Interactive Logon Machine Inactivity Limit is a crucial aspect of system security, and it’s essential for users to understand its purpose and importance. This article will delve into the world of inactivity limits, exploring its relevance, benefits, and impact on system performance.
The inactivity limit is a feature that automatically logs out a user after a specified period of inactivity. This feature is critical in various industries, including finance, healthcare, and government, where security and data confidentiality are paramount.
Defining Interactive Logon Machine Inactivity Limit
The interactive logon machine inactivity limit is a crucial feature designed to prevent unauthorized access and ensure the security of sensitive systems. This limit specifies the maximum period an interactive logon machine can remain inactive before it automatically locks or logs off the user, thereby preventing potential security threats.
The purpose of the interactive logon machine inactivity limit is to protect sensitive systems and data from unauthorized access. By setting a time limit, administrators can reduce the risk of security breaches, data theft, and other malicious activities that can occur when a machine remains locked and unattended.
The importance of implementing this feature cannot be overstated, especially in industries that heavily rely on security and data integrity. Industries such as finance, healthcare, government, and defense require robust security measures to safeguard their systems and data. Implementing an interactive logon machine inactivity limit is a critical step in ensuring the security and integrity of these systems.
- Examples of Industries that Heavily Rely on Interactive Logon Machine Inactivity Limit:
Many industries rely on interactive logon machine inactivity limits to ensure the security and integrity of their systems and data.
- Financial Institutions
- Healthcare Organizations
- Government Agencies
- Defense Contractors
- Manufacturing and Industrial Plants
Each of these industries requires a high level of security and compliance to prevent data breaches and maintain confidentiality. By implementing an interactive logon machine inactivity limit, administrators can ensure that sensitive systems and data are protected from unauthorized access.
Interactive logon machine inactivity limits can be set for various types of systems, including desktops, laptops, and servers. By setting a specific time limit, administrators can ensure that only authorized users have access to sensitive systems and data. This feature is particularly important in environments where multiple users share a single machine or system.
By implementing an interactive logon machine inactivity limit, administrators can ensure the security and integrity of sensitive systems and data, protecting against unauthorized access, data breaches, and other potential security threats.
Types of Interactive Logon Machine Inactivity Limit
The inactivity limit for an interactive logon machine can be configured in two different ways, automatic and manual, and can be based on either session or idle time.
For
Automatic vs. Manual Inactivity Limit Settings
Automatic inactivity limit settings allow administrators to define a specific time period after which a user’s session will be terminated if they are inactive. This setting is particularly useful in situations where administrators need to ensure that users are actively working on their machines. On the other hand, manual inactivity limit settings provide users with the option to reset their inactivity timer manually, allowing them to pause their session for short periods without losing their work. This feature is ideal for users who need to step away from their machines briefly to perform tasks not related to their work.
Automatic settings are preferred for organizations with strict security protocols, as they eliminate the possibility of an idle machine being used as a point of attack by malicious actors. However, manual settings are recommended for users who need to frequently pause their work due to unforeseen circumstances.
Automatic and manual inactivity limits also differ in their approach to handling user sessions. Automatic settings can be set to terminate user sessions after a specified period of inactivity, while manual settings allow users to extend their sessions or pause them when necessary.
| Inactivity Limit Setting | Description |
| :———————— | :———- |
| Automatic | Sessions are terminated after a set period of inactivity. |
| Manual | Users can manually reset or extend their inactivity timer. |
For
Session-based vs. Idle Time-based Inactivity Limits
Session-based inactivity limits are calculated from the start of a user’s session, whereas idle time-based inactivity limits are measured based on the duration of inactivity observed after a user has logged on to their machine.
Session-based inactivity limits are often preferred in environments where users are working for extended periods, such as in design, coding, or other tasks that require users to remain focused on their work. These settings are useful in preventing users from working in a dormant or idle state, which may indicate a security risk.
On the other hand, idle time-based inactivity limits can be more flexible and allow users to step away from their machines briefly for routine tasks, such as taking calls, walking to meetings, or addressing other issues unrelated to their work.
Implications of Varying Inactivity Limit Settings, Interactive logon machine inactivity limit
Configuring the right type of inactivity limit is crucial for achieving the balance between security, productivity, and user experience.
If an organization prioritizes security over user convenience, it may be more beneficial to configure automatic session-based inactivity limits. However, if user comfort is a more significant concern, implementing manual session-based or idle time-based inactivity limits may provide users with greater autonomy over their work sessions.
The impact of inactivity limit settings on system performance should also be considered. While automatic session-based inactivity limits may result in a decrease in security breaches, they can lead to an increase in logon attempts as users attempt to regain access to their systems. This may cause system load issues and degrade overall performance.
Therefore, administrators need to carefully evaluate their organization’s specific needs and requirements when configuring inactivity limits. This may involve weighing the benefits and drawbacks of different settings and implementing a strategy that strikes a balance between security and user productivity.
Implementing and Managing Interactive Logon Machine Inactivity Limit
In the realm of security and system administration, setting and managing inactivity limits for interactive logon machines is a crucial task. It serves as a safeguard against unauthorized access and potential breaches. By implementing these limits, organizations can ensure that users are periodically required to enter their credentials, thereby preventing extended periods of unattended access.
Technical Requirements for Implementing Inactivity Limits
To effectively implement inactivity limits, several technical requirements must be in place. These include:
- An operating system capable of supporting group policy or other management tools.
- A domain or Active Directory setup for centralized management.
- Server software, such as Windows Server or a compatible alternative.
- Client-side software or firmware that can enforce inactivity limits, such as Windows Client.
- Network infrastructure to support secure authentication and communication.
These technical requirements enable administrators to implement and manage inactivity limits effectively. The following sections will delve into the methods for monitoring and enforcing inactivity limits.
Methods for Monitoring and Enforcing Inactivity Limits
There are several methods for monitoring and enforcing inactivity limits on interactive logon machines. These include:
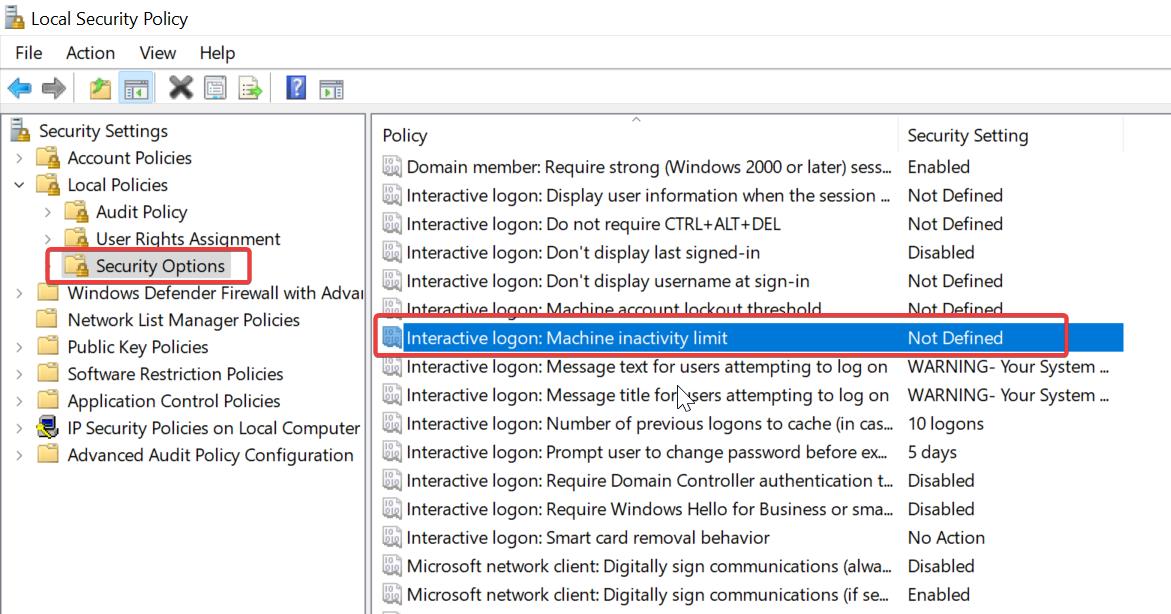
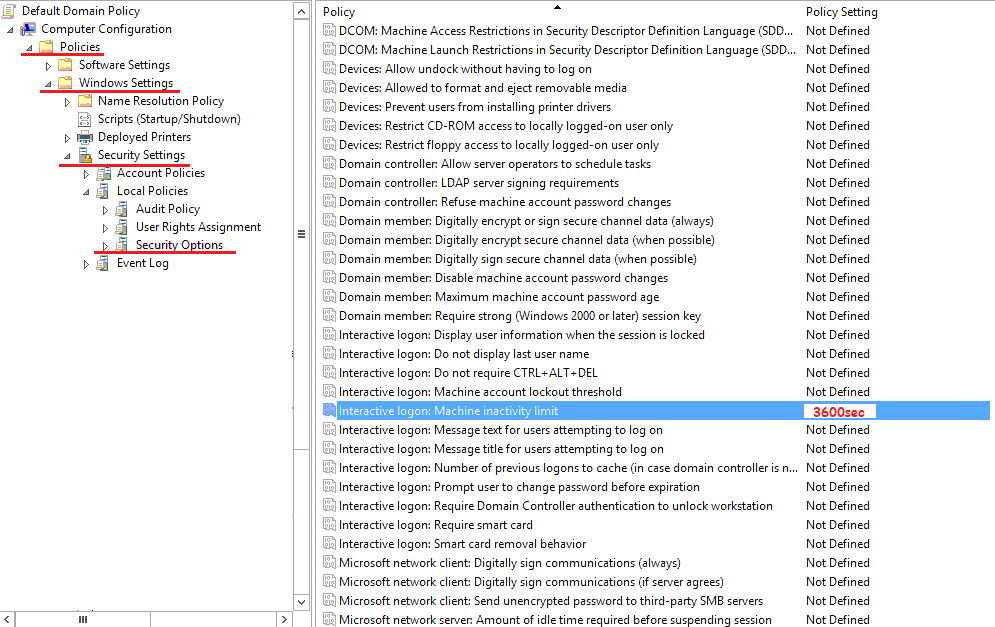
- Group Policy Objects (GPOs): Windows Active Directory allows administrators to create and apply Group Policy Objects to configure settings, including inactivity limits, across the network.
- PowerShell Scripts: Advanced Power Management (APM) and Windows PowerShell can be used to create scripts that enforce inactivity limits and automate tasks.
- Login Scripts: Local login scripts can be used to enforce inactivity limits on individual workstations.
- Vulnerability Scanners: Automated scanners can monitor network traffic and detect unauthorized access or inactivity.
These methods provide administrators with a range of options for monitoring and enforcing inactivity limits, ensuring that users comply with security policies and minimizing the risk of unauthorized access.
Consequences of Ignoring Inactivity Limit Settings
Ignoring inactivity limits can have severe consequences, including:
- Unmanaged Access: Unattended access can lead to unauthorized modification, deletion, or creation of sensitive data, compromising network security.
- Privilege Escalation: Inactive sessions can be exploited by attackers to gain elevated privileges and access sensitive resources.
- Data Breach: Ignoring inactivity limits can enable hackers to remain undetected, allowing them to steal sensitive information or disrupt critical systems.
- Compliance Non-Adherence: Failing to enforce inactivity limits can put organizations at risk of non-compliance with regulatory requirements, such as GDPR or HIPAA.
The consequences of ignoring inactivity limits are severe and can have long-lasting repercussions, making it essential for administrators to prioritize the implementation and management of these security measures.
The importance of implementing and managing inactivity limits cannot be overstated. By doing so, organizations can significantly reduce the risk of unauthorized access, data breaches, and privilege escalation, while ensuring compliance with regulatory requirements.
Impact of Interactive Logon Machine Inactivity Limit on User Experience
The implementation of interactive logon machine inactivity limits has been a contentious issue in various industries. While it aims to increase security by locking out users who have been inactive for a prolonged period, it can have a significant impact on user experience. Inactivity limits can lead to frustration, reduced productivity, and a negative perception of the organization or service provider.
Effects of Inactivity Limits on User Productivity
Implementing inactivity limits can lead to a decrease in user productivity due to the requirement for users to log back in after a certain period. This can be particularly problematic for individuals who need to switch between tasks or applications frequently. For instance, a user who is working on a project and receives a phone call may be unable to quickly pick up where they left off due to the inactivity limit, resulting in lost time and decreased productivity.
- Increased time spent logging back in
- Lost productivity due to interruptions
- Decreased user satisfaction
In many cases, users have reported feeling frustrated with inactivity limits, as they can lead to a sense of being “locked out” without warning. This can be particularly problematic for remote workers or individuals who work in locations with limited internet access.
Alternative Solutions for Maintaining User Engagement
Organizations can implement alternative solutions to maintain user engagement while still meeting security requirements. Some examples include:
- Session timeout alerts: Informing users when their session is about to expire, allowing them to log back in or save their work
- Auto-save functionality: Automatically saving user data at regular intervals to prevent lost work due to session timeouts
- Background task management: Allowing users to continue working in the background while still meeting security requirements
By implementing these alternatives, organizations can balance user experience with security concerns, leading to increased user satisfaction and productivity.
User Feedback on Inactivity Limits in Various Industries
User feedback on inactivity limits has been mixed across various industries. In some cases, users have reported feeling frustrated with inactivity limits, while others have expressed support for the increased security measures.
| Industry | User Feedback |
|---|---|
| Healthcare | Users have reported feeling frustrated with inactivity limits, particularly in situations where medical emergencies require rapid access to patient information |
| Finance | Users have expressed support for inactivity limits, citing increased security and protection against unauthorized access |
| Education | Users have reported feeling frustrated with inactivity limits, particularly in situations where online coursework requires extended periods of inactivity |
Ultimately, the impact of interactive logon machine inactivity limits on user experience will depend on the specific needs and requirements of each organization. By understanding the effects of inactivity limits and implementing alternative solutions, organizations can balance user experience with security concerns, leading to increased user satisfaction and productivity.
Technical Specifications for Interactive Logon Machine Inactivity Limit

When configuring interactive logon machine inactivity limits, it is essential to consider the technical specifications that govern their implementation and enforcement. These specifications interact with various authentication protocols, affecting system performance and user experience.
Interaction with Authentication Protocols
Interactive logon machine inactivity limits interact with authentication protocols by integrating with the authentication workflow. When a user is idle for a predetermined period, the system triggers an authentication protocol to verify the user’s credentials. This ensures that the user’s session remains secure and protected from unauthorized access. For instance, suppose a company implements a 15-minute inactivity limit for its employees’ logins. When an employee is idle for 15 minutes, the system reverts to the login screen, prompting the employee to re-authenticate before re-accessing their resources.
Enforcement of Inactivity Limits
Inactivity limits are enforced through a combination of software and hardware components. The system periodically checks the user’s activity status, and when the limit is exceeded, it initiates the re-authentication process. Modern operating systems and applications employ complex algorithms to monitor user activity and adjust inactivity limits according to their settings. For example, Windows systems use the Session Manager to track user sessions and enforce inactivity limits. When a user is idle for an extended period, the system terminates the session, prompting the user to log in again.
Impact on System Resources
Imposing inactivity limits can have varying effects on system resources, depending on the configuration and implementation. When an inactivity limit is exceeded, the system may initiate a re-authentication process, which can temporarily increase system resource utilization. This can lead to a slight increase in CPU usage, memory allocation, and network traffic. However, modern systems are designed to manage these fluctuations effectively, ensuring seamless user experience. For instance, a company with 10,000 employees implementing a 15-minute inactivity limit may experience a marginal increase in system resource utilization during peak usage hours, but this would be compensated by improved security and reduced risk of unauthorized access.
Troubleshooting Common Issues with Interactive Logon Machine Inactivity Limit
When implementing an interactive logon machine inactivity limit, it’s not uncommon to encounter issues that can hinder productivity and user experience. This sub-section will guide you through the process of identifying and resolving common errors related to inactivity limits, as well as comparing approaches to error reporting and tracking.
Identifying Common Errors Related to Inactivity Limits
Common errors related to inactivity limits often stem from misconfigured settings, user account restrictions, or conflicts with other system policies. To troubleshoot these issues, it’s essential to:
- Review the inactivity limit settings and ensure they are aligned with organizational policies and user needs. For instance, if the inactivity limit is set too low, users may experience unexpected logouts.
- Verify user account privileges and permissions. Users with limited access may be restricted from configuring account settings or accessing system resources.
- Check for conflicts with other system policies, such as screen saver or password policies. These policies may interact with the inactivity limit and cause issues.
- Monitor system logs and event viewer for errors and warnings related to the inactivity limit. This will help you identify potential issues and their underlying causes.
Resolving Inactivity Limit-Related Issues
To resolve inactivity limit-related issues, follow these step-by-step procedures:
- Temporarily reduce or disable the inactivity limit to test and isolate the issue.
- Restore the original inactivity limit setting and recreate the issue to understand its cause.
- Modify the inactivity limit setting or adjust related system policies to resolve the issue.
- Verify the changes and retest the inactivity limit setting to ensure the issue is resolved.
Error Reporting and Tracking
Effective error reporting and tracking are crucial for identifying and resolving inactivity limit-related issues. Consider the following approaches:
- Implement a centralized logging system to collect and analyze system logs, event viewer entries, and user feedback.
- Establish a clear error reporting process, including guidelines for users to submit reports and provide relevant information.
- Use automated tools to detect and alert administrators to potential issues related to the inactivity limit.
- Regularly review and analyze error reports to identify trends, root causes, and areas for improvement.
Conclusive Thoughts
Summarizing the importance of Interactive Logon Machine Inactivity Limit, it’s clear that this feature plays a vital role in maintaining system security and productivity. Users must understand its relevance, and IT administrators must be involved in setting the inactivity limits to ensure effective implementation.
Essential Questionnaire
Q: What are the benefits of implementing Interactive Logon Machine Inactivity Limit?
A: The benefits include improved system security, increased productivity, and enhanced data confidentiality.
Q: How do inactivity limits impact system performance?
A: Inactivity limits can improve system performance by automatically logging out inactive users, reducing the risk of unauthorized access.
Q: Can inactivity limits be customized?
A: Yes, inactivity limits can be customized to meet the specific needs of an organization or industry.
Q: What are the consequences of ignoring inactivity limit settings?
A: Ignoring inactivity limit settings can lead to security breaches, data loss, and system compromise.