How to install virtual machine –
As how to install virtual machine takes center stage, this comprehensive guide is crafted with good knowledge to ensure a reading experience that is both absorbing and distinctly original, walking readers through the process with clarity and humor.
For those who want to create a virtual machine, this installation process needs to be considered, including choosing a hypervisor, system requirements, and setting up virtual machine settings and managing them for optimal performance.
With this guide, you’ll learn how to create and maintain a virtual machine, ensuring a seamless and efficient experience.
Installing Hypervisor Software
Installing hypervisor software is a crucial step in setting up a virtual machine environment. Hypervisors are software applications that create and manage virtual machines on a physical host machine, allowing for efficient resource utilization and improved scalability. In this section, we will guide you through the process of installing hypervisor software on different operating systems, including Windows, Linux, and macOS.
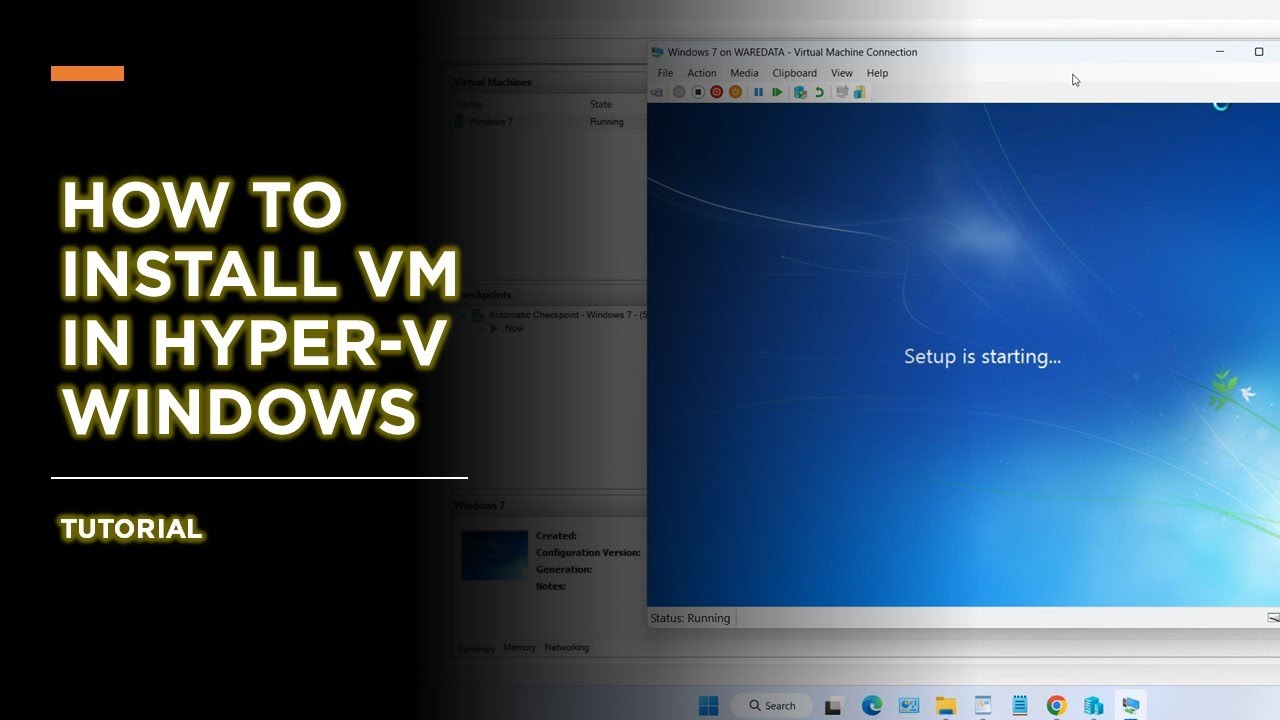
Installing Hypervisor Software on Windows
Installing a hypervisor on a Windows host involves the following steps:
- Ensure that your computer meets the system requirements for the hypervisor software, including sufficient RAM and processor speed.
- Download the hypervisor software from its official website or obtain it through a third-party source.
- Run the installer and follow the on-screen instructions to complete the installation process.
- During installation, you may be prompted to disable or uninstall any other virtualization software that is currently installed on your system.
- Once the installation is complete, restart your computer to apply the changes.
- Launch the hypervisor software and create a new virtual machine by specifying the operating system, memory, CPU, and other settings as required.
Hypervisor software for Windows includes options such as Hyper-V, VMware Workstation, and VirtualBox.
Installing Hypervisor Software on Linux
Installing a hypervisor on a Linux host can be done using the following steps:
- Install the necessary packages and prerequisites, depending on the Linux distribution you are using.
- Download the hypervisor software from its official repository or compile it from source.
- Configure the hypervisor software to match your system’s architecture and settings.
- Initialize the hypervisor with the command to start the virtual machine manager.
- Create new virtual machines using the hypervisor software and configure them as required.
Popular hypervisor software for Linux includes KVM, Xen, and VMware Server.
Installing Hypervisor Software on macOS
Installing a hypervisor on a macOS host requires careful configuration and installation:
- macOS has built-in virtualization software called Hypervisor Framework, which can be used to create virtual machines.
- Use the command line to create a new virtual machine and set the required settings, including memory and CPU allocation.
- Once the virtual machine is created, it can be managed and configured as required.
- Note that macOS-specific hypervisors are limited compared to other operating systems.
Differences in Installing Hypervisors on Mac vs. PC
Although the overall installation process is similar across different operating systems, there are differences in the specific steps and requirements for each platform:
- System architecture and compatibility issues may arise when installing hypervisor software on macOS compared to Windows or Linux.
- macOS users typically use the command line to interact with hypervisor software, whereas Windows and Linux users can use graphical user interfaces.
- macOS has specific hardware requirements for virtualization, including a Core i5 or i7 processor and a minimum of 8 GB RAM.
- Hypervisor software availability and functionality may be limited on certain platforms, such as macOS.
Understanding these differences is crucial for successful hypervisor installation and operation across various operating systems.
Creating Virtual Machines: How To Install Virtual Machine
Creating a virtual machine from scratch is a straightforward process that allows you to create a self-contained virtual environment that replicates a physical machine’s hardware, but without the costs and complexities associated with installing a physical server.
To create a new virtual machine, you’ll need to follow these steps: allocate storage space for the virtual machine, choose the operating system, configure networking settings, and select the virtual hardware requirements.
Allocating Resources to a Virtual Machine
When creating a virtual machine, one of the most critical steps is allocating resources such as CPU, memory, and storage. These resources determine the performance and capabilities of your virtual machine.
- Processor (CPU): Assign a sufficient number of CPU cores to ensure the virtual machine receives enough processing power to run resource-intensive applications smoothly. Typically, you would assign between 2-8 CPU cores, depending on the type of workload you anticipate running on the VM.
CPU Cores: The number of CPU cores allocated to a virtual machine determines the performance of the machine.
- Memory (RAM): Allocate sufficient RAM to ensure your virtual machine has enough memory to perform demanding tasks. A general rule of thumb is to allocate at least 4 GB of RAM for general-purpose computing, but this can vary greatly depending on the workload.
- Storage: Select a storage option such as a virtual hard disk or solid-state drive (SSD). Allocate sufficient storage space, depending on the operating system and applications you plan to install on the virtual machine.
- Network Settings: Configure networking settings, including selecting the virtual network adapter, specifying the network settings, and setting any necessary security protocols.
When allocating resources, it is essential to consider the minimum requirements for the operating system and applications you plan to install on the virtual machine. Additionally, be sure to leave some headroom for growth and scalability.
Configuring Virtual Hardware, How to install virtual machine
In addition to allocating resources, you’ll also need to configure the virtual hardware settings, such as the virtual IDE controller, IDE channels, and SATA settings.
- Virtual IDE Controller: Configure the virtual IDE controller, specifying the number of IDE channels and IDE settings.
- IDE Channels: Allocate IDE channels for your virtual machine’s hard disk drives.
- SATA Settings: Configure SATA settings, including selecting the number of SATA ports and specifying the settings for each port.
In conclusion, creating a virtual machine involves allocating resources, configuring virtual hardware settings, and selecting the operating system and applications to be installed.
Configuring Virtual Machine Settings

Configuring the settings of your virtual machine is crucial for ensuring that it functions smoothly and efficiently. By tweaking the network, disk, and display settings, you can optimize the performance of your VM and tailor it to your specific needs.
VM Networking Options
When it comes to configuring the network settings of your virtual machine, you have several options to choose from. These include NAT (Network Address Translation), Bridged, and Host-only networking.
– NAT is ideal for scenarios where you want to allow the VM to access the internet but still maintain a degree of isolation. This can be useful for testing and development purposes, as it allows you to simulate a real-world environment without exposing your host machine to potential threats.
– Bridged networking, on the other hand, provides the VM with direct access to the network, making it virtually indistinguishable from a physical machine. This is often preferred for gaming, video editing, and other resource-intensive applications that require a seamless network experience.
– Host-only networking is the most secure option, as it limits the VM’s access to only the host machine and any other VMs on the same network. This is typically used for testing and development purposes, as it provides an isolated environment for experimentation without exposing sensitive data to the outside world.
When selecting a networking option, consider the purpose of your VM and the level of isolation you need.
Optimizing VM Performance
In addition to adjusting the network settings, there are several other ways to optimize the performance of your virtual machine. These include:
– Allocating sufficient RAM and CPU resources to the VM. A general rule of thumb is to allocate at least 2 GB of RAM for a standard VM.
– Enabling virtualization extensions (VT-x or AMD-V) on your host machine’s processor.
– Using a high-performance disk imaging format, such as VDI or VMDK.
– Enabling hardware-accelerated graphics for improved 3D performance.
– Regularly updating the VM’s guest operating system and drivers.
Proper configuration of VM settings can make a significant difference in its overall performance and efficiency.
Virtual Machine Security and Compliance
In today’s virtualized world, security and compliance play a crucial role in protecting virtual machines and their underlying infrastructure. With virtual machines (VMs) storing sensitive data and applications, ensuring their security and compliance is of utmost importance. This chapter will delve into the security implications of running VMs, explore compliance considerations, and Artikel measures to implement security measures in virtual machines.
Security Implications of Running VMs
Running virtual machines introduces unique security risks that can compromise the integrity of the virtualized environment. Some of these risks include:
Firewalls and antivirus software are crucial in mitigating these risks, but they must be properly configured to ensure they are effective.
- Faulty configuration of network settings, allowing unauthorized access to sensitive data
- Insufficient patching of virtual machine operating systems, leaving vulnerabilities open to exploitation
- Malware infections that can spread to other virtual machines on the same host
- Unauthorized access to virtual machines through stolen or compromised admin credentials
- Denial of Service (DoS) attacks that can crash or slow down virtual machines
To mitigate these risks, IT administrators must regularly monitor virtual machines for signs of unusual activity, implement robust security measures, and conduct regular security audits to identify and remediate vulnerabilities.
Compliance Considerations for Virtualized Environments
Compliance with regulatory requirements is a critical aspect of virtualized environments. Some of the key compliance considerations include:
The General Data Protection Regulation (GDPR), the Health Insurance Portability and Accountability Act (HIPAA), and the Payment Card Industry Data Security Standard (PCI DSS) are just a few examples of regulatory requirements that must be met in virtualized environments.
- Ensuring data confidentiality, integrity, and availability, as mandated by GDPR
- Implementing HIPAA-compliant security measures to protect sensitive patient data
- Meeting PCI DSS requirements for secure processing and storage of credit card information
- Conducting regular audits to ensure adherence to regulatory requirements
- Developing and implementing incident response plans to address security breaches
By prioritizing compliance, organizations can minimize the risk of non-compliance fines, reputational damage, and data breaches.
Implementing Security Measures in Virtual Machines
To ensure the security and compliance of virtual machines, IT administrators must implement robust security measures. Some of these measures include:
Firewalls, intrusion detection and prevention systems, and antivirus software are just a few examples of security measures that can be implemented in virtual machines.
- Implementing firewalls to restrict incoming and outgoing traffic
- Configuring intrusion detection and prevention systems to monitor network traffic for suspicious activity
- Installing antivirus software to detect and remove malware
- Enforcing strong passwords and multi-factor authentication
- Implementing disk encryption to protect data at rest
By implementing these security measures, organizations can ensure the security and compliance of their virtual machines and protect their sensitive data and applications.
Creating Virtual Machines: How To Install Virtual Machine
Creating a virtual machine (VM) is a crucial step in setting up a virtualization environment. A VM is a self-contained virtualized computer that runs its own operating system and applications, allowing you to run multiple operating systems on a single physical machine. To create a VM from scratch, you’ll need to follow a few steps.
Allocating Resources to a VM
When creating a VM, you’ll need to allocate resources such as CPU cores, memory, and storage to ensure it runs smoothly. The amount of resources you allocate will depend on the specific needs of your VM and the workloads it will be running.
To allocate resources to a VM, select the VM you want to configure and click on the “Edit” button. From here, you can adjust the number of CPU cores, memory, and storage allocated to the VM.
|
|
|
|
|
| — | — | — | — |
|
|
|
| The number of CPU cores allocated to the VM will determine how many tasks it can perform simultaneously. |
|
|
|
|
|
| — | — | — | — |
|
|
|
| The amount of memory allocated to the VM will determine how many applications it can run simultaneously. |
|
|
|
|
|
| — | — | — | — |
|
|
|
| The amount of storage allocated to the VM will determine how many files and applications it can store. |
When allocating resources to a VM, make sure to consider the specific needs of the workloads it will be running. Over-allocating resources can lead to performance issues, while under-allocating resources may lead to bottlenecks.
To ensure optimal performance, it’s essential to strike a balance between resource allocation and workload requirements. By allocating the correct amount of resources, you can ensure your VM runs smoothly and efficiently.
Conclusive Thoughts

To sum it up, installing a virtual machine requires careful planning and execution, but with this guide, you’ll be well-equipped to navigate the process with ease.
Remember to consider your needs, choose the right hypervisor, and configure your virtual machine settings for optimal performance.
By following these steps and staying informed, you’ll be able to create and manage virtual machines like a pro, unlocking a world of possibilities.
Key Questions Answered
What is the minimum system requirement for installing a virtual machine?
The minimum system requirements for installing a virtual machine vary depending on the hypervisor and the number of virtual machines you plan to install.
However, a general guideline is a 64-bit processor, at least 4 GB of RAM, and a decent amount of storage space.
What is the difference between a physical machine and a virtual machine?
A physical machine is a real computer that you can touch and see, while a virtual machine is a software emulation of a physical machine that runs on top of a host operating system.
Virtual machines are more flexible and scalable than physical machines and can be easily copied, moved, or deleted.
Can I install a virtual machine on a Mac?
Yes, you can install a virtual machine on a Mac using software like VMware Fusion, VirtualBox, or Parallels.
However, the installation process may vary depending on the hypervisor you choose.