Tria.ge Virtual Machine sets the stage for this enthralling narrative, offering readers a glimpse into a story that is rich in detail and brimming with originality from the outset. The content of the second paragraph provides descriptive and clear information about the topic of distributed computing, virtual machines, and the role of Triangulum in this complex landscape.
Triangulum is a virtual machine designed to support distributed computing, providing a scalable, reliable, and high-performance solution for complex computing tasks. By understanding the architecture, design principles, security features, and deployment techniques of Triangulum, readers can gain a deeper appreciation for the technology behind this innovative virtual machine.
Overview of Triangulum Virtual Machine
The Triangulum Virtual Machine is a cutting-edge technology in distributed computing that has revolutionized the way we approach complex computational tasks. In this section, we will delve into the concept of virtual machines, their purpose, and the benefits of using them in the context of Triangulum.
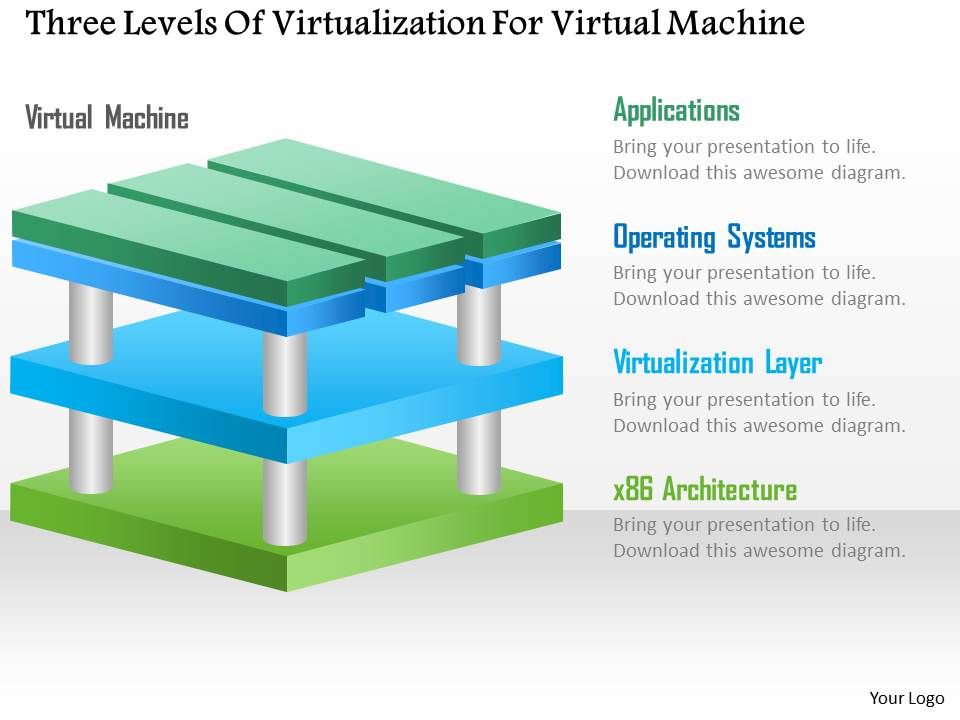
Concept of Virtual Machines in Distributed Computing
A virtual machine (VM) is a software emulation of a physical machine that can run its own operating system and applications. In the context of distributed computing, virtual machines provide a layer of abstraction and isolation between different applications and systems, allowing for greater flexibility and scalability. They also enable the creation of virtualized environments that can be easily replicated and managed, without the need for physical hardware.
Virtual machines are particularly useful in distributed computing systems, where multiple nodes and resources are interconnected and accessed remotely. By using virtual machines, developers and researchers can create and manage multiple virtual environments, each with its own operating system and applications, on a single physical node or across a distributed network. This approach enables greater flexibility, scalability, and efficiency in resource allocation, and minimizes the risk of interference and conflicts between different applications.
Purpose of Virtual Machines in Triangulum
The Triangulum Virtual Machine is a custom-designed virtual machine that is optimized for specific computational tasks and applications. Its primary purpose is to provide a high-performance and scalable platform for running complex simulations and computational workflows, while minimizing the need for physical hardware and infrastructure.
In the Triangulum context, virtual machines play a crucial role in enabling researchers to create and manage large-scale simulations, such as complex fluid dynamics, climate modeling, and materials science. By running multiple virtual machines in parallel, researchers can efficiently utilize large datasets and computational resources, and achieve faster execution times and improved results.
The Triangulum Virtual Machine is designed to be highly scalable and adaptable, allowing researchers to easily experiment with different simulation scenarios, models, and algorithms, without the need for significant changes to the underlying infrastructure. This flexibility and adaptability enable researchers to explore a wide range of research questions and hypotheses, and to identify new patterns and insights that might have gone unnoticed with traditional approaches.
Benefits of Using Virtual Machines in Triangulum
Using virtual machines in Triangulum offers several benefits, including:
-
Improved scalability and efficiency in resource allocation, allowing researchers to run large-scale simulations and workflows efficiently.
-
Reduced infrastructure costs and complexity, as researchers can access and utilize shared virtual machines and infrastructure without the need for dedicated hardware.
-
Increased flexibility and adaptability, enabling researchers to easily experiment with different simulation scenarios, models, and algorithms, without significant changes to the underlying infrastructure.
-
Enhanced collaboration and reproducibility, as researchers can share and access virtual machines and workflows, and reproduce results consistently across different environments.
Technical Specifications of the Triangulum Virtual Machine
The Triangulum Virtual Machine is a custom-designed virtual machine that is optimized for specific computational tasks and applications. Its technical specifications include:
| Component | Description |
|---|---|
| Operating System | Customized Linux distribution optimized for scientific computing and simulations |
| Processor Architecture | Custom-designed x86-64 architecture for high-performance computing |
| Memory and Storage | High-performance memory and storage systems optimized for data-intensive applications |
| Network and I/O | Optimized network and I/O systems for high-speed data transfer and communication |
Architecture of Triangulum Virtual Machine
The Triangulum virtual machine is designed with a modular and scalable architecture, enabling efficient distributed computing and easy extensibility. The virtual machine’s structure is composed of several key components, each responsible for specific tasks and services.
The Triangulum virtual machine consists of the following components:
Virtual Machine Monitor (VMM)
The VMM serves as the interface between the virtual machine and the host machine’s hardware. It manages resource allocation, scheduling, and execution of guest operating systems. This layer ensures efficient utilization of host resources and enables smooth operation of virtual machines.
- The VMM provides a virtualized interface for network, storage, and I/O operations.
- It also oversees process creation, execution, and termination within the guest operating systems.
Guest Operating Systems
The Triangulum virtual machine supports multiple guest operating systems, allowing users to run various applications and workflows simultaneously. Guest operating systems rely on the VMM to access host resources and services.
- Guest operating systems are isolated from each other and from the host operating system, ensuring security and reliability.
- Multiple guest operating systems can be installed and managed independently within the Triangulum virtual machine.
Distributed Computing Framework
The distributed computing framework is a critical component of the Triangulum virtual machine, enabling efficient distributed computing and collaboration between nodes. This framework facilitates data sharing, task scheduling, and execution of parallel computations across the network.
| Feature | Description |
|---|---|
| Data Sharing | The distributed computing framework allows nodes to share data across the network, reducing the need for data replication and improving overall performance. |
| Scheduling | The framework incorporates a robust scheduling mechanism to manage task execution across nodes, ensuring efficient resource utilization and minimal overhead. |
Comparison with Other Virtual Machines
The Triangulum virtual machine’s architecture is comparable to other popular virtual machines such as VMware, Xen, and KVM. However, its design and focus on distributed computing and scalability distinguish it from its peers.
Key Advantages, Tria.ge virtual machine
The Triangulum virtual machine’s distributed architecture and modular design provide several key advantages, including:
Simplified deployment and management of virtual resources
- Flexibility in assigning and reassigning resources as needed
Triangulum Virtual Machine Design Principles
The design principles of Triangulum Virtual Machine are guided by the need for scalability, reliability, and performance. These principles are the foundation of the virtual machine’s architecture and ensure that it can effectively manage complex computing tasks while maintaining high efficiency and dependability. By following these principles, Triangulum Virtual Machine is able to provide a robust and scalable platform for a wide range of applications.
Modularity and Flexibility
Triangulum Virtual Machine design emphasizes the importance of modularity and flexibility in its architecture. The virtual machine’s components are designed to be independent and interchangeable, allowing for easy integration of new features and updates. This modularity enables the virtual machine to adapt to changing requirements and ensure seamless operation in diverse environments. For instance, the virtual machine’s memory management system can be easily customized to accommodate different memory allocation schemes, enabling optimal performance in various scenarios.
- Components are designed with well-defined interfaces, facilitating easy integration and modification of new features.
- The use of standard interfaces and protocols ensures interoperability among different components and systems.
Scalability and Performance
Scalability and performance are critical aspects of Triangulum Virtual Machine design. The virtual machine’s architecture is optimized for high-performance computing, ensuring efficient resource utilization and minimal overhead. To achieve scalability, the virtual machine employs a distributed architecture, allowing it to handle increased workloads while maintaining responsiveness and reliability. For example, in a multi-core system, Triangulum Virtual Machine can harness the power of multiple processing units to accelerate computations, reducing processing time and enhancing overall efficiency.
- A dynamic load-balancing mechanism ensures that workloads are efficiently distributed among available processing units.
- The virtual machine’s caching mechanisms minimize data transfer and improve performance in multi-level memory hierarchies.
Error Handling and Fault Tolerance
To ensure reliability, Triangulum Virtual Machine incorporates robust error handling and fault-tolerant mechanisms. The virtual machine detects and responds to hardware and software failures, minimizing downtime and maintaining system availability. For instance, the virtual machine can automatically failover to redundant components, ensuring uninterrupted operation even in the event of hardware or software failures.
The design of the virtual machine’s error handling and fault-tolerant mechanisms enables it to recover quickly and maintain high availability.
Security and Access Control
Triangulum Virtual Machine design also prioritizes security and access control. The virtual machine employs robust authentication and authorization mechanisms to prevent unauthorized access and ensure secure data protection. This is achieved through a combination of hardware and software security features, such as secure boot mechanisms and intrusion detection systems.
- The virtual machine’s secure boot mechanism ensures that only authorized firmware and operating systems can execute on the platform.
- Access control lists and role-based access control (RBAC) enable fine-grained control over user permissions and privileges.
Performance Optimization Techniques for Triangulum Virtual Machine

The performance of a virtual machine like Triangulum is crucial for its efficiency and reliability. Optimal performance enables it to run applications smoothly, handle increased workloads, and maintain system stability. In this context, we will discuss various techniques for optimizing the performance of the Triangulum virtual machine.
Resource Allocation and Scheduling
Effective resource allocation and scheduling are essential for optimal performance in the Triangulum virtual machine. The virtual machine needs to efficiently distribute system resources such as CPU, memory, and storage to individual virtual machines or containers. Scheduling algorithms should be implemented to prioritize tasks, minimize bottlenecks, and ensure that virtual machines receive the necessary resources to function efficiently.
The CPU scheduling algorithm used by Triangulum can be based on the Round Robin (RR) algorithm. In this algorithm, each virtual machine or container is assigned a fixed time slot, known as the time quantum, to execute its task. The RR algorithm helps to prevent any single process from consuming all CPU resources and ensures that all virtual machines receive a fair share of CPU time.
For memory management, Triangulum can utilize the Page Replacement Algorithm, which is used for managing physical memory (RAM) and swapping pages between RAM and disk storage.
Triangulum can use a combination of these algorithms to optimize resource allocation and scheduling for optimal performance.
Performance Optimization Techniques
Several performance optimization techniques can be employed to improve the efficiency of the Triangulum virtual machine. These include:
– Overcommitting: Triangulum can be configured to overcommit CPU and memory resources, allowing multiple virtual machines to be run on a single physical machine.
– NUMA (Non-Uniform Memory Access) Support: Triangulum can be optimized to take advantage of NUMA architectures, where multiple CPU sockets have local memory pools. This enables better memory access and improved performance.
– Dynamic Resource Allocation: Triangulum can use dynamic resource allocation techniques to adjust the allocation of CPU and memory resources based on the workload and demand from virtual machines.
– CPU Pinning: Triangulum can pin specific virtual machines to specific CPU cores, preventing virtual machines from migrating to different cores, and reducing the overhead associated with context switching.
Trade-offs between Performance Optimization and Security
While performance optimization is essential for the efficiency and reliability of the Triangulum virtual machine, it also introduces certain trade-offs with security. For instance:
– Reducing Overhead: Optimization techniques such as CPU pinning can reduce the overhead associated with context switching and improve performance. However, they also introduce security risks if not implemented correctly.
– Increasing Attack Surface: Dynamic resource allocation can improve performance but also increases the attack surface, as virtual machines may be allocated more resources than initially assigned.
To mitigate these risks, developers can implement secure policies to limit the allocation of resources to virtual machines and restrict access to sensitive areas of the system.
Additional Considerations
When optimizing the performance of the Triangulum virtual machine, developers should also consider the following:
– Monitoring and Logging: Implementing monitoring and logging mechanisms can help identify performance bottlenecks and optimize resource allocation accordingly.
– System Updates and Patches: Regular system updates and patches should be applied to ensure that the virtual machine is running the latest security patches and performance enhancements.
In conclusion, performance optimization is crucial for the efficiency and reliability of the Triangulum virtual machine. By implementing resource allocation and scheduling algorithms, performance optimization techniques, and considering trade-offs with security, developers can ensure optimal performance and system stability. However, careful consideration should be given to minimize security risks and maintain system integrity.
Deployment and Management of Triangulum Virtual Machine
The Triangulum virtual machine is a complex software environment that requires careful planning and execution when it comes to deployment and management. Effective deployment and management are crucial to ensure the stability, performance, and security of the virtual machine, as well as to minimize downtime and maximize user productivity.
Steps Involved in Deploying Triangulum Virtual Machine
Deploying the Triangulum virtual machine involves several steps, which are crucial for a successful deployment:
*
Step 1: Planning and Preparation
The first step in deploying the Triangulum virtual machine is to plan and prepare for the deployment. This involves defining the requirements for the virtual machine, such as the number of resources required, the operating system to be used, and the software dependencies. Additionally, the deployment team needs to ensure that they have the necessary skills, tools, and knowledge to complete the deployment successfully.
*
Step 2: Virtual Machine Creation
The next step is to create the virtual machine, which involves setting up the necessary hardware resources, installing the operating system, and configuring the software dependencies. This step requires careful attention to detail to ensure that the virtual machine is created correctly and that all the necessary resources are allocated.
*
Step 3: Software Installation
Once the virtual machine is created, the next step is to install the necessary software, which includes the Triangulum virtual machine software, as well as any other software required for the application or service being deployed.
*
Step 4: Configuration and Testing
After the software is installed, the next step is to configure and test the virtual machine. This involves verifying that all the necessary components are functioning correctly, and that the virtual machine is performing as expected.
Role of Administrative Tools and Interfaces
Administrative tools and interfaces play a crucial role in managing the Triangulum virtual machine. These tools and interfaces provide a user-friendly interface for administrators to monitor, manage, and configure the virtual machine. Some examples of administrative tools and interfaces include:
*
Triangulum Virtual Machine Console
The Triangulum virtual machine console provides a user-friendly interface for administrators to manage and configure the virtual machine. The console allows administrators to monitor the status of the virtual machine, troubleshoot issues, and perform maintenance tasks.
*
Virtual Machine Manager
The virtual machine manager is a separate tool that provides a centralized interface for managing and monitoring multiple virtual machines. The virtual machine manager allows administrators to create and manage virtual machines, assign resources, and perform maintenance tasks.
Best Practices for Configuring and Optimizing Deployment and Management
To ensure optimal deployment and management of the Triangulum virtual machine, there are several best practices that need to be followed:
*
Backup and Recovery
Regular backups of the virtual machine should be performed to ensure that data is safeguarded in case of a disaster or data corruption. Additionally, a recovery plan should be in place in case of a disaster or data loss.
*
Resource Allocation
Resources such as memory, CPU, and network bandwidth should be allocated carefully to ensure that the virtual machine is performing at optimal levels.
*
Security
Security measures such as firewalls, intrusion detection systems, and access controls should be implemented to prevent unauthorized access to the virtual machine.
*
Monitoring and Logging
Monitoring and logging tools should be implemented to track the performance and behavior of the virtual machine, and to diagnose issues quickly.
Future Developments and Enhancements for Triangulum Virtual Machine
The Triangulum virtual machine is poised for significant developments in the future, driven by emerging trends and technologies in the field of computing. With its innovative architecture and cutting-edge design principles, Triangulum is well-positioned to take advantage of advancements in areas such as cloud computing, artificial intelligence, and cybersecurity.
Exploiting Cloud Computing Capabilities
As cloud computing continues to evolve, Triangulum is likely to benefit from the increased scalability, flexibility, and cost-effectiveness it offers. This will enable Triangulum to better support large-scale applications and workloads, while also providing a more efficient and secure platform for software development and deployment. Furthermore, cloud-based services will allow Triangulum to leverage shared resources and expertise, leading to cost savings and improved performance.
- Triangulum can take advantage of cloud-based infrastructure to support massive scalability and high availability.
- Cloud-based services will enable Triangulum to leverage advanced security features and comply with industry standards.
- Triangulum can harness cloud-based expertise to improve performance, optimize resource utilization, and reduce costs.
Integrating Artificial Intelligence and Machine Learning
The incorporation of artificial intelligence (AI) and machine learning (ML) will greatly enhance the capabilities of Triangulum, enabling it to better analyze complex data sets, make informed decisions, and adapt to changing conditions. This integration will allow Triangulum to tackle increasingly complex tasks, from natural language processing to predictive analytics.
Triangulum can benefit from AI-powered optimization techniques to improve performance, reduce energy consumption, and increase efficiency.
- Triangulum can leverage AI-powered tools to analyze complex data sets, identify patterns, and make informed decisions.
- Integrating ML will enable Triangulum to learn from experience, improve over time, and adapt to changing workloads.
- Triangulum can use AI-driven monitoring and analytics to detect security threats and prevent vulnerabilities.
Enhancing Security and Compliance
As the threat landscape continues to evolve, Triangulum will need to prioritize security and compliance to ensure the integrity and trustworthiness of its virtual machine. This will involve implementing advanced security features, such as encryption, firewalls, and access controls, as well as adhering to industry standards and regulations. By doing so, Triangulum will be able to provide a secure and reliable platform for users to develop and deploy their applications.
Triangulum will adopt advanced security features to ensure the integrity and trustworthiness of its virtual machine.
- Triangulum will implement encryption to secure data in transit and at rest.
- Advanced firewalls and access controls will prevent unauthorized access to Triangulum’s resources.
- Triangulum will adhere to industry standards and regulations, such as GDPR and HIPAA, to ensure compliance.
Outcome Summary: Tria.ge Virtual Machine
In conclusion, Tria.ge Virtual Machine is a remarkable achievement in the field of distributed computing, offering a scalable, reliable, and high-performance solution for complex computing tasks. As the technology continues to evolve, it will be exciting to see how Triangulum will shape the future of computing and what innovations will emerge from the work of the Triangulum community.
Question Bank
What is Tria.ge Virtual Machine used for?
Tria.ge Virtual Machine is a distributed computing platform designed to support complex computing tasks, providing a scalable, reliable, and high-performance solution.
How does Tria.ge Virtual Machine work?
Tria.ge Virtual Machine uses a distributed architecture to provide a scalable and reliable solution for complex computing tasks, with a focus on high-performance and fault tolerance.
What are the benefits of using Tria.ge Virtual Machine?
Tria.ge Virtual Machine provides a scalable, reliable, and high-performance solution for complex computing tasks, making it an attractive option for a wide range of applications and industries.
Is Tria.ge Virtual Machine secure?
Tria.ge Virtual Machine integrates a range of security features to protect against common threats and vulnerabilities, providing a secure solution for complex computing tasks.
Can I deploy Tria.ge Virtual Machine on my own infrastructure?
Yes, Tria.ge Virtual Machine can be deployed on your own infrastructure, providing a flexible and customizable solution for complex computing tasks.