Virtual machines on linux –
virtual machines on linux takes center stage, this opening passage beckons readers into a world crafted with good knowledge, ensuring a reading experience that is both absorbing and distinctly original with a strong focus on setup and management.
in today’s computing world, virtual machines on linux are a must-have for businesses, developers, and power users alike. with the flexibility to run multiple operating systems on a single physical host, virtual machines offer unparalleled scalability, security, and efficiency.
Introduction to Virtual Machines on Linux
Virtual machines (VMs) on Linux are a groundbreaking technology that has revolutionized the way we approach computing. At its core, a virtual machine is a software-emulated environment that runs an operating system (OS) on top of a host OS. This allows users to run multiple OSes concurrently on a single physical machine, without the need for multiple hardware configurations.
In 1960s, the concept of virtualization was first introduced by IBM, in their System/360 mainframe computers. The idea was to create a virtual computer system, where multiple virtual machines could run on a single physical machine. This concept has since evolved and matured, leading to its widespread adoption in the computing world.
The significance of virtual machines on Linux can be attributed to several benefits, including:
The benefits of using virtual machines on Linux are numerous:
Portability and Flexibility
Virtual machines provide unparalleled portability and flexibility, allowing users to run various OSes on a single machine, without the need for hardware upgrades or reconfigurations. This flexibility is especially beneficial for developers, testers, and IT professionals who need to work on multiple OS platforms.
When deploying a virtual machine, users can choose from a myriad of OS distributions, including Linux, Windows, and macOS. This ability to run multiple OSes on a single machine simplifies the development, testing, and deployment process, making it an indispensable tool for software development and IT operations.
Isolation and Security
Virtual machines isolate each virtual machine from the host OS and other virtual machines, ensuring that any potential security exploits or malfunctions are contained within the virtual machine. This level of isolation provides an added layer of security, as any unauthorized access or malicious activity within a virtual machine cannot affect the host OS or other virtual machines.
Cost-Effectiveness
Virtual machines are a cost-effective solution for organizations and individuals alike. By running multiple virtual machines on a single physical machine, users can significantly reduce hardware costs, as they do not need to purchase separate hardware configurations for each OS.
Furthermore, virtual machines require minimal maintenance and support, reducing the overall burden on IT teams. With the ability to snapshot, clone, and migrate virtual machines, users can easily reproduce and manage virtual environments, making it an ideal solution for testing, development, and disaster recovery.
Simplified Backup and Recovery
Virtual machines simplify the backup and recovery process by allowing users to snapshot virtual machines at regular intervals. This enables users to reproduce a previous state of the virtual machine, in the event of data loss or corruption.
With the ability to snapshot virtual machines, users can easily recover from disasters or data loss, reducing downtime and ensuring business continuity. This level of flexibility and control makes virtual machines an essential tool for any organization that relies on robust data backup and recovery processes.
Easy Testing and Development
Virtual machines make it easy to test and develop software applications, by allowing users to create isolated and controlled environments for testing and development. This ability to quickly reproduce and manage virtual environments enables users to rapidly iterate and refine their software products, making virtual machines an indispensable tool for software development teams.
With the ability to snapshot, clone, and migrate virtual machines, users can easily reproduce and manage virtual environments, making it an ideal solution for testing, development, and disaster recovery.
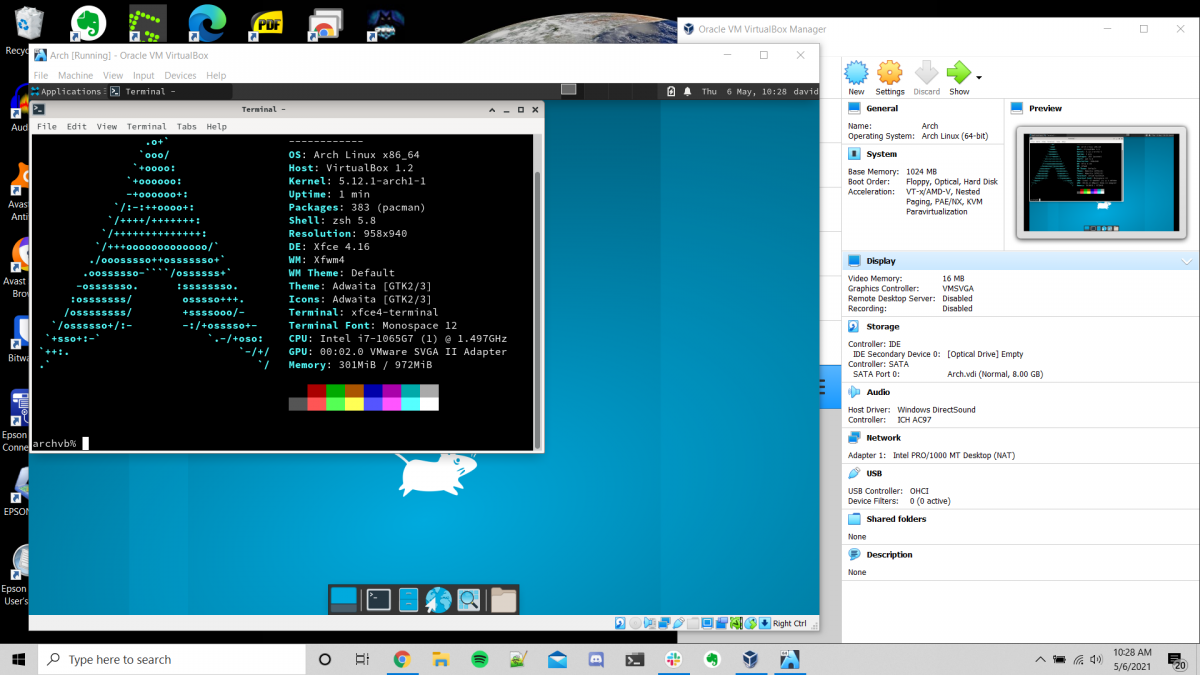
Types of Virtual Machines on Linux
Virtual machines on Linux provide users with the flexibility to run multiple operating systems on a single physical host, each with its own set of applications and resources. The choice of virtual machine depends on the user’s requirements, ranging from simple development environments to complex enterprise applications. In this section, we will explore the different types of virtual machines available on Linux and their key features.
Xen Virtual Machine
Xen is a type-1 hypervisor, meaning it sits directly on top of the host machine’s hardware, providing the necessary platform for other operating systems to run. It supports multiple virtualization modes, including fully virtualized and paravirtualized environments.
- Xen offers high performance and efficiency, making it suitable for server virtualization.
- It supports live migration, allowing virtual machines to be moved between hosts without downtime.
- Xen has a large community of developers and users, ensuring the availability of resources and support.
KVM Virtual Machine
KVM (Kernel-based Virtual Machine) is a type-1 hypervisor that utilizes the host machine’s kernel to provide virtualization capabilities. It supports both 2D and 3D acceleration, making it suitable for graphics-intensive applications.
- KVM offers high performance and low latency, making it suitable for gaming and other latency-sensitive applications.
- It supports hardware acceleration for virtual machines, improving performance and efficiency.
- KVM has a large community of developers and users, ensuring the availability of resources and support.
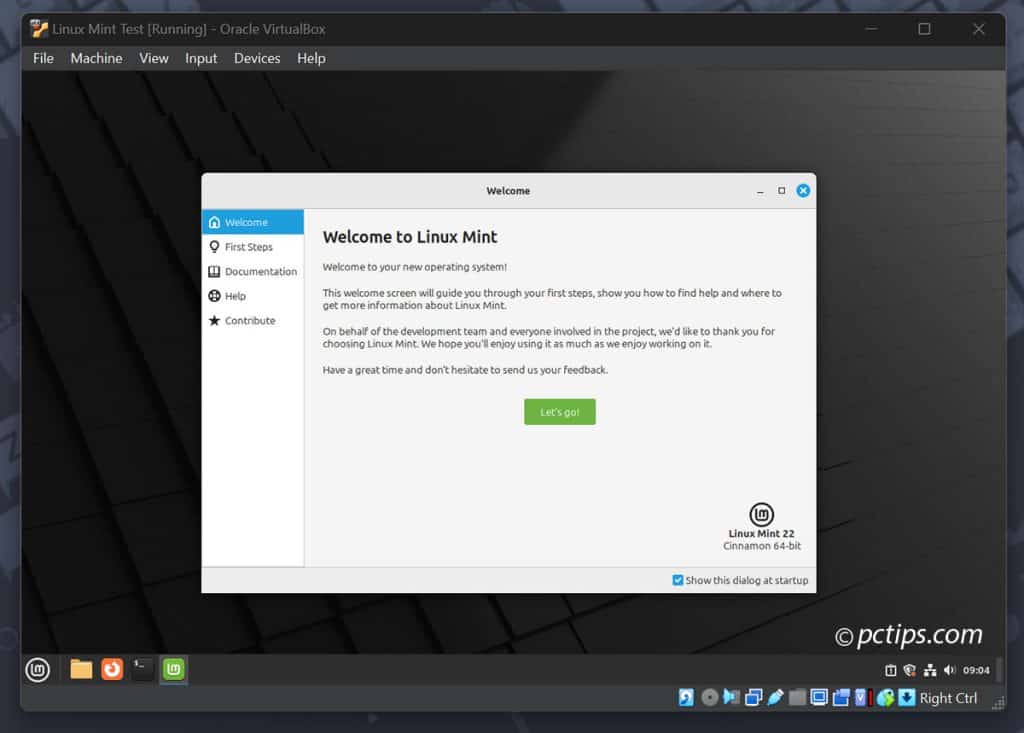
VirtualBox Virtual Machine
VirtualBox is a type-2 hypervisor that sits on top of the host machine’s operating system, providing virtualization capabilities. It supports a wide range of guest operating systems and offers advanced features such as snapshotting and cloning.
- VirtualBox offers high flexibility and portability, making it suitable for development and testing environments.
- It supports virtual networking, allowing virtual machines to communicate with each other.
- VirtualBox has a user-friendly interface and is relatively easy to set up and use.
VMware Virtual Machine
VMware is a type-2 hypervisor that offers advanced virtualization capabilities, including virtualization of hardware components such as disk controllers and network cards. It supports a wide range of guest operating systems and offers features such as snapshots and clustering.
- VMware offers high performance and security, making it suitable for enterprise environments.
- It supports virtual machines with multiple virtual network interfaces and VLAN support.
- VMware has a large community of developers and users, ensuring the availability of resources and support.
System Requirements for Virtual Machines
The system requirements for virtual machines depend on the host machine’s hardware and software configuration. In general, virtual machines require:
- Adequate CPU resources, including multiple cores and threads.
- Sufficient memory (RAM) to support the virtual machines and their applications.
- A fast disk subsystem, including a solid-state drive (SSD) or high-performance hard disk drive.
- A network interface, either physical or virtual, to support communication between virtual machines and the host machine.
Installing and Setting Up Virtual Machines on Linux
Installing virtual machines on Linux can seem daunting at first, but with the right tools and a bit of guidance, it’s a straightforward process. Linux offers a wide range of virtualization tools, each with its own strengths and weaknesses. In this section, we’ll cover the process of installing and setting up virtual machines on Linux using popular virtualization tools.
Choosing a Virtualization Tool
The first step in installing a virtual machine on Linux is to choose a virtualization tool. Some popular options include VirtualBox, KVM, and Xen. Each tool has its own set of features and requirements, so it’s essential to consider your needs before making a decision.
Here are some key factors to consider when choosing a virtualization tool:
- Hardware requirements: Some virtualization tools require a VT-x or AMD-V capable CPU, while others can run on older hardware.
- Platform support: Some tools are designed for specific distributions, such as Ubuntu or CentOS, while others are more flexible.
- Feature set: Some tools offer advanced features like snapshotting, live migration, and storage management.
- Community support: Consider the size and activity of the tool’s user community and documentation.
Installing VirtualBox
VirtualBox is a popular and widely-supported virtualization tool. Here’s a step-by-step guide to installing it on Ubuntu:
First, update your package list:
sudo apt update
Then, install VirtualBox using the following command:
sudo apt install virtualbox
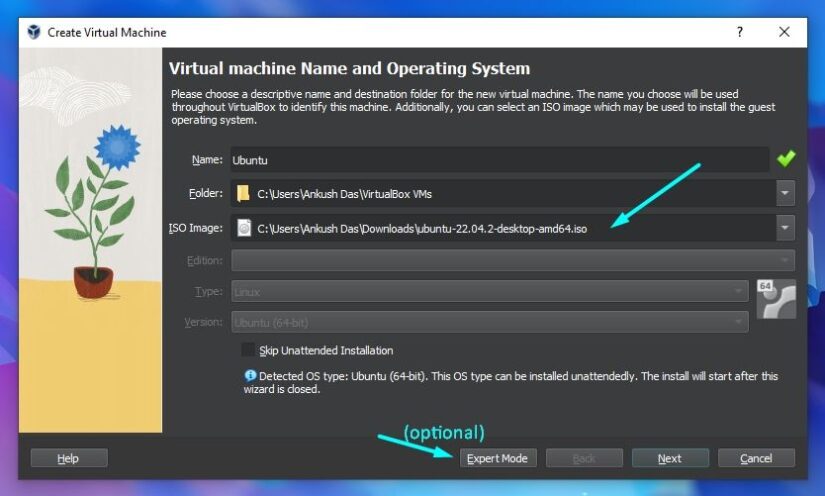
Configuring Virtual Machines
Once you’ve installed your virtualization tool, it’s time to set up your virtual machines. Here are some key configuration options to consider:
RAM allocation: Allocate enough RAM to run your virtual machine smoothly. A good rule of thumb is to allocate at least 2GB of RAM per virtual machine.
CPU allocation: You can allocate multiple CPU cores to your virtual machine, depending on its requirements.
Networking: You can configure your virtual machine to use bridged networking, NAT networking, or host-only networking.
Storage: You can configure your virtual machine to use a virtual hard drive or a shared folder.
Example Configuration
Here’s a real-world example of configuring a virtual machine using VirtualBox:
Create a new virtual machine with the following specifications:
- RAM allocation: 4GB
- CPU allocation: 2 cores
- Networking: Bridged networking
- Storage: 20GB virtual hard drive
Save your changes and start the virtual machine. Your virtual machine should now be up and running, with a bridged networking configuration and a 20GB virtual hard drive.
Advanced Configuration Options
Some virtualization tools offer advanced configuration options that can enhance your virtual machine’s performance and security. Here are a few examples:
Snapshotting: Some virtualization tools offer snapshotting capabilities, which allow you to capture the state of your virtual machine at a particular point in time. This can be useful for testing and development.
Live migration: Some virtualization tools offer live migration capabilities, which allow you to move your virtual machine between hosts without disrupting its operation.
Storage management: Some virtualization tools offer advanced storage management capabilities, which allow you to manage your virtual machine’s storage needs.
Configuring Networking for Virtual Machines on Linux
Configuring networking for virtual machines (VMs) on a Linux host is a crucial step in setting up a virtualization environment. It involves setting up the networking stack to allow VMs to communicate with each other and with the external network. In this section, we will cover the different network configurations for VMs on Linux and provide examples of how to configure them.
NAT Network Configuration, Virtual machines on linux
One of the simplest ways to configure networking for VMs is to use NAT (Network Address Translation). NAT allows a single IP address to be shared by multiple VMs, and it is a good choice for development, testing, and other use cases where the VMs do not need direct access to the external network. To configure NAT, you need to set up a NAT bridge on the Linux host and then create virtual NICs for each VM.
IP forwarding can be enabled on the Linux host to allow NAT.
To enable IP forwarding, you need to add the following lines to the /etc/sysctl.conf file:
net.ipv4.ip_forward = 1
Then, you need to restart the network service using systemctl restart network or service networking restart (on RHEL/CentOS systems).
Here is an example of how to create a NAT bridge:
“`bash
sudo brctl addbr vmbr0
sudo ip addr add 10.10.10.1/24 dev vmbr0
sudo ip link set vmbr0 up
“`
Then, create virtual NICs for each VM:
“`bash
sudo ip addr add 10.10.10.2/24 dev eth0 label eth0:0
sudo ip link set eth0:0 up
“`
Bridged Network Configuration
Bridged networking allows VMs to access the external network directly. This is the most common configuration used in production environments. To configure bridged networking, you need to create a bridge interface on the Linux host and attach virtual NICs to the bridge interface. You also need to set up the network on the Linux host to use the bridge interface as the default interface.
The bridge interface must be created with the same IP address and netmask as the physical network interface.
Here is an example of how to create a bridge interface:
“`bash
sudo brctl addbr vmbr0
sudo ip addr add 192.168.1.1/24 dev vmbr0
sudo ip link set vmbr0 up
“`
Then, create virtual NICs for each VM:
“`bash
sudo ip addr add 192.168.1.2/24 dev eth0 label eth0:0
sudo ip link set eth0:0 up
“`
Routing Network Configuration
Routing networking allows VMs to access multiple networks by setting up a routing table on the Linux host. This is useful when you need to access different networks from within the VM. To configure routing networking, you need to set up the network on the Linux host to use the default route to the external network and then create a routing table for each VM.
The routing table must be created with the network address and netmask of the external network.
Here is an example of how to create a routing table:
“`bash
sudo ip route add default via 192.168.1.1 dev eth0
“`
Then, create a routing table for each VM:
“`bash
sudo ip route add 10.10.10.0/24 via 10.10.10.1 dev vmbr0
“`
Sharing and Managing Resources on Virtual Machines on Linux
Sharing and managing resources between virtual machines is a crucial aspect of efficiently utilizing your Linux host machine’s capabilities. By understanding how to allocate and manage resources effectively, you can optimize your virtual machine setup for improved performance and productivity. In this section, we will explore the different methods for sharing and managing resources, including CPU, memory, and storage, as well as how to use virtual network interfaces to manage traffic between virtual machines.
CPU and Memory Resource Management
CPU and memory resource management is a critical aspect of virtual machine setup. Linux provides various tools and methods for managing these resources, ensuring optimal utilization and minimizing resource waste.
*
cpuset: a way to assign a specific set of cpus to a particular virtual machine.
*
- Use the cpuset command to create and manage CPU sets.
- Assign the created CPU sets to virtual machines using the cgroups feature.
Storage Resource Management
Storage resource management involves allocating and managing storage space for virtual machines. Linux provides various tools and methods for managing storage resources, including:
*
- LVM (Logical Volume Manager): a tool for creating and managing logical volumes for virtual machines.
- Mounting file systems: mounting file systems from the host machine to virtual machines.
- Networking file systems: using network file systems such as NFS and CIFS to share storage resources between virtual machines.
Virtual Network Interfaces for Traffic Management
Virtual network interfaces (VNICs) play a crucial role in managing traffic between virtual machines. VNICs allow virtual machines to communicate with each other and the host machine’s network stack.
*
- VLANs (Virtual Local Area Networks): a way to isolate virtual machines on the same network.
- VXLANs (Virtual eXtensible Local Area Networks): a way to extend VLANs across multiple networks.
- SR-IOV (Single Root Input/Output Virtualization): a technology that allows multiple virtual machines to share the same physical network interface.
Automating Resource Management with Scripting Tools
Scripting tools such as Python and bash can be used to automate resource management tasks. Here are some examples of how to use these tools to automate resource management:
*
- Use Python’s py-cgroup library to manage cgroups and CPU sets.
- Use bash’s cgroups feature to manage CPU sets and allocate resources to virtual machines.
Security Considerations for Virtual Machines on Linux
Running virtual machines on Linux can introduce unique security risks that must be addressed to ensure the overall security and integrity of your system. One of the primary concerns is that virtual machines can be used as a potential entry point for malicious actors, allowing them to gain access to your host machine and other virtual machines. Additionally, virtual machines can also be used to host unauthorized or malicious software, which can further compromise your system’s security.
Firewall Rules for Virtual Machines
Configuring firewall rules for virtual machines is essential to control incoming and outgoing traffic. You can use tools like `firewalld` or `iptables` to set up rules for your virtual machines. For example, you can allow incoming traffic on specific ports for certain protocols, such as SSH or HTTP, while blocking all other traffic.
- Use network namespace isolation to ensure that each virtual machine has its own network namespace.
- Configure firewall rules to allow only necessary traffic for each virtual machine.
- Use secure communication protocols, such as SSH, HTTPS, and SMB, to communicate with virtual machines.
Access Controls for Virtual Machines
Implementing access controls for virtual machines is crucial to ensure that only authorized users have access to them. You can use tools like `virt-manager` or `libvirt` to manage access to your virtual machines. For example, you can set up user permissions to manage virtual machines, or use encryption to secure the data stored on virtual machines.
- Use secure authentication protocols, such as SSH keys, to access virtual machines.
- Configure access controls to restrict user access to virtual machines and their resources.
- Use encryption to secure data stored on virtual machines.
Example: Implementing Secure Virtualization on a Linux Host
To implement secure virtualization on a Linux host, you can use the following example:
Use a Linux distribution like Ubuntu or CentOS, which has built-in support for `libvirt` and `virt-manager`. Create a virtual machine with a secure configuration, including firewall rules and access controls. Use a secure authentication protocol, such as SSH keys, to access the virtual machine. Encrypt the data stored on the virtual machine using tools like `cryptsetup`.
By following these best practices and implementing secure virtualization on your Linux host, you can minimize the risks associated with running virtual machines and ensure a secure and reliable environment for your applications and data.
Best Practices for Running Virtual Machines on Linux
Running virtual machines on Linux requires a combination of technical knowledge, attention to detail, and adherence to best practices. By following these guidelines, you can ensure your virtual machine infrastructure is stable, secure, and efficient. Effective management of virtual machines is essential for maximizing performance, reliability, and scalability in a Linux environment.
Monitoring Performance
Monitoring virtual machine performance is crucial for identifying bottleneck, optimizing resource allocation, and preventing bottlenecks. Here are key aspects to consider when monitoring virtual machine performance:
- Track CPU, memory, and disk usage: Monitor these resources to ensure optimal allocation and prevent resource contention.
- Use resource metering tools: Utilize tools like vmstat, iostat, and mpstat to collect resource utilization data.
- Set thresholds and alerts: Establish warning and critical thresholds for resource utilization and configure alerting systems to notify administrators of potential issues.
- Analyze performance metrics: Regularly review performance data to identify trends, bottlenecks, and areas for optimization.
Updating Software
Staying up-to-date with the latest software updates is essential for securing and optimizing virtual machine performance. Here are key considerations for software updates:
- Regularly update kernels and virtualization software: Keep your kernel and virtualization software current to ensure access to the latest security patches and performance enhancements.
- Patch virtual appliance templates: Keep your virtual appliance templates up-to-date to prevent exploits and ensure compatibility with the latest Linux distributions.
- Run software updates on virtual machines: Regularly update software on your virtual machines to prevent security vulnerabilities and ensure compatibility with other components.
- Automate patching and updates: Leverage automation tools or scripting to streamline the update process and minimize downtime.
Backup and Recovery
Implementing a robust backup and recovery strategy is critical for ensuring the integrity and availability of virtual machines. Here are key considerations for virtual machine backup and recovery:
- Develop a comprehensive backup plan: Establish clear backup schedules, retention policies, and recovery procedures to ensure business continuity.
- Use backup software: Leverage specialized backup software designed for virtual machines, such as NFS or DD backup tools.
- Test backup and recovery procedures: Regularly test your backup and recovery procedures to ensure their effectiveness in case of a disaster.
- Store backups securely: Ensure backup storage is secure, accessible, and easily recoverable in case of an emergency.
Automation and Scripting
Automation and scripting can significantly streamline virtual machine management, improving efficiency, and reducing errors. Here are key aspects to consider when implementing automation and scripting:
- Script virtual machine creation and configuration: Automate the creation and configuration of virtual machines using scripting tools like Bash or Perl.
- Implement automated backup and recovery: Leverage scripting to automate backup and recovery procedures, ensuring timely and accurate data protection.
- Monitor and analyze virtual machine performance: Utilize automation and scripting to collect and analyze performance data, highlighting trends and potential issues.
- Automate software updates and patching: Streamline the update process using automation and scripting, ensuring your virtual infrastructure remains secure and up-to-date.
Automation and scripting are critical components of a robust virtual infrastructure, enabling administrators to efficiently manage resources, reduce errors, and ensure high availability.
Troubleshooting Virtual Machines on Linux
Troubleshooting virtual machines on Linux can be a challenging task, but with the right approach and tools, you can resolve common issues and keep your virtual environment running smoothly. This section covers common issues and errors that can occur when running virtual machines on Linux, step-by-step troubleshooting procedures, and the importance of logging and monitoring for virtual machines.
Common Issues and Errors
Virtual machines on Linux can experience a range of issues, including:
- Instability or crashes
- Networking problems
- Storage issues
- Performance problems
- Security vulnerabilities
These issues can be caused by a variety of factors, including hardware problems, software conflicts, or misconfigured virtual machine settings.
Step-by-Step Troubleshooting Procedures
When troubleshooting virtual machines on Linux, follow these steps:
- Check the virtual machine console logs for error messages
- Verify the virtual machine’s hardware configuration
- Check for software updates and apply them
- Review the virtual machine’s network settings
- Run a virus scan and malware scan
These steps can help you identify and resolve common issues with your virtual machines.
Importance of Logging and Monitoring
Logging and monitoring are essential for virtual machines on Linux. They allow you to track the virtual machine’s performance, identify potential issues, and troubleshoot problems before they become major issues.
Regularly review your virtual machine’s logs and error messages to stay on top of potential problems
Common Linux Tools for Troubleshooting Virtual Machines
Several Linux tools can help you troubleshoot virtual machines, including:
- vmware.log
- VirtualBox logs
- KVM logs
- Systemd logs
These tools provide detailed information about the virtual machine’s performance, including error messages, system calls, and resource usage.
Best Practices for Troubleshooting Virtual Machines
To troubleshoot virtual machines effectively, follow these best practices:
- Keep your virtual machine’s software up to date
- Regularly back up your virtual machine’s data
- Monitor your virtual machine’s performance regularly
- Use logging and monitoring tools to track potential issues
- Document your troubleshooting steps and solutions
These best practices can help you resolve issues quickly and keep your virtual environment running smoothly.
Virtual Machine Backup and Recovery
Virtual machine backup and recovery is essential for protecting your data and reducing downtime. Regularly backup your virtual machine’s data and configuration, and keep multiple backups in case of a disaster.
Virtually backup your virtual machine’s data and configuration regularly to prevent data loss and downtime.
Ultimate Conclusion
and so, this comprehensive guide comes to a close, leaving you with a solid understanding of virtual machines on linux, from setup and management to security and best practices. armed with this knowledge, you’ll be able to harness the full potential of virtualization on your linux machines, transforming the way you work and empowering your systems to deliver more.
Question Bank: Virtual Machines On Linux
Can i run windows on a linux host?
yes, you can run windows on a linux host using virtual machines, but it will require additional software and setup. popular virtualization tools like virtualbox and vmware support running windows on linux.
How do i manage resources on multiple virtual machines?
resource management on multiple virtual machines can be done using tools like virtual network interfaces, cpu and memory allocation, and automated resource management using scripting tools like python and bash.
Is it secure to run multiple virtual machines on a single host?
running multiple virtual machines on a single host can increase security risks, but this can be mitigated by using secure virtualization tools, firewall rules, and access controls.