Delving into copy gpg keys from other machine using scp, this introduction immerses readers in a unique and compelling narrative. Secure communication plays a vital role in today’s digital landscape.
The concept of GPG keys, their purpose, and scenarios where copying GPG keys from one machine to another is necessary set the foundation for understanding the importance of GPG key management. In addition, the SCP protocol is a widely-used method for securely transferring files between servers.
Introduction to Copying GPG Keys with SCP: Copy Gpg Keys From Other Machine Using Scp
In the digital age, secure communication is more crucial than ever. GPG keys play a vital role in this process, ensuring that our digital messages remain encrypted and protected from prying eyes. But what exactly are GPG keys, and why do we need to copy them from one machine to another?
GPG keys, short for GNU Privacy Guard keys, are pairs of cryptographic keys used for encryption and decryption. They are the backbone of secure communication, allowing individuals and organizations to send and receive sensitive information with confidence. Imagine a locked box, where only the person with the corresponding key can unlock it. This is the concept behind GPG keys.
When we need to send or receive sensitive information, such as emails or files, we use our GPG keys to encrypt and decrypt the data. This ensures that even if the information is intercepted, it remains unreadable without the corresponding key.
So, when do we need to copy GPG keys from one machine to another? There are several scenarios where this becomes necessary:
* Machine migration: When switching from an old machine to a new one, we need to transfer our GPG keys to ensure continuity in secure communication.
* Collaboration: When working with a team or organization, we may need to share our GPG keys to enable secure communication and collaboration.
* Backup: In case of data loss or system failure, copying our GPG keys ensures that we can recover our encryption capabilities.
Now, let’s dive into the world of SCP, the protocol used for copying GPG keys from one machine to another.
SCP Protocol Overview
SCP, or Secure CoPy, is a protocol designed for secure data transfer. It uses cryptography to ensure that the data transferred is authentic and not tampered with during transmission. SCP is often used in situations where data needs to be transferred securely over a network.
SCP works by establishing a secure connection between the sender and receiver, using public-key cryptography to authenticate the sender’s identity. Once the connection is established, the sender can send the GPG keys to the receiver.
SCP is widely used in the Linux and Unix world, and is also available on Windows. Its high security features make it an ideal choice for transferring sensitive data, including GPG keys.
Comparison of GPG Key Management Methods, Copy gpg keys from other machine using scp
GPG keys are a crucial part of secure communication. But how do we manage them effectively? Here’s a comparison of different GPG key management methods:
| Method | Description |
|---|---|
| GPG Keys | Secure encryption and decryption |
GPG Keys are a powerful tool for secure communication, and SCP provides a reliable protocol for copying them between machines. By understanding the concept of GPG keys and how SCP works, we can ensure that our digital communications remain safe and secure.
SCP in Practice
SCP is widely used in various industries, including finance, healthcare, and government. Its high security features make it an ideal choice for transferring sensitive data, including GPG keys.
For example, in the finance industry, SCP is used to transfer sensitive financial data between banks and financial institutions. The use of SCP ensures that the data is transmitted securely, reducing the risk of data breaches and cyber attacks.
In the healthcare industry, SCP is used to transfer patient data between hospitals and healthcare providers. The use of SCP ensures that the data is transmitted securely, reducing the risk of data breaches and ensuring that patients’ sensitive information remains confidential.
In the government sector, SCP is used to transfer sensitive data between government agencies and contractors. The use of SCP ensures that the data is transmitted securely, reducing the risk of data breaches and cyber attacks.
In each of these industries, SCP provides a secure and reliable way to transfer sensitive data, including GPG keys. By understanding how SCP works, we can ensure that our digital communications remain safe and secure.
Prerequisites for Copying GPG Keys with SCP
Before we dive into the details of copying GPG keys with SCP, let’s first set the stage with the necessary prerequisites. To get started, you’ll need to have a solid understanding of GPG and SSH keys, as well as the necessary software and tools to manage them.
Setting Up GPG and SSH Keys
GPG (GNU Privacy Guard) is a free and open-source implementation of the OpenPGP standard, which provides secure encryption and decryption services. On the other hand, SSH (Secure Shell) keys are used for secure remote access to servers and other machines. In order to copy GPG keys with SCP, you’ll need to have GPG installed on your system. SSH keys are also a requirement, as SCP relies on SSH for secure file transfers.
GPG and SSH keys serve different purposes, but they complement each other well in the context of secure communication. GPG is used for encrypting and decrypting data, while SSH keys provide secure authentication and authorization. Having both GPG and SSH keys set up on your system will allow you to take advantage of SCP’s features for secure file transfers.
Necessary Software and Tools
To copy GPG keys with SCP, you’ll need the following software and tools:
- GnuPG: This is the software that implements the OpenPGP standard and provides secure encryption and decryption services.
- OpenSSL: While not strictly necessary, OpenSSL is often used for key generation and management, as well as for creating certificates and other cryptographic materials.
These tools can be used for a variety of tasks, including generating and managing keys, encrypting and decrypting data, and creating secure certificates.
With GnuPG and SSH keys set up on your system, and the necessary software and tools at your disposal, you’re now ready to learn how to copy GPG keys with SCP. This will allow you to securely transfer files and data between machines, while maintaining the integrity and security of your encrypted data.
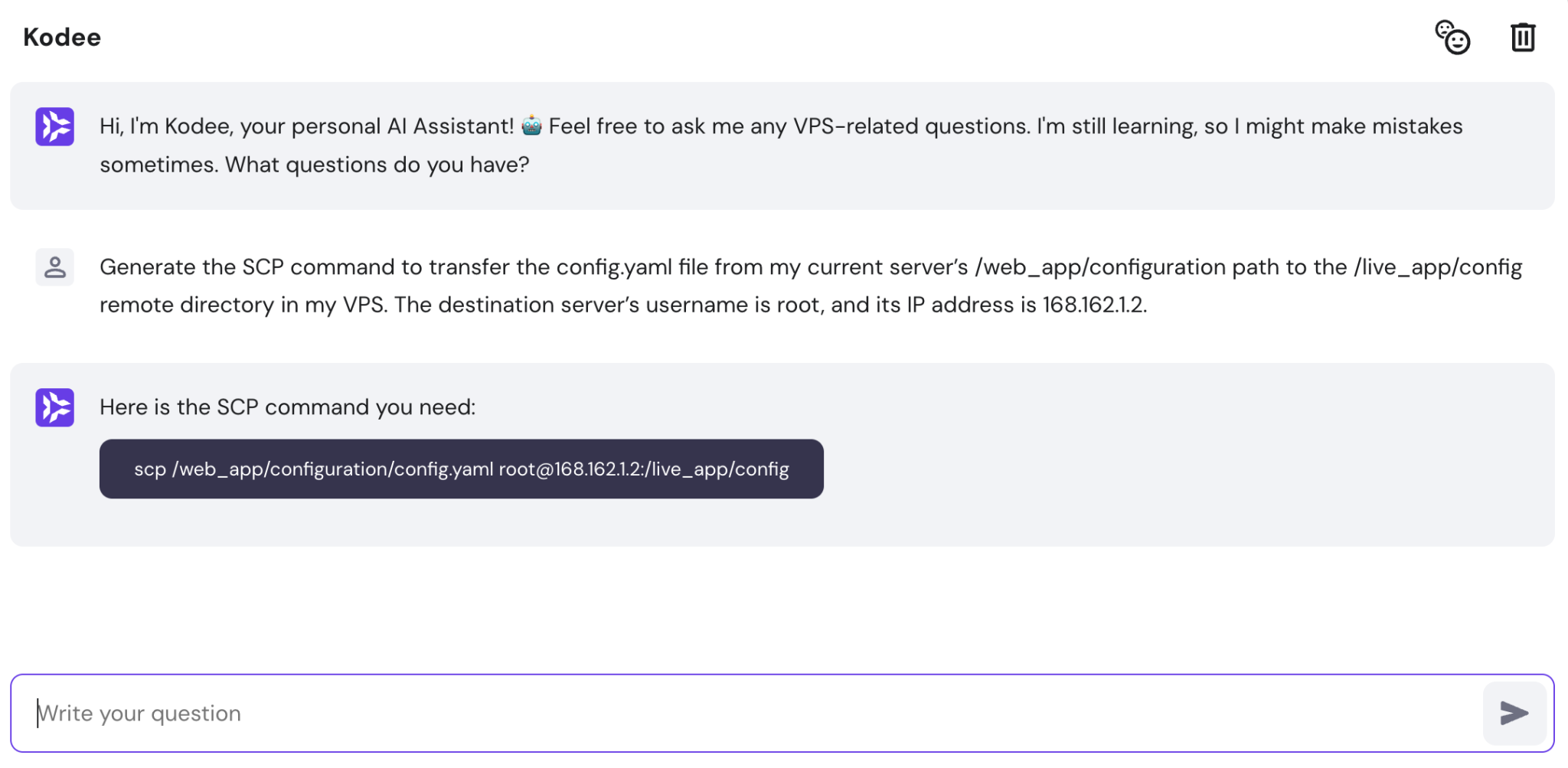
SCP’s line interface and syntax are based on the rsh (remote shell) command. The general syntax for copying a file using SCP is: `scp user@host:/path/to/file /path/to/save/file`. This command connects to the remote host, copies the specified file, and saves it to the specified local path. Note that SCP requires a secure shell (SSH) connection to be established before it can initiate the file transfer.
The SCP Command
The SCP command is used to copy files securely over a network. It uses the SSH protocol to establish a secure connection to the remote host, and can be used for both local and remote file transfers. The SCP command syntax is as follows:
`scp [options] source destination`
Some common SCP options include:
* `-r` for recursive copying
* `-p` for preserving file permissions
* `-P` for specifying a non-standard port
Examples of Copying GPG Keys with SCP
Here are a few examples of using SCP to copy GPG keys from one machine to another:
* To copy a GPG key from user `bob` on host `192.168.1.100`, use the following command: `scp bob@192.168.1.100:/path/to/key.gpg /path/to/saved/key.gpg`
* To copy all GPG keys from user `bob` on host `192.168.1.100`, use the following command: `scp -r bob@192.168.1.100:/path/to/key/ /path/to/saved/key`
SCP to copy a GPG key (scp user@host1:/path/to/key.gpg /path/to/saved/key.gpg)
Configuring SCP for Secure Key Exchange
Before copying GPG keys using SCP, you’ll need to configure SCP to use a secure connection. Here are the steps to follow:
1. Ensure that SSH is installed and configured on both the local and remote hosts.
2. Generate a key pair on the local host using the `ssh-keygen` command.
3. Add the local host’s public key to the remote host’s authorized_keys file.
4. Test the secure connection using the `ssh -v` command.
By following these steps and using the SCP command, you can securely copy GPG keys between machines. Remember to use the `-r` option for recursive copying, and to preserve file permissions with the `-p` option.
End of Discussion
![SCP Remote to Local [Practical Examples] SCP Remote to Local [Practical Examples]](https://learnubuntu.com/content/images/size/w1000/2023/09/scp-copying-folders-from-remote-to-local.png)
In conclusion, copying GPG keys from one machine to another using SCP is a crucial step in secure key management. By following the steps Artikeld in this guide and adhering to best practices for secure GPG key management, individuals can ensure the security and integrity of their digital communications. Remember, secure communication is key to preventing data breaches and ensuring the confidentiality of sensitive information.
Helpful Answers
Q: What is the SCP -line interface and syntax?
The SCP line interface and syntax vary depending on the operating system and SCP client being used. However, the general syntax for copying a file using SCP is: scp [source] [destination]
Q: How do I securely store and manage GPG keys on multiple machines?
Use a secure key server to store your GPG keys and ensure they are encrypted. Additionally, use a password manager to securely store the passwords required to access the keys. Finally, use a secure protocol, such as encrypted key storage, to transfer keys between machines.
Q: Can I use SCP to copy GPG keys between machines with different operating systems?
Yes, SCP can be used to copy GPG keys between machines with different operating systems, provided that the SCP client is compatible with both operating systems and the GPG keys are in a compatible format.
Q: How do I troubleshoot issues with SCP key exchange?
Verify that the SCP client and server are compatible, ensure the GPG keys are in a compatible format, and double-check the syntax of the SCP command being used.