Virtual Machines for Linux at the forefront, we’ve got a story to tell and some knowledge to drop, so buckle up and get ready for a journey of discovery!
With virtual machines, you can run multiple operating systems on a single physical server, creating isolated environments for testing, development, and deployment. It’s like having multiple laptops in one, but without the clutter and expense.
Types of Virtual Machines for Linux
In the realm of virtualization, Linux has numerous types of virtual machines that cater to various needs and use cases. From monolithic to microkernel-based architectures, each type has its unique characteristics and advantages.
Linux virtual machines fall into two primary categories: monolithic and microkernel. Monolithic virtual machines, such as VMware and KVM, have a single, self-contained kernel that manages the entire virtual machine environment.
A monolithic virtual machine consists of:
- The Guest OS (Linux in this case)
- The Host OS (the system running the virtual machine)
- The Virtual Machine Monitor (VMM), which manages the guest OS, including the emulation of hardware
On the other hand, microkernel-based virtual machines, such as Xen, have a small, lightweight kernel that handles only essential tasks, delegating other responsibilities to domain-specific modules.
A microkernel-based virtual machine consists of:
- The Microkernel
- The Domain 0 (the management domain)
- The Device Driver Domain
- The Guest OS (Linux)
In terms of performance, monolithic virtual machines tend to be more efficient, especially for single-VM scenarios. However, microkernel-based architectures can offer better scalability and flexibility in multi-VM environments.
Examples of virtual machine architectures include:
* VMware’s ESXi, a monolithic-type VMM
* KVM (Kernel-based Virtual Machine), another monolithic VMM
* Xen, a microkernel-based VMM
* VirtualBox, a hybrid monolithic-microkernel architecture
Here is a comparison of the performance of different virtual machine types:
| Virtual Machine Type | Guest OS Switching Time | VM Boot Time |
| — | — | — |
| VMware ESXi | 5-10 ms | 1-2 minutes |
| KVM | 3-6 ms | 30 seconds to 1 minute |
| Xen | 2-5 ms | 10-30 seconds |
Note: These values are approximate and may vary depending on the specific hardware and configuration.
Monolithic virtual machines, such as VMware and KVM, tend to have lower guest OS switching times and slightly longer VM boot times compared to microkernel-based architectures like Xen.
Microkernel-based virtual machines, such as Xen, have faster guest OS switching times and shorter VM boot times, making them more suitable for multi-VM environments.
However, these differences may not be significant in most use cases, and the choice of virtual machine type ultimately depends on specific requirements and needs.
Creating Virtual Machines for Linux
Creating a new virtual machine in Linux is a straightforward process that can be achieved using a variety of tools, each with its own set of features and capabilities. In this section, we will explore the process of creating a virtual machine in Linux, the tools used for this purpose, and provide step-by-step instructions for creating a virtual machine.
Tools for Creating Virtual Machines
There are several tools available for creating virtual machines in Linux, each with its own strengths and weaknesses. Some of the most popular tools include libvirt, VirtualBox, and KVM. Libvirt is a virtualization framework that provides a common interface for managing virtual machines, while VirtualBox is a virtualization software that allows users to create and run virtual machines on a variety of platforms. KVM, on the other hand, is a kernel-based virtual machine that allows users to create and run virtual machines directly on the Linux kernel.
Creating a Virtual Machine with libvirt
libvirt is a popular tool for creating and managing virtual machines in Linux. To create a new virtual machine using libvirt, follow these steps:
* Install the libvirt package on your Linux system using the package manager.
* Use the virsh command to create a new virtual machine. The virsh command has several options for creating a new virtual machine, including the `create` option, which creates a new virtual machine from a disk image, and the `import` option, which imports a previously created virtual machine.
* Use the `virsh create` command to create a new virtual machine from a disk image. The `virsh create` command takes the disk image file name as an argument and creates a new virtual machine using the disk image.
virsh create Options
The `virsh create` command has several options that can be used to customize the creation of a new virtual machine. Some of the most useful options include:
* `-a` option, which specifies the disk image file name.
* `-c` option, which specifies the name of the virtual machine.
* `-v` option, which specifies the virtual machine’s operating system.
* `-d` option, which specifies the virtual machine’s boot device.
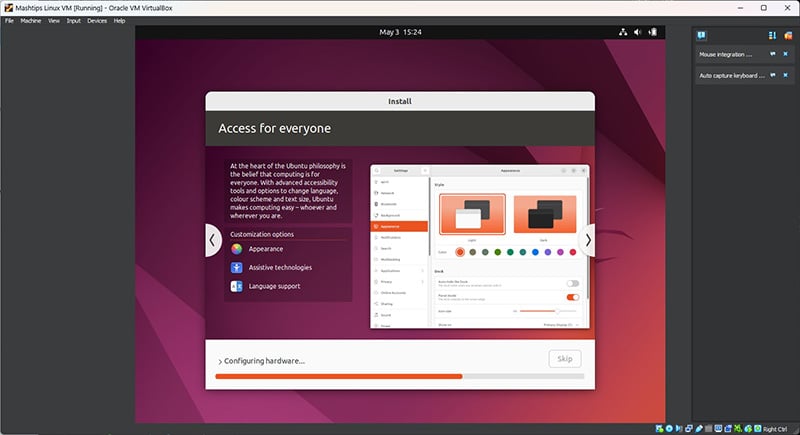
Creating a Virtual Machine with VirtualBox
VirtualBox is another popular tool for creating and managing virtual machines in Linux. To create a new virtual machine using VirtualBox, follow these steps:
* Install the VirtualBox package on your Linux system using the package manager.
* Launch the VirtualBox application and click on the “New” button to create a new virtual machine.
* Enter the name and operating system of the virtual machine, and select the disk image file from the file system.
* Configure the virtual machine’s settings, including the amount of RAM and CPU allocated to the virtual machine, and the network settings.
* Start the virtual machine and boot it from the disk image.
VirtualBox Virtual Machine Settings
VirtualBox has several options for customizing the settings of a virtual machine. Some of the most useful options include:
* “System” section, which allows users to specify the virtual machine’s operating system and boot device.
* “Motherboard” section, which allows users to specify the virtual machine’s CPU and memory settings.
* “Hard Disks” section, which allows users to specify the virtual machine’s disk image file.
* “Network” section, which allows users to specify the virtual machine’s network settings.
Creating a Virtual Machine with KVM
KVM is a kernel-based virtual machine that allows users to create and run virtual machines directly on the Linux kernel. To create a new virtual machine using KVM, follow these steps:
* Install the KVM package on your Linux system using the package manager.
* Use the `qemu-img` command to create a new disk image file for the virtual machine.
* Use the `qemu-system` command to create a new virtual machine from the disk image file. The `qemu-system` command has several options for customizing the creation of a new virtual machine, including the `-m` option, which specifies the amount of RAM allocated to the virtual machine, and the `-cpu` option, which specifies the virtual machine’s CPU settings.
KVM Virtual Machine Settings
KVM has several options for customizing the settings of a virtual machine. Some of the most useful options include:
* `-m` option, which specifies the amount of RAM allocated to the virtual machine.
* `-cpu` option, which specifies the virtual machine’s CPU settings.
* `-smp` option, which specifies the number of CPU cores allocated to the virtual machine.
* `-device` option, which specifies the virtual machine’s network settings.
Virtual Machine Networking in Linux
Virtual machine networking in Linux is crucial for providing isolated networks for each virtual machine (VM). This isolation ensures that VMs do not interfere with each other’s network activity, improving overall system security and performance.
Different Networking Options for Virtual Machines
Linux provides various networking options for virtual machines, each with its own strengths and use cases. These options include Network Address Translation (NAT), bridging, and port forwarding.
NAT (Network Address Translation)
NAT is a networking technique that allows multiple VMs to share a single IP address. This is achieved by translating the source IP address of each packet to a different IP address. For instance, VM1 can be assigned the IP address 192.168.1.10, and when it sends a packet, the NAT function translates the source IP address to the host machine’s IP address.
- NAT is a good choice for development and testing environments, where multiple VMs need to share a single IP address.
- NAT can help protect VMs from external attacks by hiding their IP addresses.
- NAT can lead to performance issues if not configured properly, as it introduces an additional layer of processing.
Bridging
Bridging is a method of connecting VMs to the host machine’s network interface. This allows VMs to share the same IP address as the host machine and can be used for servers or virtual appliances. However, bridging requires careful configuration to avoid IP address conflicts between VMs and the host machine.
- Bridging is suitable for server VMs or virtual appliances that require direct access to the host machine’s network.
- Bridging can be more complex to set up than NAT and requires careful configuration to avoid IP address conflicts.
Port Forwarding
Port forwarding is a method of mapping a VM’s IP address and port number to a different IP address and port number. This allows external connections to be forwarded to a VM, even if the VM is not directly accessible from the host machine.
- Port forwarding is useful for applications that require external connections, such as web servers or databases.
- Port forwarding can introduce security risks if not configured properly, as it allows external access to VMs.
Use of NAT, Bridging, and Port Forwarding in Real-World Scenarios
In real-world scenarios, the choice of networking option depends on the specific requirements of each VM. For instance, a development environment might use NAT for testing purposes, while a server VM might require bridging for direct access to the host machine’s network. Port forwarding can be used in scenarios where external connections are necessary.
Comparison of Networking Configurations
The choice of networking configuration depends on specific requirements, such as security, performance, and ease of use. NAT is generally a good choice for development and testing environments, while bridging is more suitable for server VMs or virtual appliances. Port forwarding should be used sparingly, as it introduces security risks if not configured properly.
Virtual Machine Security for Linux
Virtual machine security is a top priority for any Linux administrator, as virtual machines (VMs) can pose unique security risks. With the flexibility to run multiple operating systems and applications on a single physical host, VMs can also create opportunities for attackers to exploit vulnerabilities and gain unauthorized access to sensitive data.
When a virtual machine is compromised, the entire host system is at risk, as the attacker could potentially move laterally across the network. This is why it’s essential to implement robust security measures to protect virtual machines and maintain the integrity of the host system.
The Security Risks Associated with Virtual Machines
Security risks associated with virtual machines in Linux include:
- Privilege Escalation: Attackers can exploit vulnerabilities in the guest operating system or virtualization software to gain elevated privileges, allowing them to access sensitive data or perform malicious actions.
- Network Exploitation: Virtual machines can be used as a pivot point for network attacks, allowing attackers to move laterally across the network and exploit vulnerabilities in other systems.
- Data Theft: Virtual machines can be used to steal sensitive data, such as encryption keys, passwords, or other confidential information.
- Malware and Ransomware: Virtual machines can be used to spread malware and ransomware across the network, causing significant disruptions and financial losses.
These security risks highlight the importance of implementing robust security measures to protect virtual machines and maintain the integrity of the host system.
Best Practices for Securing Virtual Machines
To ensure the security of virtual machines in Linux, follow these best practices:
- Use Secure Virtualization Software: Choose a reputable virtualization software, such as VMware or KVM, that provides robust security features, including encryption and access controls.
- Implement Network Segmentation: Segment the virtual network to prevent lateral movement and contain malware or ransomware outbreaks.
- Use Strong Access Controls: Implement role-based access controls (RBAC) and ensure that all users and administrators have the minimum required privileges to perform their tasks.
- Monitor Virtual Machine Activity: Regularly monitor virtual machine activity, including system logs, network traffic, and disk usage, to detect potential security threats.
- Keep Software Up-to-Date: Regularly update and patch virtualization software, guest operating systems, and applications to prevent exploitation of known vulnerabilities.
By implementing these best practices, you can significantly reduce the risk of security breaches and maintain the integrity of your virtual machines and host system.
Security Configurations for Virtual Machines
To enhance virtual machine security, configure the virtualization software and guest operating system as follows:
- Enable Host-Only Networking: Configure the virtualization software to use host-only networking, which limits network access to the host system and prevents lateral movement.
- Enable Encryption: Enable full-disk encryption and secure boot mechanisms to prevent unauthorized access to virtual machine data.
- Configure Firewall Rules: Configure firewall rules to restrict incoming and outgoing network traffic, preventing potential security threats.
- Implement Secure Password Policies: Implement secure password policies, including password length, complexity, and expiration, to prevent unauthorized access to virtual machines.
These security configurations can significantly enhance the security of your virtual machines and protect against potential security threats.
The Role of Access Control in Virtual Machine Security
Access control plays a crucial role in virtual machine security, as it determines who can access, create, modify, or delete virtual machines and their associated resources.
- Role-Based Access Control (RBAC): Implement RBAC to restrict user access to virtual machines based on their roles and privileges.
- Attribute-Based Access Control (ABAC): Implement ABAC to restrict access to virtual machines based on specific attributes, such as user ID, group ID, or file access control lists.
- MAC (Mandatory Access Control): Implement MAC to restrict access to virtual machines based on specific security labels, ensuring that sensitive data is protected.
By implementing robust access controls, you can ensure that virtual machines are only accessible to authorized personnel and prevent potential security breaches.
Virtual Machine Best Practices for Linux
Virtual machine best practices for Linux ensure efficient and secure usage of virtual machines in a Linux environment. Proper configuration and management are crucial for reliable and scalable virtual machine operations.
Optimal Virtual Machine Configuration
Optimal virtual machine configuration includes allocating sufficient resources, such as CPU, memory, and storage, for each virtual machine based on its requirements. Over- or under- allocation can result in performance issues or inefficient utilization of system resources.
- Assign a sufficient amount of CPU resources to the virtual machine, taking into account the workload and application requirements.
- Allocate memory resources based on the memory requirements of the operating system and applications running within the virtual machine.
- Ensure sufficient storage capacity for the virtual machine, considering the file system size and data storage requirements.
Virtual Machine Backup and Disaster Recovery, Virtual machines for linux
Regular virtual machine backups and disaster recovery plans are essential for minimizing data loss and business disruption in case of system failures or data corruption. Proper backup strategies ensure smooth recovery and minimize downtime.
- Establish a regular backup schedule for virtual machines, including incremental backups and full backups.
- Use a reliable backup software that supports virtual machine backups, such as rsync or duplicati.
- Store backup data on a separate physical storage device or in a remote location to ensure data availability.
Troubleshooting Virtual Machines
Troubleshooting virtual machines involves identifying and resolving issues related to performance, availability, and data integrity. Effective troubleshooting requires a systematic approach and expertise in virtual machine management.
- Identify and isolate the issue: Determine the symptoms, scope, and root cause of the issue.
- Analyze and diagnose: Gather data, logs, and other relevant information to determine the cause of the issue.
- Apply fixes or patches: Resolve the issue by applying fixes, patches, or updates to the operating system, applications, or virtual machine configuration.
Virtual Machine Documentation
Accurate and up-to-date documentation of virtual machines provides valuable information for future reference, troubleshooting, and knowledge sharing within the organization. Proper documentation ensures efficient and reliable virtual machine operations.
- Maintain a record of virtual machine creation, configuration, and modifications.
- Document operating system and application versions, including software and patch versions.
- Keep a record of backup schedules, backup data, and disaster recovery procedures.
Ending Remarks
We’ve reached the end of our journey, but don’t worry, we’ve only just scratched the surface. Virtual Machines for Linux offer a world of possibilities, and with the right tools and knowledge, you can unlock its full potential.
FAQ Corner: Virtual Machines For Linux
Q: What is the difference between virtualization and containerization? A: Virtualization creates a new, standalone operating system for each virtual machine, while containerization runs multiple applications on a single operating system.
Q: What are the benefits of using virtual machines in a Linux environment? A: Virtual machines offer flexibility, scalability, and security, making them ideal for development, testing, and deployment.
Q: How do virtual machines communicate with the host operating system? A: Virtual machines use virtual networking options like NAT, bridging, and port forwarding to communicate with the host operating system.
Q: What are some best practices for securing virtual machines? A: Regularly update and patch virtual machine operating systems, use strong passwords, and enable access control lists to protect against unauthorized access.