Delving into bytecode vs machine code, this introduction immerses readers in a unique narrative that explores the intricate world of software development. At its core, bytecode vs machine code is a battle of two approaches: one that prioritizes platform independence and the other that seeks raw performance.
The history of bytecode and machine code dates back to the early days of computing, with pioneers like Alan Turing and John von Neumann laying the groundwork for modern computer architectures. As high-level programming languages like C and Pascal gained popularity, the need for efficient compilation arose. This led to the development of just-in-time (JIT) compilation and virtual machines, further blurring the lines between bytecode and machine code.
Character Encoding in Bytecode
Character encoding in bytecode plays a crucial role in determining how the computer interprets the code. Unlike machine code, which relies on binary encoding, bytecode uses a more complex encoding scheme that can handle different character sets and languages. In this section, we will explore the character encoding schemes used in machine code and bytecode, discuss the impact of character encoding on programming languages, and explain how bytecode handles different character encodings.
Character Encoding Schemes in Machine Code
Machine code uses binary encoding, which represents data as either 0 or 1. The most common character encoding schemes in machine code are ASCII (American Standard Code for Information Interchange) and EBCDIC (Extended Binary Coded Decimal Interchange Code). ASCII is the most widely used character encoding scheme and is the default for most computer systems. It assigns a unique binary code to each character, allowing for the representation of letters, numbers, and symbols.
ASCII has several limitations, including:
- It only supports characters from the English alphabet and a limited set of special characters.
- It does not support non-English languages or special characters.
- It uses a fixed-length encoding, which can lead to inefficient use of space.
EBCDIC is another character encoding scheme used in mainframe computers and some older systems. It is also a fixed-length encoding scheme that is less widely used than ASCII.
Character Encoding Schemes in Bytecode
Bytecode, on the other hand, uses a more complex encoding scheme that can handle different character sets and languages. The most common character encoding schemes in bytecode are Unicode and UTF-8 (Unicode Transformation Format – 8-bit).
Unicode is a character encoding scheme that assigns a unique binary code to each character from any language or culture. It is the default character encoding scheme for most modern programming languages, including Java, Python, and C++. Unicode supports over 140,000 characters from more than 100 languages.
UTF-8 is a variable-length encoding scheme that is an extension of Unicode. It is designed to be backward compatible with ASCII and can represent any Unicode character using one to four bytes.
Bytecode handles different character encodings through the following mechanisms:
- Character encoding detection: Bytecode can detect the character encoding of the input code and perform the necessary conversions.
- Encoding conversion: Bytecode can convert the character encoding of the code to match the requirements of the target platform.
- Language support: Bytecode supports a wide range of languages and character sets, making it a popular choice for cross-platform development.
Impact of Character Encoding on Programming Languages
Character encoding has a significant impact on programming languages, particularly when it comes to language support and data transmission. The choice of character encoding scheme can affect the way a programming language represents characters, which can impact the language’s syntax and semantics.
For example, the Python programming language uses Unicode as its default character encoding scheme. This allows Python to support characters from any language or culture, making it a popular choice for cross-platform development.
Impact of Character Encoding on Data Transmission
Character encoding also affects data transmission, particularly when it comes to text data. The choice of character encoding scheme can impact the way data is transmitted over a network or written to a file.
For example, the UTF-8 character encoding scheme is widely used for text data transmission over the internet. This is because UTF-8 is designed to be backward compatible with ASCII and can represent any Unicode character using one to four bytes.
Conclusion, Bytecode vs machine code
In conclusion, character encoding in bytecode plays a crucial role in determining how the computer interprets the code. Bytecode uses a more complex encoding scheme that can handle different character sets and languages, unlike machine code, which relies on binary encoding. The choice of character encoding scheme can impact the way a programming language represents characters, which can impact the language’s syntax and semantics.
Compilers and Interpreters
Compilers and interpreters are two fundamental components of programming environments that play a crucial role in converting high-level code into machine executable code. They serve as the backbone of programming languages, facilitating the transition from developer-friendly code to efficient machine code.
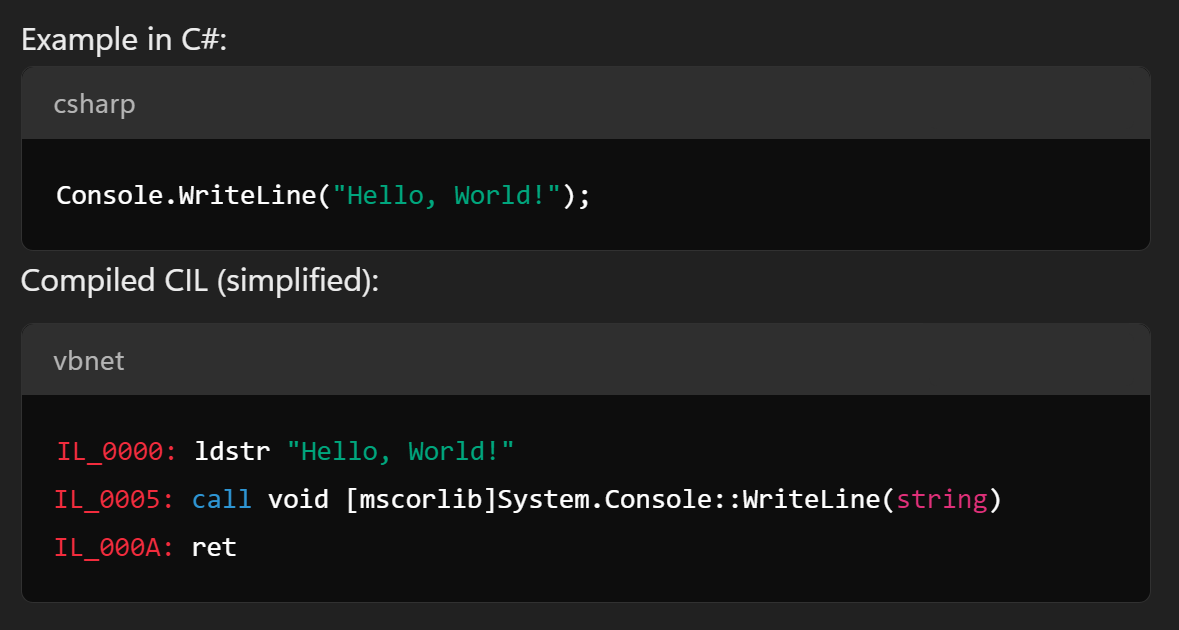
Role of Compilers in Converting High-Level Code to Machine Code and Bytecode
Compilers are programs that take high-level source code as input and generate machine executable code or bytecode as output. The primary function of a compiler is to translate the source code into a format that can be executed directly by the computer’s processor. Compilers typically work in a compile-time, meaning they analyze the source code and generate machine code in a single step. This process involves several stages, including:
* Lexical analysis: Breaking down the source code into individual tokens
* Syntax analysis: Verifying the syntax of the source code
* Semantic analysis: Checking the meaning of the source code
* Intermediate code generation: Creating intermediate code that can be optimized
* Optimization: Improving the efficiency of the intermediate code
* Code generation: Producing machine executable code
However, compilers can also generate bytecode, which is an intermediate form of code that can be executed by a virtual machine.
Role of Compilers in Converting High-Level Code to Bytecode
While compilers primarily generate machine executable code, some compilers can also produce bytecode. This bytecode can be executed by a virtual machine, eliminating the need for a separate compilation step. Bytecode compilers, such as those used in Java and Python, take high-level source code and generate bytecode that can be executed by a virtual machine. This approach offers several benefits, including:
* Platform independence: Bytecode can be executed on any platform that supports the virtual machine
* Dynamic compilation: Bytecode can be compiled just-in-time, reducing compilation overhead
* Security: Bytecode provides a higher level of security by limiting the code that can be executed directly by the computer’s processor
Trade-offs between Compilers and Interpreters
Compilers and interpreters have distinct characteristics that make them suitable for various scenarios.
- Advantages of Interpreters
* Faster development and testing: Interpreters allow for rapid interpretation and execution of code
* Error handling: Interpreters can handle errors and provide feedback to the developer
* Dynamic execution: Interpreters can execute code dynamically, without the need for a separate compilation step
However, interpreters typically suffer from performance penalties due to the interpretation process. This can result in slower execution times and reduced overall performance.
- Advantages of Compilers
* Faster execution: Compiled code executes directly on the computer’s processor, resulting in faster execution times
* Improved performance: Compilers can optimize code for performance, reducing the overhead of interpretation
* Security: Compiled code provides a higher level of security by limiting the code that can be executed directly by the computer’s processor
However, compilers can introduce additional complexity and overhead due to the compilation process.
Just-in-Time (JIT) Compilation
JIT compilation is a technique that combines the benefits of interpreters and compilers. JIT compilers translate high-level code into machine executable code at runtime, often using the interpretation overhead to compensate for compilation overhead. This approach offers several benefits, including:
* Improved performance: JIT compilation can provide performance benefits similar to those of compilers
* Platform independence: JIT compilation can execute code on any platform that supports the virtual machine
* Dynamic compilation: JIT compilation can compile code just-in-time, reducing compilation overhead
However, JIT compilation can introduce additional overhead due to the compilation process and may not always provide performance benefits.
Security Considerations for Bytecode and Machine Code: Bytecode Vs Machine Code
Security is a crucial aspect to consider when working with bytecode and machine code. Bytecode, being a platform-independent code, faces unique security risks that can lead to data breaches and system compromise. Similarly, machine code, being specific to a particular architecture, can be vulnerable to reverse engineering and exploitation.
Potential Security Risks Associated with Bytecode
Bytecode execution environments, such as the Java Virtual Machine (JVM), address security concerns through sandboxing and memory management. However, some potential security risks associated with bytecode include:
- Code injection attacks: Malicious code can be injected into the bytecode, allowing attackers to execute unauthorized code.
- Deserialization attacks: Deserialization of untrusted data can lead to remote code execution and arbitrary code injection.
- Information leakage: Bytecode can leak sensitive information, such as memory contents, stack frames, or CPU registers.
These security risks are mitigated by implementing robust sandboxing and memory management in bytecode execution environments. The JVM, for example, uses a combination of sandboxes and memory protection to prevent unauthorized code execution and information leakage.
Potential Security Risks Associated with Machine Code
Machine code, being specific to a particular architecture, can be vulnerable to reverse engineering and exploitation. Some potential security risks associated with machine code include:
- Reverse engineering: Malicious actors can reverse engineer machine code to discover sensitive information, such as cryptographic keys or authentication tokens.
- Buffer overflows: Machine code can be vulnerable to buffer overflows, allowing attackers to execute arbitrary code or crash the system.
- Exploitation of architecture-specific vulnerabilities: Machine code can exploit vulnerabilities specific to a particular architecture, such as the Spectre and Meltdown vulnerabilities in modern CPUs.
These security risks can be mitigated by implementing techniques such as obfuscation, code signing, and vulnerability hardening. Obfuscation can make it more difficult for attackers to reverse engineer machine code, while code signing can ensure that machine code is executed only if it is digitally signed by a trusted entity.
T Techniques to Improve the Security of Machine Code
Machine code can be made more secure through various techniques:
-
Code obfuscation
can make it more difficult for attackers to reverse engineer machine code, by introducing unnecessary complexity and making it harder to identify patterns.
- Code
signing
can ensure that machine code is executed only if it is digitally signed by a trusted entity, preventing unauthorized code execution.
-
Vulnerability hardening
can be used to prevent exploitation of architecture-specific vulnerabilities, by patching vulnerabilities and implementing mitigations.
By implementing these techniques, machine code can be made more secure, reducing the risk of reverse engineering and exploitation.
Comparison of Performance

In the realm of programming, performance is a critical aspect to consider when evaluating bytecode and machine code. The choice between these two forms of code can significantly impact the responsiveness and throughput of an application. In this section, we will delve into the performance characteristics of bytecode and machine code, and explore how the choice between them affects application performance.
Advantages of Bytecode
Bytecode is a crucial aspect of many programming languages, such as Java and Python. When bytecode is executed, it undergoes just-in-time (JIT) compilation or interpretation, which enables it to adapt to changing system conditions. This flexibility allows bytecode to provide several performance benefits, including:
- Predictable Performance: Bytecode execution is typically more efficient than traditional compilation, as it can adapt to changing system conditions.
- Dynamic Memory Allocation: Bytecode can handle dynamic memory allocation more effectively, reducing memory-related issues.
- Platform Independence: Bytecode can run on multiple platforms without requiring recompilation, making it an attractive choice for cross-platform development.
However, bytecode also has some performance limitations, particularly when dealing with computationally intensive tasks or low-latency requirements.
Advantages of Machine Code
Machine code, on the other hand, is the lowest-level representation of programming languages and is executed directly by the CPU. Machine code provides the following performance benefits:
- Native Execution: Machine code is executed natively by the CPU, resulting in minimal overhead and optimal performance.
- Low Latency: Machine code can achieve lower latency than bytecode, particularly for real-time systems or applications that require rapid response times.
- High Performance: Machine code can leverage CPU-level optimizations, making it a suitable choice for computationally intensive tasks.
However, machine code also has some limitations, particularly when it comes to portability and maintainability.
Choosing Between Bytecode and Machine Code
When deciding between bytecode and machine code, consider the specific requirements of your application. If you need high performance, low latency, and platform independence, machine code may be the better choice. However, if you prioritize ease of development, flexibility, and adaptability, bytecode may be more suitable.
Remember that the choice between bytecode and machine code also depends on the programming language and development framework being used. Certain languages, such as Java, are specifically designed to work with bytecode, while others, like C++, may be more suited to machine code.
Ultimately, the decision between bytecode and machine code comes down to the specific needs of your application. By understanding the performance characteristics of each, you can make an informed decision and choose the best approach for your project.
Case Studies and Real-World Examples
Bytecode has been successfully employed in numerous real-world systems across various domains, including Java, Ruby, and many others. In this section, we will delve into several prominent case studies that illustrate the benefits and drawbacks of using bytecode, as well as its impact on performance and reliability.
Java Bytecode in Android App Development
Java bytecode plays a crucial role in Android app development due to the use of the Java Virtual Machine (JVM) by the Android Runtime (ART). The use of bytecode in Android development offers several advantages, including platform independence, ease of development, and improved security. For instance, Android applications are compiled into bytecode and then executed on the ART, which provides several performance optimisations.
*
Dalvik Virtual Machine
The Dalvik Virtual Machine was the original runtime environment for Android apps. It used a Just-In-Time (JIT) compiler, which transformed bytecode into native machine code at runtime. Although the Dalvik Virtual Machine was efficient, it had limitations, including slower startup times compared to subsequent versions of Android.
*
ART and AOT Compilation
With the introduction of ART, the Android Runtime moved towards Ahead-Of-Time (AOT) compilation. This approach involved converting bytecode into native machine code before runtime. ART provides improved performance and faster startup times compared to Dalvik.
“ART’s AOT compilation approach offers improved performance and faster startup times for Android applications.”
Bytecode in Ruby
Ruby bytecode is also employed in the Ruby VM, known as YARV (Yet Another Ruby VM). Although Ruby is often associated with dynamic typing and compilation, the YARV VM uses a bytecode approach to optimize execution speed.
YARV and Performance
Using bytecode in YARV enables several performance enhancements, including:
*
- Code caching for repeated execution of the same method calls.
* Just-In-Time (JIT) compilation for methods that are frequently called.
* Profile-guided optimization to minimize execution time for frequently accessed code blocks.
Security Considerations for Bytecode
While bytecode offers several benefits, it is not immune to security vulnerabilities. Malicious code can still be embedded within bytecode, and runtime environments can be susceptible to attacks.
For instance, a buffer overflow vulnerability in the Dalvik VM could lead to unauthorized code execution within the context of an Android app.
- Buffer overflow attack on Dalvik VM.
- Execution of arbitrary code due to buffer overflow.
- Potential compromise of sensitive data within the app.
- Malware distribution through compromised app.
Outcome Summary
Throughout this discussion, we’ve explored the realms of bytecode and machine code, shedding light on their respective strengths and weaknesses. From the benefits of platform independence to the pursuit of raw performance, it’s clear that both approaches have their place in the world of software development. As developers continue to push the boundaries of technology, the debate between bytecode and machine code will undoubtedly persist, driving innovation and growth in the industry.
FAQs
What is the primary difference between bytecode and machine code?
Bytecode is an intermediate form of code that is executed by a virtual machine, while machine code is the binary code that is directly executed by the computer’s processor.
Can bytecode be executed directly by the computer’s processor?
No, bytecode requires a virtual machine to execute it, whereas machine code can be executed directly by the processor.
What is the benefit of using bytecode over machine code?
Bytecode provides platform independence, allowing programs to run on multiple platforms without modification.
Can machine code be made more secure through techniques like obfuscation?