With turn on machine remotely at the forefront, this is a window to an amazing start and intrigue, inviting readers to embark on a tale of modern convenience and technological advancements.
The concept of remote machine access has become increasingly important in today’s world, where machines and devices are being controlled and monitored from afar in various industries, including finance, healthcare, and manufacturing.
Defining Remote Machine Access

In today’s fast-paced and interconnected world, remote machine access has become an essential tool for various industries and individuals. This concept enables users to control and monitor devices or machines from a distance, revolutionizing the way we work and interact with technology. The significance of remote machine access cannot be overstated, as it improves efficiency, increases productivity, and enhances the overall user experience.
Remote machine access allows users to control machines or devices located in remote areas, eliminating the need for physical presence and reducing the risk of accidents or injuries. This technology has far-reaching implications in various industries, including finance, healthcare, and manufacturing. In finance, for instance, remote machine access enables banks to monitor and control ATM machines, ensuring that they are functioning properly and providing accurate transactions.
Controlling Machines Remotely in Various Industries
Remote machine access has become a cornerstone in various industries, with numerous applications and benefits.
Finance Industry
In the finance industry, remote machine access plays a crucial role in maintaining the security and efficiency of financial transactions. For example, banks use remote machine access to monitor and control ATM machines, which are critical to their operations.
| Industry | Example of Machine |
| Finance | ATM Machines |
| Healthcare | Medical Equipment |
Healthcare Industry
In the healthcare industry, remote machine access enables medical professionals to monitor and control medical equipment, such as ventilators or dialysis machines, from a distance. This enhances patient care and reduces the risk of equipment failure.
Manufacturing Industry
In the manufacturing industry, remote machine access improves the efficiency and productivity of production lines. For instance, remote machine access enables manufacturers to monitor and control industrial robots, which perform tasks such as assembly and packaging. This reduces the risk of human error and improves product quality.
Examples of Remote Machine Access in Action
Some examples of remote machine access in action include:
* Monitoring and controlling medical equipment from a distance to ensure patient safety and comfort.
* Controlling industrial robots to improve the efficiency and productivity of production lines.
* Monitoring and controlling ATM machines to ensure accurate transactions and maintain financial security.
Future Developments and Implications
As remote machine access continues to evolve, we can expect to see new and innovative applications of this technology. Some potential developments include:
* Increased use of artificial intelligence and machine learning to improve the efficiency and accuracy of remote machine access.
* Expansion of remote machine access to new industries, such as transportation and logistics.
* Development of new security protocols to protect against cyber threats and ensure the integrity of remote machine access.
Methods for Remote Machine Access
Remote machine access is a crucial aspect of modern computing, allowing users to access and control machines from anywhere in the world. With the rising need for remote work and distributed teams, understanding the different methods of remote access is essential for securing and maintaining connections. This section will compare the various methods of remote access, including VPNs, SSH, and remote desktop software, and discuss their advantages and disadvantages.
VPN (Virtual Private Network) Connectivity
A VPN is a secure connection between two endpoints over a public network, using encryption to protect data and maintain confidentiality. VPNs work by creating a secure “tunnel” between the user’s machine and the remote server, effectively masking the user’s IP address and location. This provides several advantages, including:
- Encryption: VPNs use strong encryption to protect data in transit, making it difficult for unauthorized access or interception.
- Anonymity: By masking the user’s IP address and location, VPNs can provide anonymity and protect user identity.
- Security: VPNs can provide additional security features, such as kill switches and DNS leak protection.
However, VPNs also have some disadvantages, including:
* Speed: VPNs can slow down internet speeds due to encryption and routing overhead.
* Compatibility: Some devices or operating systems may not be compatible with certain VPN protocols.
* Complexity: Setting up and managing VPNs can be complex, especially for large networks.
SSH (Secure Shell) Connectivity
SSH is a secure remote access protocol that allows users to access and control machines remotely, using password or public key authentication. SSH works by establishing a secure connection between the user’s machine and the remote server, using encryption to protect data and maintain confidentiality. This provides several advantages, including:
* Security: SSH provides strong encryption and secure authentication, making it more secure than other remote access protocols.
* Flexibility: SSH can be used for a wide range of tasks, including file transfer, shell access, and secure tunneling.
* Customization: SSH can be customized to suit specific requirements, including authentication methods and encryption algorithms.
However, SSH also has some disadvantages, including:
* Complexity: SSH can be complex to set up and manage, especially for large networks.
* Limited support: SSH may not be supported on all devices or operating systems.
Remote Desktop Software
Remote desktop software allows users to access and control remote machines, using graphical interfaces and remote desktop protocols. Some popular remote desktop software includes:
- TeamViewer: A popular remote desktop software that provides secure, easy-to-use access to remote machines.
- Remote Desktop Protocol (RDP): A protocol developed by Microsoft that allows users to access and control remote Windows machines.
Remote desktop software provides several advantages, including:
* Ease of use: Remote desktop software is often easy to use and intuitive, making it accessible to non-technical users.
* Flexibility: Remote desktop software can be used on a wide range of devices and operating systems.
* Customization: Remote desktop software can be customized to suit specific requirements, including encryption algorithms and authentication methods.
However, remote desktop software also has some disadvantages, including:
* Security risks: Remote desktop software can pose security risks, especially if not properly configured or secured.
* Performance issues: Remote desktop software can cause performance issues, especially if high-bandwidth applications are used.
Best Practices for Implementing Remote Access Solutions
To maintain secure and efficient remote access solutions, follow these best practices:
- Use strong encryption and secure authentication methods.
- Use secure password policies and two-factor authentication.
- Implement regular security updates and patching.
- Use secure protocols and encryption algorithms.
- Monitor and audit remote access connections.
By following these best practices, organizations can maintain secure and efficient remote access solutions, ensuring confidentiality, integrity, and availability of data.
Hardware and Software Requirements
Hardware and software requirements are crucial for establishing reliable and secure remote machine access. A robust infrastructure is necessary to ensure the smooth transfer of data and control signals between the local and remote machines.
To facilitate remote access, the following hardware components are essential:
- Network routers: These devices manage the flow of data between different networks and play a critical role in establishing a connection between the local and remote machines.
- Switches: These network devices help to forward data packets between devices on a network, ensuring efficient communication.
- Firewalls: Firewalls act as a barrier between the local and remote networks, protecting against unauthorized access and potential security threats.
In addition to hardware requirements, the following software tools are commonly used for remote machine access:
- TeamViewer: A remote desktop software that allows users to access and control Windows, macOS, and Linux machines remotely.
- AnyDesk: A secure remote desktop software that enables users to transfer files, print documents, and access remote machines with enhanced security features.
| Software Tool | Description |
| TeamViewer | Remote desktop software for Windows, macOS, and Linux |
| AnyDesk | Secure remote desktop software with file transfer and printing capabilities |
Implementation and Configuration
To set up remote access on a machine, it is essential to follow a series of steps that ensure a secure and functional connection. This involves configuring network settings, enabling remote access software, and implementing necessary security measures.
Configuring Network Settings
Configuring network settings is a crucial step in setting up remote access. This includes ensuring that the machine is properly connected to the internet and that the necessary ports are open for remote access. To configure network settings, follow these steps:
- Enable Wi-Fi or Ethernet connection on the machine.
- Verify that the machine’s IP address is assigned correctly (DHCP or static).
- Configure the machine’s firewall settings to allow incoming connections.
- Verify that the necessary ports (e.g., 22 for SSH, 3389 for RDP) are open for remote access.
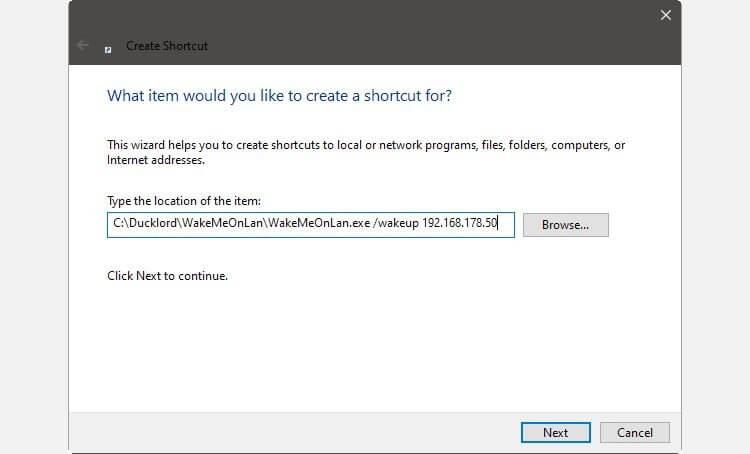
Enabling Remote Access Software
Enabling remote access software is another critical step in setting up remote access. This involves installing and configuring software such as Remote Desktop Protocol (RDP), Secure Shell (SSH), or Virtual Private Network (VPN). To enable remote access software, follow these steps:
- Install RDP, SSH, or VPN software on the machine.
- Configure the software settings to allow remote connections.
- Verify that the software is properly configured and functional.
Implementing Security Measures
Implementing security measures is essential to prevent unauthorized access to the machine. This includes using strong passwords, enabling two-factor authentication (2FA), and configuring access controls. To implement security measures, follow these steps:
- Set strong passwords for all users.
- Enable 2FA to add an extra layer of security.
- Configure access controls to restrict access to authorized users.
- Regularly update and patch the machine’s operating system and software.
Troubleshooting Common Issues
Troubleshooting common issues is an essential part of setting up remote access. This includes troubleshooting connection errors, authentication failures, and other issues that may arise. To troubleshoot common issues, follow these steps:
- Verify that the machine is properly connected to the internet.
- Verify that the necessary ports are open for remote access.
- Chech for any configuration issues with the remote access software.
- Check for any updates or patches for the machine’s operating system and software.
Password Management
Password management is an essential aspect of remote access security. This includes using strong passwords, enabling password rotation, and avoiding password reuse. To manage passwords effectively, follow these best practices:
- Use strong, unique passwords for all users.
- Enable password rotation to ensure that passwords are changed regularly.
- Avoid password reuse to prevent unauthorized access.
- Store passwords securely using a password manager.
Access Control
Access control is a critical aspect of remote access security. This includes configuring access controls to restrict access to authorized users. To implement access controls, follow these steps:
- Configure the remote access software to restrict access to authorized users.
- Use role-based access control (RBAC) to assign users to specific roles.
- Configure access controls to restrict access based on user location.
- Implement audit logging to monitor access and identify potential security threats.
Security Measures

Security is a top priority when it comes to remote machine access, as it directly affects the confidentiality, integrity, and availability of sensitive data. Implementing robust security measures is essential to prevent unauthorized access, data breaches, and other malicious activities. A comprehensive security strategy should encompass encryption, authentication, and intrusion detection and prevention systems to mitigate potential risks and threats.
Security Risks Associated with Remote Access
Remote machine access increases the attack surface, making it more vulnerable to security breaches. Data breaches can occur through various means, including unauthorized access, data theft, and interception. Moreover, remote access provides an entry point for malware, viruses, and other types of malicious software. It is crucial to understand the potential risks associated with remote access to develop an effective security strategy.
-
• Data breaches can lead to financial losses, damage to reputation, and loss of customer trust.
• Unauthorized access can be used to manipulate or destroy data, disrupting business operations.
• Data theft can result in intellectual property loss, compromising business secrets.
Encryption and Secure Authentication Protocols
Encryption and secure authentication protocols are essential to ensure the confidentiality and integrity of data transmitted over remote connections. Encryption converts data into unreadable formats, protecting it from unauthorized access. Secure authentication protocols, such as SSL/TLS and two-factor authentication, verify the identity of users and ensure that data is transmitted securely.
Implementing Encryption for Data-in-Transit
Encryption is a fundamental security measure that converts data into unreadable formats, protecting it from unauthorized access. Implementing encryption for data-in-transit is essential to ensure confidentiality and integrity. SSL/TLS encryption protocols are widely used to secure remote connections and protect data transmitted between systems.
Intrusion Detection and Prevention Systems
Intrusion detection and prevention systems (IDPS) are essential to detect and prevent malicious activities, such as hacking, malware, and denial-of-service (DoS) attacks. IDPS systems can be used to monitor and analyze network traffic for suspicious activity, quickly identifying potential security threats.
Types of IDPS
There are various types of IDPS systems used to secure remote access connections, including:
-
• Network-based IDPS systems, which monitor network traffic for suspicious activity.
• Host-based IDPS systems, which monitor and analyze data on individual systems.
• Application-based IDPS systems, which monitor and analyze specific applications.
Security measures should be implemented at multiple levels to provide comprehensive protection against various types of threats.
Best Practices for Remote Machine Access Security
To ensure the security and integrity of remote machine access connections, organizations should implement the following best practices:
-
• Use strong passwords and multi-factor authentication.
• Implement encryption for data-in-transit.
• Monitor and analyze network traffic for suspicious activity.
• Implement intrusion detection and prevention systems.
• Regularly update and patch remote access software and systems.
Importance of Regular Security Audits
Regular security audits are essential to identify potential security vulnerabilities and weaknesses in remote machine access connections. These audits can help organizations develop an effective security strategy, ensuring the confidentiality, integrity, and availability of sensitive data.
Examples of Remote Machine Access: Turn On Machine Remotely
Remote machine access is a vital technology for modern businesses, allowing employees to work from anywhere, on any device, and at any time. In this section, we will explore various scenarios where remote machine access is used, including remote work setups, disaster recovery scenarios, and IoT devices.
Remote Work Setup
Remote work has become increasingly popular in recent years, with many businesses adopting flexible work arrangements to improve employee productivity and job satisfaction. Remote machine access enables employees to access company resources, collaborate with colleagues, and complete tasks from the comfort of their own homes. This setup offers numerous benefits, including reduced commuting times, increased flexibility, and improved work-life balance.
- Cost savings: Reduced overhead costs, including office space and utilities.
- Increased productivity: Employees can work in a distraction-free environment, leading to enhanced productivity.
- Improved employee satisfaction: Flexible work arrangements can lead to increased job satisfaction and reduced turnover rates.
Disaster Recovery Scenario, Turn on machine remotely
Disaster recovery requires swift and reliable access to critical systems and data. Remote machine access enables businesses to quickly restore services, ensuring minimal downtime and data loss. By having remote access to critical systems, businesses can:
- Quickly restore services: Remote access enables IT teams to quickly access critical systems and restore services.
- Minimize data loss: Remote access allows businesses to quickly recover data, minimizing potential losses.
- Ensure business continuity: Remote machine access enables businesses to continue operating even in the face of disasters.
IoT Devices
The Internet of Things (IoT) has revolutionized the way we interact with devices, making it possible to remotely access and control a wide range of devices, from smart home appliances to industrial control systems. Remote machine access enables businesses to monitor and control IoT devices remotely, improving efficiency and reducing costs.
- Improved efficiency: Remote access enables businesses to monitor and control IoT devices, improving efficiency and reducing manual intervention.
- Reduced costs: Remote access can help reduce manual intervention, leading to cost savings and improved productivity.
- Enhanced security: Remote access enables businesses to monitor and control IoT devices, improving overall security and reducing the risk of cyber threats.
Case Studies
Several industries have successfully implemented remote machine access, improving productivity, reducing costs, and enhancing security.
- IT and Technology: Companies like Amazon and Google have implemented remote work arrangements, leveraging remote machine access to improve productivity and job satisfaction.
- Collections and Finance: Companies like FIS and JPMorgan Chase have implemented remote machine access to improve access to critical systems and data, reducing costs and improving productivity.
- Healthcare: Companies like Medtronic and Philips have implemented remote machine access to improve patient care, reduce costs, and enhance security.
Final Review
The implementation of remote machine access presents a complex scenario, where security considerations and hardware/software requirements play a pivotal role in ensuring uninterrupted access and foolproof data protection.
Commonly Asked Questions
What are the primary advantages of turn on machine remotely?
It allows users to access and control machines remotely, thereby increasing convenience and efficiency.
Can I control any device using turn on machine remotely?
No, certain devices or machines require specific software or hardware configurations for remote access, whereas others may have restrictions or limitations due to security concerns.
How does turn on machine remotely ensure security?
Implementing encryption for data-in-transit, using strong passwords and multi-factor authentication, and monitoring and analyzing network traffic for suspicious activity are essential measures for secure remote machine access.