Machine to machine authentication is a critical concept in the digital age, where devices and systems interact and exchange information with each other. Delving into machine to machine authentication, this introduction immerses readers in a unique and compelling narrative, with engaging storytelling that is both thought-provoking and informative.
The concept of machine to machine authentication involves the use of various protocols and methods to securely exchange information between devices and systems. This can range from simple authentication methods like symmetric keys to more complex protocols like OpenID Connect and JWT.
Best Practices for M2M Authentication: Machine To Machine Authentication
In the realm of machine-to-machine authentication, security is paramount. As machines communicate with each other, they share sensitive information that can be exploited by malicious entities. Secure key storage and certificate management are vital components in safeguarding the integrity of M2M interactions.
Secure Key Storage and Certificate Management
Secure key storage and certificate management are crucial for M2M authentication. This involves storing cryptographic keys securely on the device, utilizing robust encryption algorithms, and managing certificates effectively to prevent unauthorized access.
- Use Hardware Security Modules (HSMs) to securely store cryptographic keys.
- Implement Public Key Infrastructure (PKI) to manage certificates and ensure they are properly issued, renewed, and revoked.
- Store sensitive data in a secure, tamper-proof environment to prevent unauthorized access.
- Regularly update and patch cryptographic algorithms to stay ahead of known vulnerabilities.
In addition to these best practices, implementing secure key storage and certificate management can be achieved through the use of secure protocols, such as Secure Sockets Layer (SSL) or Transport Layer Security (TLS), which provide end-to-end encryption for secure communication between machines.
Reducing Latency and Improving Performance in M2M Authentication
Minimizing latency in M2M authentication is essential for seamless communication between machines. This can be achieved through efficient protocol design, optimized network architecture, and reduced computational overhead.
- Implement efficient communication protocols that minimize the number of round trips and reduce latency.
- Optimize network architecture to reduce congestion and packet loss.
- Use caching mechanisms to store frequently accessed data and reduce the need for round trips.
- Implement lightweight authentication mechanisms that do not add significant computational overhead.
Implementing M2M Authentication with Multiple Protocols and Devices
M2M authentication may involve communicating with multiple devices and protocols. Ensuring seamless communication across these platforms is crucial for successful authentication.
- Implement protocol-agnostic authentication mechanisms that can adapt to different communication protocols.
- Use standardized APIs and interfaces to ensure interoperability across different devices and platforms.
- Implement load balancing and failover mechanisms to ensure high availability and reliability.
- Regularly test and validate authentication mechanisms across multiple scenarios and devices.
Securing M2M Authentication Logs and Metrics
M2M authentication logs and metrics contain sensitive information about user interactions and communication patterns. Securing these logs and metrics is essential to prevent unauthorized access and ensure compliance with regulatory requirements.
- Store logs in a secure, encrypted environment to prevent unauthorized access.
- Implement access controls and auditing mechanisms to track user interactions and ensure compliance.
- Regularly update and patch systems to stay ahead of known vulnerabilities.
- Implement real-time analytics and monitoring to detect potential security issues.
M2M Authentication Examples
In the realm of machine-to-machine (M2M) communication, authentication is a pivotal component ensuring the security, reliability, and integrity of data exchanged between devices. Here, we shall delve into real-world scenarios necessitating M2M authentication, and illustrate the implementation of such systems.
Smart Energy Management System
A smart energy management system, for instance, might comprise a central gateway receiving data from various sensors installed in buildings. These sensors monitor electricity usage, temperature, and other parameters, sending their readings wirelessly to the gateway for analysis and potential control. To secure this system, M2M authentication becomes vital. The gateway should verify the identity of each sensor before accepting and processing their data.
Authentication of sensors is based on a secure communication protocol, such as Transport Layer Security (TLS) or Internet Protocol Security (IPSec), ensuring that only authorized devices can join the network and send legitimate data.
- The central gateway should be configured to recognize a set of predefined sensor IDs during manufacturing or setup.
- Each sensor should be equipped with a unique, time-stamped token or certificate, which is verified by the gateway upon connection.
- The gateway uses the validated sensor ID and token to grant or deny access to the network and authenticate incoming data.
Industrial Automation and Predictive Maintenance, Machine to machine authentication
In an industrial setting, M2M authentication can be employed in industrial automation and predictive maintenance applications. For example, a network of sensors and actuators in a manufacturing facility must communicate with each other and with a central control system to ensure efficient production and minimize downtime. M2M authentication can be used to secure the communication between these devices, preventing unauthorized changes in production parameters and ensuring that updates from sensors are accurate and trustworthy.
- A centralized control system acts as the central gateway, receiving and processing data from various sensors and actuators.
- Sensors and actuators are identified using a unique identifier (ID) or serial number, which is verified against a database maintained by the control system.
- The control system uses the validated device ID to authenticate data from sensors and authorize commands sent from actuators.
M2M Authentication in IoT Devices
Machine-to-machine authentication is not exclusive to the enterprise space. Consumer-grade IoT devices, such as smart home thermostats or security cameras, also rely on M2M authentication to operate securely and efficiently. IoT devices communicate with a central hub or cloud service to exchange data, control their settings, and receive software updates.
| Device | Authentication Mechanism |
|---|---|
| Smart Thermostat | Wi-Fi-based authentication using WPA2 encryption and a unique device ID. |
| Security Camera | Internet-based authentication using SSL/TLS certificates issued by a trusted Certificate Authority. |
Last Word

In conclusion, machine to machine authentication is a complex and multifaceted topic that requires careful consideration and planning. By understanding the different types of authentication, protocols, and methods, organizations can ensure the security and integrity of their devices and systems. Our hope is that this content has provided a comprehensive overview of machine to machine authentication and has inspired readers to explore this topic further.
Questions Often Asked
What is machine to machine authentication?
Machine to machine authentication is a process that involves verifying the identity of devices and systems to ensure secure communication and exchange of information.
What are the different types of machine to machine authentication protocols?
There are several types of machine to machine authentication protocols, including OAuth, SAML, OpenID Connect, and JWT. Each protocol has its own strengths and weaknesses, and the choice of protocol depends on the specific use case and requirements.
What is symmetric key encryption and how does it work?
Symmetric key encryption involves using the same key for both encryption and decryption. In machine to machine authentication, symmetric keys are often used to encrypt and decrypt sensitive information, such as authentication tokens and credentials.
What is the role of public key infrastructure (PKI) in machine to machine authentication?
Public key infrastructure (PKI) plays a critical role in machine to machine authentication by providing a framework for securely managing and exchanging public keys between devices and systems. PKI ensures the authenticity and integrity of public keys and prevents tampering and eavesdropping.
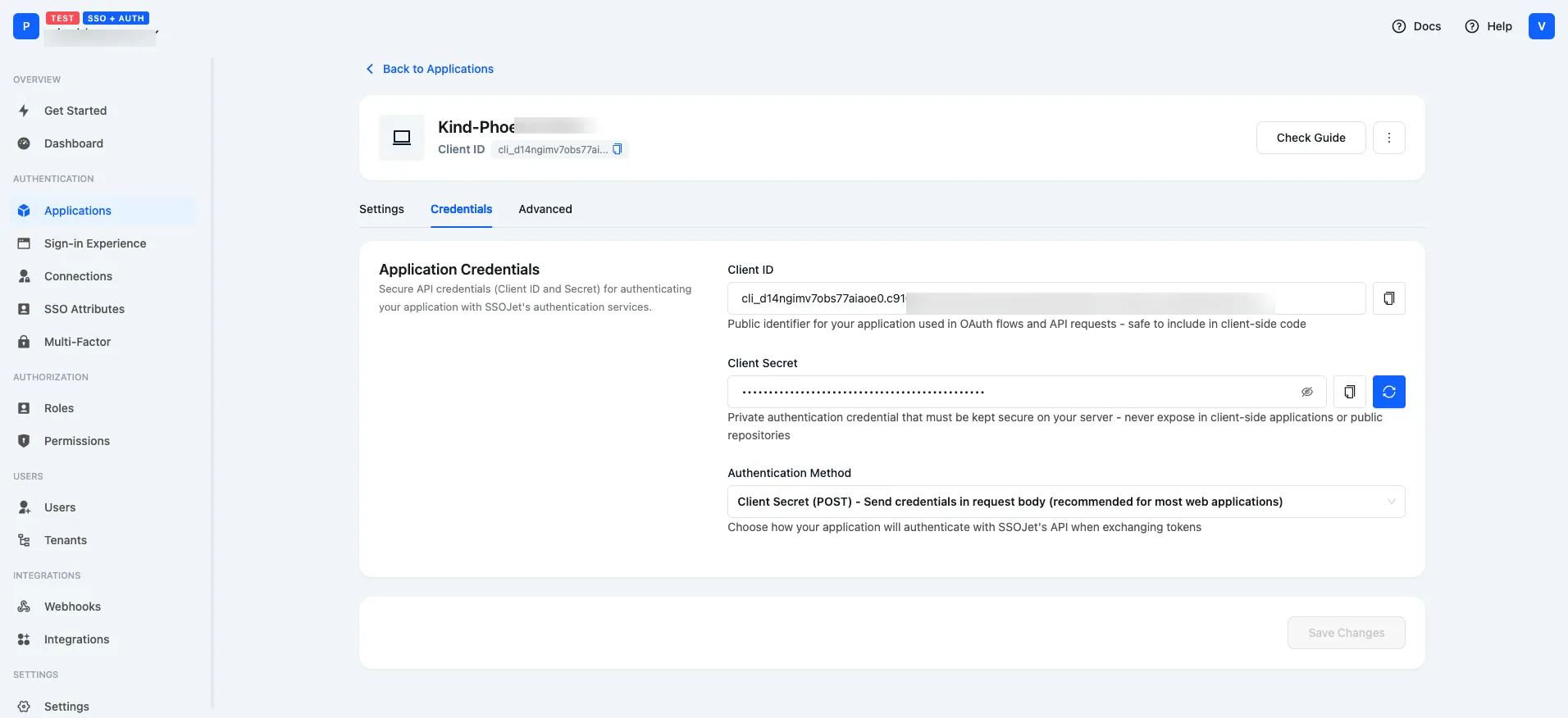
What is the difference between implicit and client-secret grant types in OAuth?
The implicit grant type involves redirecting the user’s browser to the authorization server, while the client-secret grant type involves exchanging an authorization code for an access token.