Linux for virtual machine sets the stage for this enthralling narrative, offering readers a glimpse into a story that is rich in detail with casual trendy style and brimming with originality from the outset. As we embark on this journey, we will delve into the world of Linux virtual machines, exploring the types, configurations, management, and security of these digital entities.
The concept of virtual machines has revolutionized the way we interact with computing systems, providing a flexible and scalable solution for various applications, from development to production environments. Linux, with its vast array of distributions and customization options, has emerged as the premier choice for virtual machine infrastructure.
Types of Linux Virtual Machines: Linux For Virtual Machine
Linux virtual machines have become an essential tool for developers, testers, and administrators. They offer a cost-effective and flexible way to run multiple operating systems on a single host machine. In this section, we will explore the different types of Linux virtual machines and their features.
These virtualization solutions have gained popularity due to their ability to run multiple OS instances on a single physical machine. This flexibility allows users to test, develop, and deploy applications with greater ease.
Virtualization Solutions
There are several virtualization solutions available for Linux virtual machines. Each solution has its own set of features, advantages, and limitations.
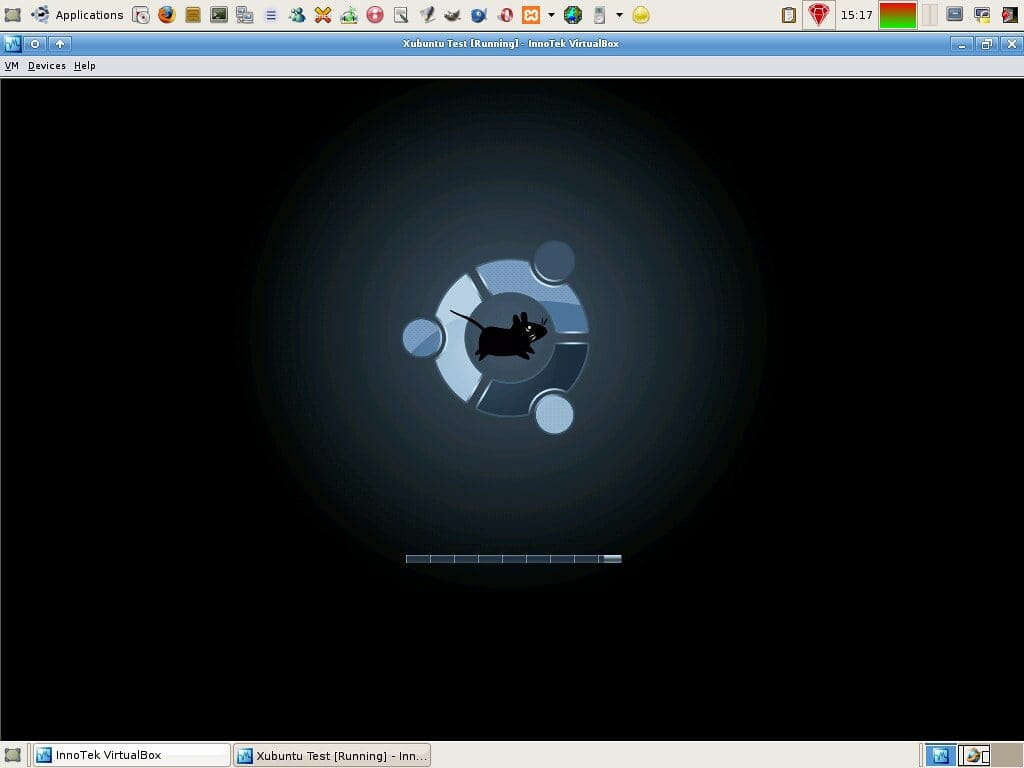
VirtualBox
VirtualBox is a popular open-source virtualization solution developed by Oracle. It supports a wide range of operating systems, including Linux, Windows, and macOS. VirtualBox provides a user-friendly interface and offers advanced features such as snapshotting, cloning, and virtual networking.
Some of the key features of VirtualBox include:
- Support for multiple operating systems: VirtualBox can run multiple OS instances on a single host machine.
- Snapshotting and cloning: VirtualBox allows users to create snapshots of their VMs and clone them to create new VMs.
- Virtual networking: VirtualBox provides support for virtual networking, which allows users to create and manage virtual networks.
- Multiplatform support: VirtualBox is available for Windows, macOS, and Linux host operating systems.
- Extensive documentation: VirtualBox provides extensive documentation and a large community of users and developers.
VirtualBox is a popular choice among developers and administrators due to its user-friendly interface and advanced features.
VMware
VMware is a commercial virtualization solution that offers a wide range of features and tools. It supports multiple operating systems and provides advanced features such as snapshotting, cloning, and virtual networking.
Some of the key features of VMware include:
- Support for multiple operating systems: VMware can run multiple OS instances on a single host machine.
- Snapshotting and cloning: VMware allows users to create snapshots of their VMs and clone them to create new VMs.
- Virtual networking: VMware provides support for virtual networking, which allows users to create and manage virtual networks.
- Multiplatform support: VMware is available for Windows, macOS, and Linux host operating systems.
- Enhanced security features: VMware provides enhanced security features, including encryption and access controls.
VMware is a popular choice among businesses due to its advanced features and robust tools.
KVM (Kernel-based Virtual Machine), Linux for virtual machine
KVM is an open-source virtualization solution that provides high-performance virtualization capabilities. It supports multiple operating systems and provides features such as snapshotting, cloning, and virtual networking.
Some of the key features of KVM include:
- High-performance virtualization: KVM provides high-performance virtualization capabilities, making it suitable for demanding workloads.
- Snapshotting and cloning: KVM allows users to create snapshots of their VMs and clone them to create new VMs.
- Virtual networking: KVM provides support for virtual networking, which allows users to create and manage virtual networks.
- Multiplatform support: KVM is available for Linux host operating systems.
- Low overhead: KVM has a low overhead compared to other virtualization solutions.
KVM is a popular choice among Linux administrators due to its high-performance capabilities and low overhead.
Each virtualization solution has its own strengths and weaknesses, and the choice ultimately depends on the specific needs of the user.
Installing Linux on a Virtual Machine
Installing Linux on a virtual machine provides a convenient and risk-free environment to explore and learn about Linux without affecting the host machine’s operating system. This method is ideal for testing, development, and training purposes. With the right virtualization software and a suitable Linux distribution, you can create a virtual machine with a fully functional Linux environment.
Selecting the Correct Installation Medium
The installation medium determines how you will install Linux on your virtual machine. You have two options: CD/DVD or ISO file.
The ISO file is a digital copy of a CD/DVD that can be used to install Linux.
To install Linux from a CD/DVD, you need to create a virtual CD/DVD drive in your virtual machine settings. To use an ISO file, you can attach it to the virtual machine as a CD/DVD device and then follow the installation process from the ISO file.
- Use a CD/DVD drive if you prefer to have a physical installation media or if your virtual machine software does not support ISO files.
- Choose an ISO file if you prefer to have a digital installation media or if you want to avoid the hassle of burning a CD/DVD.
- Download a Linux ISO file from a reputable source, such as the official Linux distribution website.
Configuring Virtual Machine Settings
To run Linux on a virtual machine, you need to configure the virtual machine settings, including CPU, memory, and network.
Properly configuring these settings ensures optimal performance and a smooth user experience.
To configure the virtual machine settings:
- Assign a minimum of 2 GB of RAM and 2 CPU cores to the virtual machine.
- Ensure that the virtual machine has access to a network, either through a bridge network or a virtual network interface.
- Configure the virtual machine to use a suitable CPU architecture, such as 64-bit or 32-bit, depending on the Linux distribution you are using.
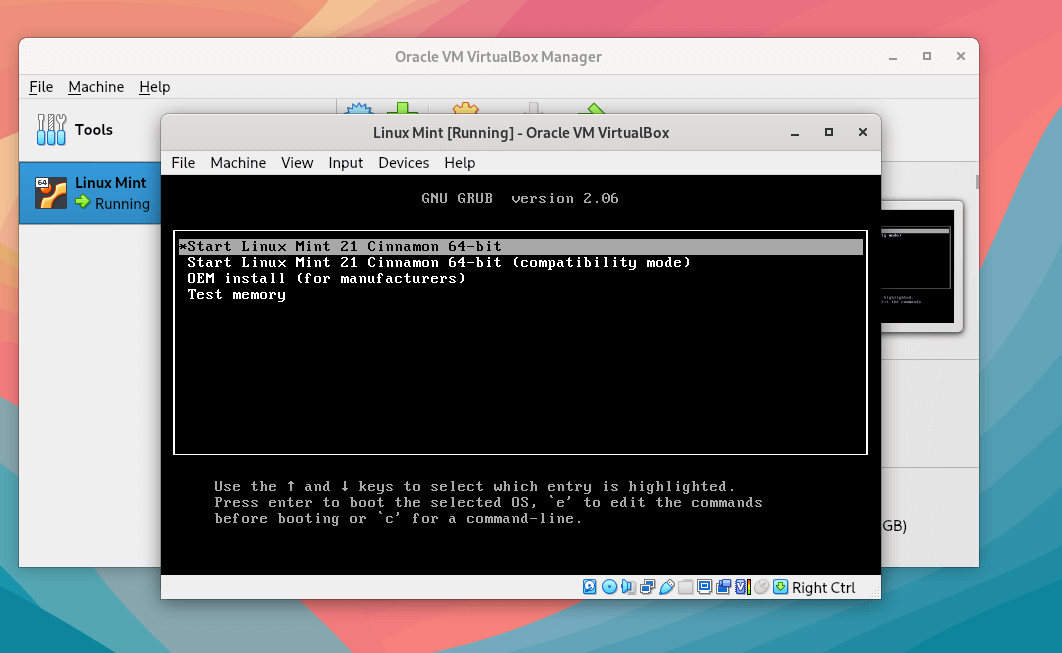
Installing Linux on the Virtual Machine
Once you have selected the correct installation medium and configured the virtual machine settings, you can start the installation process. Follow the installation wizard to install Linux on the virtual machine.
- Start the virtual machine and boot from the installation media.
- Follow the installation wizard to select the language, keyboard layout, and time zone.
- Select the partition scheme and install Linux on the virtual machine.
- Configure the network and other settings as needed.
- Start the virtual machine and login to your new Linux environment.
Configuring Linux Virtual Machines
Configuring Linux virtual machines is a crucial step in ensuring they run smoothly and efficiently. It involves setting up various components such as network settings, storage, and security.
With Linux virtual machines, you can configure network settings to suit your needs. The three main options for network settings are bridged, NAT (Network Address Translation), and host-only.
###
Configuring Network Settings
Configuring network settings allows you to control how your virtual machine interacts with the physical network. You can choose from three main options: bridged, NAT, and host-only.
-
Bridged networking connects your virtual machine directly to the physical network. This allows your virtual machine to communicate with other devices on the network, just like a physical machine.
-
NAT (Network Address Translation) networking assigns a private IP address to your virtual machine, allowing it to communicate with the physical network while keeping your private network hidden from the outside.
-
Host-only networking connects your virtual machine to the physical machine’s network stack, but no other devices on the physical network can communicate with your virtual machine.
When choosing a network setting, consider the requirements of your virtual machine and the security level you want to maintain.
###
Setting up SSH and Other Network Services
To set up SSH and other network services, you will need to configure the network settings of your virtual machine. Follow these steps:
1. Ensure your virtual machine is configured to use a bridged, NAT, or host-only network setting.
2. Set up a static IP address for your virtual machine.
3. Configure the SSH server to listen on a specific port.
4. Test the SSH connection from your host machine to your virtual machine.
###
Configuring Storage Settings
Configuring storage settings is crucial for setting up your virtual machine’s file system. You can configure storage settings to suit your needs, including virtual hard disk and CD/DVD drives.
####
Virtual Hard Disk
A virtual hard disk is a file that simulates a physical hard drive. You can create a virtual hard disk using various formats such as VMDK, VDI, or VHD.
– Fixed-size hard disk: Allocates a fixed amount of space on the host machine’s disk.
– Dynamic hard disk: Allocates space as needed, but may lead to fragmentation.
– Thin-provisioned hard disk: Allocates space only when data is written, reducing the risk of fragmentation.
####
CD/DVD Drives
A CD/DVD drive in a virtual machine is a virtual device that allows you to mount and access CDs or DVDs.
– Host drive: Allows access to the host machine’s CD/DVD drive.
– ISO file: Allows mounting of ISO files.
###
Creating Snapshots and Cloning Virtual Machines
Snapshots and cloning allow you to create copies of your virtual machine at a certain point in time.
###
Creating Snapshots
A snapshot is a copy of the current state of the virtual machine. You can create a snapshot at any point in time and revert back to that point later.
###
Cloning Virtual Machines
Cloning creates a new virtual machine that is an exact copy of the original.
Cloning can be useful if you need to create a new machine with the same settings and configuration. However, note that it may still have a different UUID (Universally Unique Identifier).
Managing Linux Virtual Machines
Managing Linux virtual machines requires a deep understanding of the operating system’s intricacies and the virtualization software being used. Effective management enables system administrators to optimize performance, troubleshoot issues, and ensure the security and integrity of the virtual environment.
Viewing Resource Utilization and Performance Metrics
To manage and monitor Linux virtual machines, it is crucial to have real-time visibility into system resource utilization, including CPU, memory, and disk usage. This can be achieved by using various command-line tools and graphical interfaces:
- The
topcommand provides a real-time view of system processes, CPU usage, and memory consumption. - The
freecommand offers information on memory and disk usage. - The
htopcommand, an interactive version oftop, allows for more in-depth analysis and filtering of system processes. - The
xrdpandrdpcommands facilitate remote access to graphical consoles and enable system administrators to monitor virtual machine performance from anywhere.
Taking and Restoring Snapshots
Snapshots are a vital feature in virtualization, allowing system administrators to capture the state of a virtual machine at a particular point in time. This feature is particularly useful for backup and disaster recovery purposes. The process of taking and restoring snapshots involves:
- Using the virtualization software’s built-in snapshot tool, such as VMware vCenter Converter or VirtualBox.
- Creating a snapshot by freezing the virtual machine’s state, which includes the RAM, disk, and other system settings.
- Restoring a snapshot by reverting the virtual machine to its previous state.
Cloning and Creating Templates
Cloning and creating templates are essential for efficiently managing Linux virtual machines. Cloning involves creating a duplicate of an existing virtual machine, while creating templates involves creating a snapshot of a virtual machine that can be used to create new virtual machines. The benefits of cloning and creating templates include:
- Streamlining the virtual machine creation process by reusing existing configurations.
- Ensuring consistency across multiple virtual machines by standardizing configurations.
- Improving efficiency by reducing the amount of manual configuration required.
A well-managed Linux virtual machine environment can significantly improve performance, reduce downtime, and enhance overall system security.
Linux Virtual Machine Security
Securing Linux virtual machines is crucial to protect sensitive data and prevent potential security threats. A compromised virtual machine can have severe consequences, including data breaches, unauthorized access, and disruptions to critical services. To mitigate these risks, it is essential to implement robust security measures and follow best practices for managing and monitoring Linux virtual machines.
Setting Strong Passwords
A strong password is the first line of defense against unauthorized access to a Linux virtual machine. To ensure the security of your virtual machine, you should set strong passwords for all users, including the root account. A strong password should meet the following criteria:
- Be at least 8 characters long
- Contain a mix of uppercase and lowercase letters
- Include numbers and special characters
- Be unique and not easily guessable
It is recommended to use a password manager to generate and store complex passwords. Avoid using common passwords or easily guessable information, such as your name or birthdate.
Restricting Access to Sensitive Files
Linux virtual machines often store sensitive data, such as database credentials, encryption keys, and confidential documents. To prevent unauthorized access to these files, you should implement restrictive file permissions and access controls. Use the following techniques to limit access to sensitive files:
- Use the umask command to set default file permissions
- Use the chown command to change file ownership and permissions
- Use the chmod command to modify file permissions
- Use access control lists (ACLs) to grant or deny access to specific users or groups
By implementing restrictive file permissions and access controls, you can prevent unauthorized access to sensitive files and protect your virtual machine from potential security threats.
Implementing Firewall Rules
Firewall rules play a crucial role in securing Linux virtual machines by controlling incoming and outgoing network traffic. A well-configured firewall can prevent unauthorized access to your virtual machine, block malicious traffic, and limit the exposure of sensitive data.
blockquote>”The first thing you do when you’re dealing with a hostile environment is to set up a firewall.” – Linus Torvalds
To implement firewall rules, you can use the iptables command or a firewall management tool like ufw. Create rules to:
- Block incoming traffic on unnecessary ports and services
- Allow outgoing traffic to essential services and destinations
- Implement stateful packet inspection to detect and block malicious traffic
By implementing firewall rules, you can enhance the security of your Linux virtual machine and prevent potential security threats.
Monitoring and Analyzing System Logs
System logs provide valuable information about security incidents, errors, and other events occurring on your Linux virtual machine. To detect potential security threats and prevent data breaches, you should regularly monitor and analyze system logs. Use the following tools to collect and analyze system logs:
- syslog-ng
- logrotate
- grep
- awk
By monitoring and analyzing system logs, you can:
- Identify potential security threats and vulnerabilities
- Detect and respond to security incidents
- Optimize system performance and reduce errors
Regularly monitoring and analyzing system logs is essential to maintaining a secure and reliable Linux virtual machine.
Linux Virtual Machine Backup and Recovery
Linux virtual machines are crucial components of modern IT infrastructure, and their availability, reliability, and security cannot be compromised. Therefore, it is essential to implement robust backup and recovery strategies to ensure that these virtual machines are always up and running.
Importance of Block-Level Backups
Block-level backups are a type of backup that focuses on backing up the raw data blocks of a virtual machine’s disk, rather than individual files. This approach is highly efficient and effective for backing up large data sets, as it eliminates the need to scan and backup individual files. Block-level backups are particularly useful for virtual machines that store large amounts of data, such as databases, file servers, and video editing workstations.
Identify the virtual machine’s disk storage:This can be done by accessing the virtual machine’s settings or configuration file. The disk storage is usually located in a format such as VMDK or VDI.Use a backup tool:Select a reliable backup tool that supports block-level backups, such as Veeam or Acronis. This tool will scan the virtual machine’s disk and identify the data blocks that need to be backed up.Configure the backup job:Specify the virtual machine, the disk storage, and the backup frequency. The backup tool will then execute the backup job and create a consistent backup of the virtual machine’s data.
Benefits of Incremental Backups
Incremental backups are a type of backup that backs up only the changes made to a virtual machine’s data since the last full backup. This approach is highly efficient and effective for backing up large data sets, as it reduces the amount of data that needs to be backed up. Incremental backups are particularly useful for virtual machines that experience frequent changes, such as development environments, testing labs, and production servers.
Determine the backup frequency:Specify how often the incremental backup should run, such as daily or weekly.Identify the base image:Select the base image from which to perform the incremental backup. This image should be a consistent and complete backup of the virtual machine’s data.Run the incremental backup:Execute the backup job and let the tool create an incremental backup of the changes made to the virtual machine’s data since the last full backup.
Restoring from Snapshots
Snapshots are point-in-time copies of a virtual machine’s state, including its memory, disk, and network configuration. Restoring from snapshots is a highly efficient and effective way to recover a virtual machine from a previous state. This approach is particularly useful for virtual machines that experience frequent data corruption or hardware failures.
Identify the snapshot:Select the snapshot from which to restore. This snapshot should be a consistent and complete copy of the virtual machine’s state.Run the restore job:Execute the restore job and let the tool recreate the virtual machine’s state from the snapshot.Verify the restore:Once the restore job completes, verify that the virtual machine is properly restored and functioning as expected.
Cloning Virtual Machines
Cloning virtual machines is a highly efficient and effective way to create a duplicate virtual machine with the same configuration, memory, and disk settings. This approach is particularly useful for virtual machines that require identical setup, such as development environments, testing labs, and production servers.
Identify the source virtual machine:Select the virtual machine to be cloned. This virtual machine should have the desired configuration, memory, and disk settings.Run the clone job:Execute the clone job and let the tool create a duplicate virtual machine with the same configuration, memory, and disk settings.Verify the clone:Once the clone job completes, verify that the cloned virtual machine is properly created and functioning as expected.
Real World Applications of Linux Virtual Machines
Linux virtual machines have become a crucial tool in various industries due to their flexibility, scalability, and cost-effectiveness. In this section, we will explore several real-world applications of Linux virtual machines and discuss their benefits and challenges in different scenarios.
Case Study in Education
Linux virtual machines have been widely adopted in educational institutions due to their ease of use and flexibility. They enable educators to create a simulated learning environment that mimics real-world scenarios, allowing students to gain practical experience and develop essential skills.
- Simulated lab environments: Linux virtual machines enable educators to create simulated lab environments that allow students to practice and learn without the need for physical equipment. This approach reduces the financial burden on educational institutions and provides students with a safe and controlled environment to experiment and learn.
- Virtualized student workstations: Linux virtual machines can be used to create virtualized student workstations that provide students with access to a shared computing environment. This approach enables students to work on projects and assignments in a collaborative and secure manner.
- Lab automation: Linux virtual machines can be used to automate lab procedures, freeing up educators to focus on teaching and mentoring students.
Case Study in Research and Development
Linux virtual machines have become an essential tool in research and development (R&D) due to their high performance and flexibility. They enable researchers to create complex, scalable environments that can be easily duplicated and shared with colleagues.
- High-performance simulations: Linux virtual machines can be used to create high-performance simulations that enable researchers to model complex systems and phenomena. This approach has been used in various fields, including climate modeling, fluid dynamics, and materials science.
- Large-scale data analysis: Linux virtual machines can be used to perform large-scale data analysis, enabling researchers to process and analyze vast amounts of data quickly and efficiently.
- Collaborative environments: Linux virtual machines can be used to create collaborative environments that enable researchers to work together on projects and share resources.
Case Study in Development and Deployment
Linux virtual machines have become an essential tool in development and deployment due to their flexibility and scalability. They enable developers to create and test complex systems and applications quickly and efficiently.
- DevOps environments: Linux virtual machines can be used to create DevOps environments that enable developers to test and deploy applications quickly and efficiently.
- Continuous Integration and Continuous Deployment (CI/CD): Linux virtual machines can be used to implement CI/CD pipelines that enable developers to automate the testing and deployment of applications.
- Cloud-native applications: Linux virtual machines can be used to create cloud-native applications that are scalable, secure, and highly available.
Benefits and Challenges
Linux virtual machines offer several benefits, including flexibility, scalability, and cost-effectiveness. However, they also present several challenges, including compatibility issues, security concerns, and high maintenance requirements.
- Benefits:
- Flexibility: Linux virtual machines can be easily cloned and customized to meet specific needs.
- Scalability: Linux virtual machines can be scaled up or down to meet changing requirements.
- Cost-effectiveness: Linux virtual machines can be created and managed at a lower cost than physical hardware.
- Challenges:
- Compatibility issues: Linux virtual machines may not be compatible with all hardware and software.
- Security concerns: Linux virtual machines may be vulnerable to security threats, including malware and unauthorized access.
- Maintenance requirements: Linux virtual machines require regular maintenance, including updates and patching.
Future Development and Trends
The adoption of Linux virtual machines is expected to continue growing in various industries, driven by their flexibility, scalability, and cost-effectiveness. Future developments and trends include the use of Linux virtual machines in Edge computing, AI, and IoT applications.
Edge Computing
Linux virtual machines can be used to create Edge computing environments that enable data processing and analysis at the edge of the network, reducing latency and improving performance.
AI and Machine Learning
Linux virtual machines can be used to create AI and machine learning environments that enable developers to train and deploy AI models quickly and efficiently.
IoT and Embedded Systems
Linux virtual machines can be used to create IoT and embedded systems environments that enable developers to create and manage complex systems and applications quickly and efficiently.
Best Practices for Using Linux Virtual Machines
When working with Linux virtual machines, having a solid understanding of the best practices is essential for ensuring smooth operation, efficient resource utilization, and robust security. By following these guidelines, you can avoid common pitfalls and make the most out of your virtualization efforts.
Choosing the Correct Software
When selecting a virtualization software, consider your specific needs and the type of Linux distribution you’re planning to use. Some popular options include
- VirtualBox, which offers a wide range of features and is available for multiple platforms.
- KVM, an open-source solution that’s particularly suitable for Linux systems.
- VMware, a powerful option with strong security features and high performance capabilities.
Each of these options has its strengths and weaknesses, and choosing the right one for your needs can greatly impact your overall experience.
Configuring Hardware
When configuring your virtual hardware, it’s essential to strike a balance between performance and resource utilization. Consider the following points:
- Assigning sufficient RAM to your VM: Ensure that you allocate enough memory to match the requirements of your Linux distribution and applications. Insufficient RAM can lead to slow performance or even crashes.
- Choosing the correct CPU settings: Selecting the right CPU mode (e.g., VT-x or AMD-V) and allocating sufficient CPU resources can significantly impact performance.
- Setting up storage: Decide on the storage type and allocation for your VM, considering factors such as speed, capacity, and durability.
Proper configuration of your virtual hardware can greatly impact your virtual machine’s performance and overall usability.
Managing Virtual Machines
Effective management of your virtual machines is crucial for maintaining a smooth operation and ensuring security. Consider the following strategies:
- Monitoring resource utilization: Regularly check your VM’s resource usage to identify potential bottlenecks or areas for optimization.
- Implementing backup and recovery procedures: Develop a robust backup and recovery plan to protect your VM’s data and ensure business continuity.
- Enforcing security best practices: Regularly update your VM’s software, configure firewalls, and use strong passwords to prevent unauthorized access.
Proper management of your virtual machines can help prevent issues, ensure security, and optimize resource utilization.
Troubleshooting Common Issues
When issues arise with your virtual machines, it’s essential to approach troubleshooting in a methodical and efficient manner. Consider the following strategies:
- Reviewing system logs: Analyzing system logs can provide valuable insights into potential causes of issues.
- Checking for updates: Ensuring your VM’s software is up-to-date can resolve many common issues.
- Disabling unnecessary services: Identifying and disabling unnecessary services can help prevent conflicts and improve performance.
By employing these best practices and strategies, you can minimize the risk of common issues and ensure a smooth operation for your Linux virtual machines.
Ultimate Conclusion
In conclusion, Linux for virtual machine promises a wealth of possibilities for users and administrators alike. By understanding the intricacies of virtual machine configurations, management, and security, we can unlock the full potential of these digital entities. As we continue to evolve and improve the art of virtualization, we will undoubtedly see even more remarkable applications of Linux for virtual machine.
General Inquiries
What is the best virtualization software for Linux?
The best virtualization software for Linux depends on individual needs and preferences. Popular options include VirtualBox, VMware, and KVM. Each software has its strengths and weaknesses, and users should research and choose the one that suits their requirements.
How do I configure network settings in a Linux virtual machine?
To configure network settings in a Linux virtual machine, you can follow these steps: First, create a new virtual network interface in the guest operating system. Then, configure the IP address and subnet mask according to your network settings. Finally, verify the network connection by pinging a nearby host or a public IP address.
Can I run multiple operating systems on a single virtual machine?
Yes, you can run multiple operating systems on a single virtual machine, but this may require some tweaking of the virtual machine settings. You should choose an operating system that supports multi-booting and create separate virtual disk images for each operating system. Additionally, you may need to adjust the CPU and memory settings to ensure that each operating system has sufficient resources.
How do I secure my Linux virtual machine?
To secure your Linux virtual machine, you should implement the following best practices: Use strong passwords for all users, including the root user. Enable authentication and authorization using tools like PAM and SELinux. Regularly update your virtual machine’s packages and plugins. Finally, monitor system logs and alerts for potential security threats.