How the Enigma Machine Was Cracked is an intriguing story that unravels in a captivating manner, drawing readers into a tale that combines complexity, strategic thinking, and determination. The Enigma machine, a German military innovation, was used to secure communication during World War II, making it a pressing issue for the Allied forces.
The Enigma machine’s keyboard layout and functionality are a crucial aspect of its operation, with the machine producing a complex encryption that has been the subject of extensive analysis and study. Despite its significance, deciphering the Enigma code was a daunting task, presenting numerous challenges for cryptographic analysts and highlighting the importance of persistence and innovative problem-solving.
Introduction
The Enigma machine played a pivotal role in World War II, serving as a critical tool for secure communication between German military units and command centers. Developed in the 1920s by German engineer Arthur Scherbius, the Enigma machine used a complex system of rotors, wiring, and substitution tables to encode messages, making them virtually unbreakable.
The Enigma Machine
The German military adopted the Enigma machine due to its perceived unbreakability, using it for high-level communication. This was especially crucial for the German military, which was eager to maintain secrecy in its operations and plans during the war. The machine’s primary function was to substitute alphabetic characters with other alphabetic characters, making it difficult for unauthorized parties to decipher the messages.
Encryption and Decryption Process
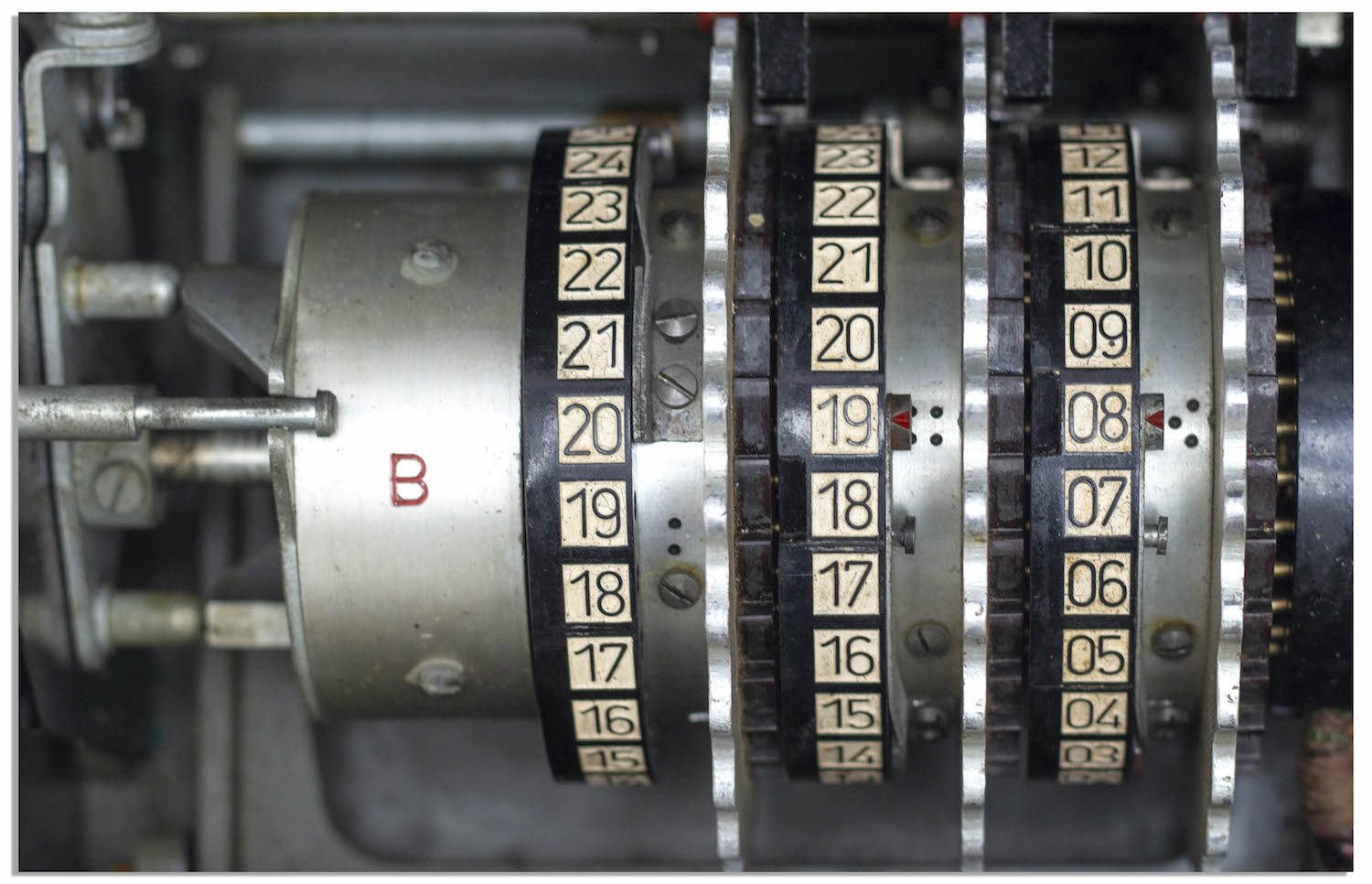
The Enigma machine employed a polyalphabetic substitution cipher, which involved the use of multiple rotors, a wiring system, and a keyboard to encrypt messages. The rotors were responsible for shifting the character positions, creating a unique substitution pattern for each character entered. Each rotor had a specific number of wiring connections, which added to the complexity of the encryption process. The result was an encoded message that seemed random to outsiders, requiring extensive knowledge of the machine’s internal workings and settings to accurately decrypt.
Operational Details
Every day, the German military would set up the machine, selecting specific rotors, wiring, and ring settings. The machine’s keyboard allowed for efficient input of characters, and the substitution tables ensured that each character was replaced with a new one, following a predetermined sequence. The encoded message would then be fed through a machine like an Enigma machine via radio transmission. This ensured that information was kept secret, even if intercepted by enemy forces.
Impact and Limitations
Despite being unbreakable to the general public, the Enigma machine was not foolproof. The machine’s internal workings and settings could be deduced through rigorous work and collaboration, eventually enabling the Allies to crack the code. German operators were not aware of this possibility, often using the Enigma machine for routine communications. While the Enigma machine served German military goals, limitations existed, including the potential for human error, maintenance issues, and the development of rival encryption methods.
Limitations of Human-Operated Machines
The Enigma machine relied heavily on human operators, who would manually set the rotors, wiring, and ring settings each day. Human error and variations in settings could lead to difficulties in deciphering messages. As German forces expanded their geographical reach, coordinating operations across distant locations became increasingly challenging. This led to instances of confusion and miscommunication due to machine settings being set incorrectly. Furthermore, as the Allies gathered crucial information about the machine’s operation, the German military’s reliance on the Enigma machine grew increasingly vulnerable.
Key Players and Their Contributions
Several key individuals played a crucial role in deciphering Enigma messages. Polish mathematicians Marian Rejewski, Jerzy Różycki, and Henryk Zygalski were among the first to crack the Enigma code through painstaking work and collaboration. Their efforts eventually reached the British intelligence agency, where codebreakers like Alan Turing used the provided information to develop a working version of the Bombe machine, a mechanical device specifically designed to automate the process of deciphering the Enigma code.
British Intelligence Agency and Codebreaking Efforts
The British codebreaking agency (also referred to as the Government Code and Cypher School, or GC & CS), located at Bletchley Park, spearheaded the effort to crack the Enigma code. With assistance from Polish cryptographers and mathematicians, they made use of cryptanalysis techniques and machine development. The British team’s work focused on using the Bombe machine, alongside human operators, to rapidly process and crack intercepted Enigma communications. Their efforts significantly altered the tide of World War II, ultimately providing valuable information to the Allied forces.
Structure and Operation
The Enigma machine was a complex cryptographic device that played a crucial role in securing German communications during World War II. Its unique structure and operation made it one of the most secure encryption systems of its time. The machine consisted of a keyboard, a plugboard, and a rotor system that combined to scrambles the text entered into the machine.
At its core, the Enigma machine was an electro-mechanical cipher machine that used a series of rotors, wiring, and substitution tables to encrypt messages. The machine’s keyboard layout featured 26 keys, one for each letter of the alphabet, as well as a few additional keys for common punctuation marks and symbols. The plugboard, located on the front of the machine, was a small panel with a series of sockets that allowed the operator to connect the letters in a specific order. This created a unique substitution table that changed with each keystroke.
Keyboard Layout and Functionality
The Enigma machine’s keyboard layout was designed to facilitate easy typing and efficient encryption. The keys were arranged in a compact, QWERTY-style layout, with each key corresponding to a specific letter or symbol. The operator would type a message into the machine, and the keyboard would transmit the electrical signals to the rotors, which would scramble the message accordingly. The plugboard also played a crucial role in the encryption process, as it introduced additional substitutions to the message.
The Enigma machine’s functionality was centered around the rotor system, which consisted of three to five rotors, each with a different wiring pattern. The rotors were stacked on top of each other, with the first rotor on the left. As the operator typed a message, the electrical signals would flow through the rotors, introducing additional substitutions and rearrangements to the message. The plugboard would also modify the signal flow by connecting certain letters to specific letters on the next rotor.
Comparison to Other Cryptographic Systems
The Enigma machine’s encryption methods were unparalleled at the time, making it one of the most secure communication systems in the world. Compared to other cryptographic systems of the era, the Enigma machine stood out for its complex rotor system and plugboard, which introduced a near-infinite number of possible encryption permutations. Other systems, such as the Hagelin cipher machine, relied on simpler substitution tables and mechanical wheels, making them more predictable and vulnerable to cryptanalysis.
The Enigma machine’s encryption methods were also more flexible and adaptable than other systems, allowing operators to easily change the settings and configurations to create new encryption patterns. This made the Enigma machine an attractive option for secure communication, particularly for military and diplomatic purposes.
The Enigma machine’s encryption methods were further enhanced by the use of encryption tables and key exchange protocols. The German military used a complex system of encryption tables and key exchange protocols to ensure that the Enigma machine’s settings were kept secret, even from other German agents.
In summary, the Enigma machine’s structure and operation were designed to create a highly secure encryption system that would protect German communications from interception and deciphering. Its unique keyboard layout, plugboard, and rotor system made it one of the most complex and secure cryptographic devices of its time.
Polish Contributions and Early Breakthroughs
Marian Rejewski and his team in Poland made significant contributions to the decryption of the Enigma machine, which laid the foundation for the subsequent breaking of the code by the British and the Americans. The Polish team’s work was instrumental in deciphering the Enigma code, and their efforts paved the way for the Allied forces to gain valuable intelligence during World War II.
The Polish team’s insights into the Enigma machine were gained through the use of stolen machines, which they analyzed and experimented with to understand its internal workings. They developed techniques for deducing the settings used by the machine, including the use of wheel patterns and plugboard connections.
Stolen Enigma Machines and Analytical Techniques
The Polish team obtained several Enigma machines through various means, including theft and purchase. They then thoroughly cleaned, repaired, and analyzed these machines to understand their internal mechanics. Their analytical techniques allowed them to determine the machine’s settings, including the wheel patterns and plugboard connections, which were critical for deciphering the encrypted messages.
-
The Polish team developed a system to identify the Enigma machine’s rotor order, which was essential for understanding the machine’s internal workings.
They also created methods for determining the wiring of the machine’s plugboards, which further aided in deciphering the encrypted messages.
By studying the machine’s internal workings, the Polish team was able to create charts and tables to help them determine the machine’s settings. -
The Polish team’s work also involved the development of techniques for deducing the daily settings used by the German operators, which included the use of wheel patterns and plugboard connections.
They also created a system to identify the machine’s “key” for the day, which enabled them to decipher the encrypted messages.
The Polish team’s techniques for deducing the machine’s settings were innovative and effective, and they paved the way for the Allied forces to gain valuable intelligence during World War II.
“The Enigma machine was like a puzzle, and we had to find the missing pieces to solve it.”
— Marian Rejewski
The Polish team’s work laid the foundation for the subsequent breaking of the Enigma code by the British and the Americans. Their analytical techniques and innovative methods for deciphering the Encrypted messages were instrumental in the Allied forces’ ultimate victory in World War II.
British Codebreaking Efforts – Breaking the Malleable Machine
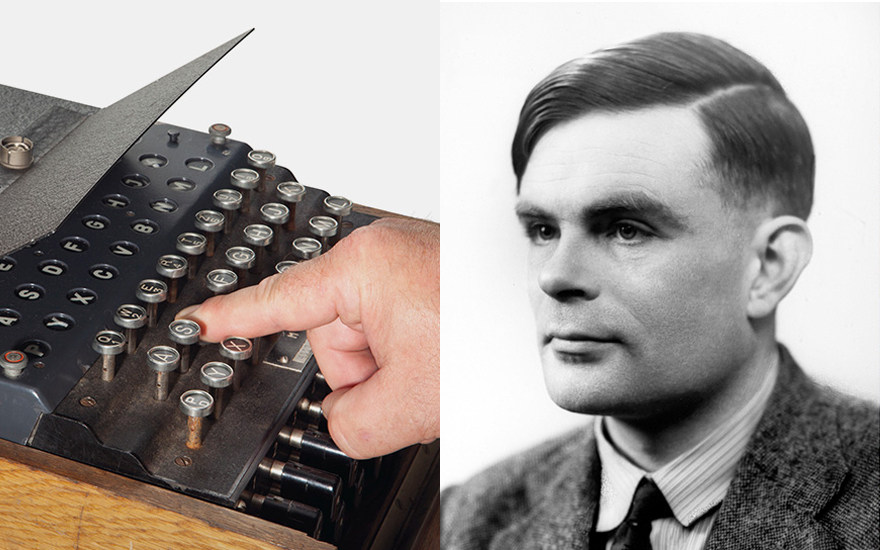
Alan Turing and his team at the Government Code and Cypher School (GC&CS) at Bletchley Park made significant advancements in cracking the Enigma code, which had been puzzling the British for several years. Their work marked a major breakthrough in the war effort, allowing the Allies to gain valuable intelligence on German military operations.
After the Polish cryptographers had identified the Enigma machine’s operating principles and made initial headway in cracking its code, the British took over the task with renewed vigor. Alan Turing, in particular, contributed significantly to the efforts, as did his colleague Gordon Welchman. They worked tirelessly to develop innovative techniques to process and analyze the vast amounts of encrypted messages intercepted by the British.
Machine Improvements Inspired by Turing’s Work
Turing’s work led to a better understanding of the Enigma machine’s inner workings and identified areas where its security could be compromised. This newfound knowledge directly influenced the design of the Bombe, an electromechanical machine specifically created to decipher Enigma traffic. The Bombe was a crucial addition to the British codebreaking efforts, allowing the team to process messages at an unprecedented rate.
The Bombe was inspired by the Polish machine known as the ‘Rejewski’s Bomba’, and it greatly enhanced the efficiency of codebreaking operations at Bletchley Park. By using a series of electromechanical drums and levers, the Bombe simulated the Enigma machine’s encryption process, allowing the team to deduce the settings used by the Germans and subsequently crack the codes.
The improvements made to the Enigma machine itself were also informed by Turing’s research. His work highlighted the machine’s inherent malleability and the need for frequent changes to its settings to maintain its security. This knowledge was used to modify the Enigma machine’s design, making it slightly more secure but also more prone to errors that the British could exploit.
The Role of the Bombe in Codebreaking
The Bombe played a vital role in the British codebreaking efforts, processing and analyzing millions of possible settings to uncover the correct ones used by the Germans. This machine allowed the codebreakers to tackle the Enigma traffic on a much larger scale than ever before, providing the Allies with a steady flow of high-quality intelligence.
-
The Bombe’s efficiency enabled the British to rapidly process Enigma messages, keeping pace with the Germans’ rapid changes to the machine’s settings. This allowed the codebreakers to continuously update their knowledge of the Enigma machine’s inner workings.
-
The Bombe also facilitated the development of more sophisticated analytical techniques, such as the “cribbing” method, which involved comparing fragments of known text to corresponding fragments of encrypted messages. This led to significant breakthroughs in codebreaking.
The Bombe’s effectiveness was instrumental in maintaining the British codebreaking advantage throughout the war. It provided a solid foundation for future advancements in codebreaking, ultimately contributing to the Allied victory.
The Bombe Machine and Codebreaking Efficiency
In 1939, Alan Turing and Gordon Welchman, two British mathematicians, designed and developed the Bombe machine at the Government Code and Cypher School (GC&CS) at Bletchley Park. The Bombe machine was a mechanical device that significantly improved the efficiency of codebreaking by automating and speeding up the process of searching for the correct settings for the Enigma machine.
The Bombe machine was a large and complex device, consisting of a series of drums, electrical connections, and switches. It was powered by a series of motors and had a series of input and output mechanisms. The machine used a similar concept to the Enigma machine’s rotor system, with multiple drums and settings that could be adjusted to search for the correct combination of wheel order, ring setting, and plugboard connections.
The Mechanics of the Bombe Machine
The Bombe machine used a combination of mechanical and electrical principles to speed up the codebreaking process. It consisted of five drums, each representing one of the rotors in the Enigma machine. The drums were connected through a series of electrical contacts, which were used to search for the correct combination of rotor positions, rotor wiring, plugboard connections, and rotor ring settings.
How the Bombe Machine Worked
The Bombe machine worked by simulating the process of encrypting and decrypting a message with the Enigma machine. The operator would enter a sequence of letters and numbers into the machine, which would then search for the correct settings that would result in the plaintext message being obtained. The machine would iterate through all possible settings, using a combination of mechanical and electrical contacts to simulate the Enigma machine’s encryption process.
Key Features of the Bombe Machine, How the enigma machine was cracked
Automated Search Mechanism
The Bombe machine’s automated search mechanism was its most significant innovation. It allowed the machine to search through all possible settings in a fraction of the time it would take a human operator to do so. This made it possible to crack the Enigma code in a matter of hours, rather than weeks or months.
Reduced Human Error
The Bombe machine also reduced human error, which was a significant problem in codebreaking. The machine’s mechanical and electrical contacts ensured that the settings were entered correctly, reducing the likelihood of human error.
Increased Codebreaking Capacity
The Bombe machine increased codebreaking capacity by allowing multiple operators to work on different aspects of the codebreaking process simultaneously. This made it possible to crack multiple Enigma messages in a short period.
List of Key Innovations
- The Bombe machine’s automated search mechanism significantly improved codebreaking efficiency.
- The machine’s reduced human error rate ensured that settings were entered correctly, reducing the likelihood of error.
- The Bombe machine increased codebreaking capacity, allowing multiple operators to work on different aspects of the codebreaking process simultaneously.
- The machine’s mechanical and electrical contacts simulated the Enigma machine’s encryption process, making it possible to crack the Enigma code.
- The Bombe machine played a crucial role in the Allied victory in World War II.
“The Bombe was a machine that could do the job of 20 or 30 men, and if it had been available earlier, I believe that would have changed the whole course of the war.”
– Alan Turing
Human Computing and Statistical Methods
Human computing and statistical methods played a vital role in the codebreaking process of the Enigma machine. Mathematicians and statisticians used complex algorithms and statistical techniques to decipher the cryptic messages, complementing the efforts of the Bombe machine and cryptanalysts. Their contributions were instrumental in cracking the code, which significantly impacted the outcome of World War II.
Human computers and statisticians were responsible for analyzing and processing the vast amount of data generated by the Bombe machine. They employed statistical methods to identify patterns and trends in the encrypted messages, which helped narrow down the possibilities for the rotor settings and wheel orders. The team of human computers and statisticians worked tirelessly to process the data, often under intense pressure and with limited resources.
Statistical Methods in Codebreaking
One significant statistical method used to crack the Enigma code was the “cribbing” technique. Cribbing involved identifying a short sequence of plaintext characters, known as a crib, that appeared in the encrypted message. By analyzing the frequency of letters and letter combinations, the cryptanalysts could deduce the possible location of the crib within the encrypted message. This technique relied heavily on the statistical analysis of letter frequencies, a concept developed by William Friedman, an American cryptanalyst, who studied the frequency distribution of letters in the English language. According to
the Friedman frequency distribution
, the most common letter in the English language is ‘E’, accounting for approximately 12.7% of all letters. By applying this distribution to the encrypted message, the cryptanalysts could estimate the probability of each letter being in a particular position, thus increasing the chances of identifying the crib.
The “cribbing” technique was used in conjunction with other statistical methods, such as the
chi-squared test
, a statistical test used to determine whether the observed frequencies of letters in an encrypted message differed significantly from the expected frequencies based on the English language. By analyzing these frequencies, the cryptanalysts could identify patterns and trends that hinted at the presence of a crib.
In addition to these statistical methods, the human computers and statisticians played a crucial role in processing the data generated by the Bombe machine. They used a combination of mental math and statistical software to identify the possible rotor settings and wheel orders, which significantly narrowed down the possibilities for the Enigma machine’s settings.
Statistical methods such as these, in combination with human computing and the Bombe machine, ultimately contributed to the successful cracking of the Enigma code, which had a profound impact on the outcome of World War II.
Key Statistical Techniques
-
The Chi-Squared Test
The chi-squared test was a statistical test used to determine whether the observed frequencies of letters in an encrypted message differed significantly from the expected frequencies based on the English language. By analyzing these frequencies, the cryptanalysts could identify patterns and trends that hinted at the presence of a crib.
-
Cribbing
The “cribbing” technique involved identifying a short sequence of plaintext characters, known as a crib, that appeared in the encrypted message. By analyzing the frequency of letters and letter combinations, the cryptanalysts could deduce the possible location of the crib within the encrypted message.
-
Letter Frequencies
The cryptanalysts studied the frequency distribution of letters in the English language, which was developed by William Friedman. This distribution was used to analyze the probability of each letter being in a particular position in the encrypted message.
The Role of Intelligence and Human Error
The cracking of the Enigma code was a complex process that involved a multitude of factors, including intelligence networks and human error. While the mathematical and logistical breakthroughs achieved by cryptanalysts and engineers are well-documented, it is essential to acknowledge the significant contributions made by intelligence networks and human error.
Intelligence Networks
The British intelligence network played a crucial role in the cracking of the Enigma code. Through their network of agents and spies, they obtained crucial information about the Enigma machine and its operating procedures. This information, combined with the knowledge gained from the Polish cryptanalysts, formed the basis of the British codebreaking efforts. The British intelligence network was instrumental in gathering the necessary data to understand the machine’s mechanics and the encryption procedures used by the German military. This information allowed the British to build on the work of the Polish cryptanalysts and make significant breakthroughs in cracking the Enigma code.
- The most significant contribution of the British intelligence network was the capture of the Enigma machine from a German U-boat in 1941. This provided the British with a working model of the machine, which they used to develop the Bombe machine.
- The intelligence network also provided information about the daily keys and settings used by the German military to operate the Enigma machine. This information allowed the British to understand how the machine was being used in real-time, providing valuable insights into the enemy’s communication patterns.
Human Error
Human error played a significant role in the cracking of the Enigma code. The Enigma machine relied on the security of a series of settings and keys being changed daily. However, human operators often failed to follow procedures correctly, which resulted in predictable patterns emerging in the encrypted messages. The British codebreakers were able to exploit these patterns to make significant breakthroughs in cracking the Enigma code.
- The German military had a tendency to use the same keys for multiple messages, which created a predictable pattern in the encrypted messages. This allowed the British codebreakers to identify the keys used in a particular message.
- The human error also included the fact that the German military often transmitted redundant and redundant key messages, which were easily intercepted by the British. The British codebreakers were able to use these intercepted messages to develop their own keys for decrypting the Enigma machine.
Impact of Intelligence Networks and Human Error
The combined impact of intelligence networks and human error was significant. It allowed the British codebreakers to develop a deep understanding of the Enigma machine and its operating procedures. This understanding enabled them to make significant breakthroughs in cracking the Enigma code, providing invaluable intelligence to the Allies during World War II.
Conclusion
The cracking of the Enigma code was a complex process that involved a multitude of factors, including intelligence networks and human error. While the mathematical and logistical breakthroughs achieved by cryptanalysts and engineers are well-documented, it is essential to acknowledge the significant contributions made by intelligence networks and human error. The combined impact of these factors played a crucial role in the success of the British codebreaking efforts and ultimately contributed to the defeat of the German military in World War II.
Key Takeaways
The key takeaways from the intelligence networks and human error are:
- The British intelligence network played a crucial role in the cracking of the Enigma code by gathering information about the Enigma machine and its operating procedures.
- Human error, such as the use of predictable patterns and redundant keys, allowed the British codebreakers to make significant breakthroughs in cracking the Enigma code.
- The combined impact of intelligence networks and human error was significant, providing invaluable intelligence to the Allies during World War II.
“The machine was not just a piece of hardware, but a system that relied on human operators to ensure its security. The human error played a significant role in the cracking of the Enigma code.”
Legacy of Enigma Codebreaking: How The Enigma Machine Was Cracked

The Enigma codebreaking efforts, which took place from the 1920s to the 1940s, had a profound impact on cryptographic history. The efforts of Polish cryptanalysts and British codebreakers, particularly Alan Turing and his team at Bletchley Park, demonstrated the importance of breaking complex encryption systems. This legacy paved the way for modern cryptography, influencing the development of coding theory and the creation of secure communication systems.
The Impact on Cryptographic History
The Enigma codebreaking efforts marked a significant turning point in the history of cryptography. For the first time, it demonstrated that complex encryption systems could be broken with the right combination of mathematical and computational techniques. This accomplishment had far-reaching consequences, leading to a re-evaluation of cryptographic practices and the development of more secure encryption methods.
- The Enigma codebreaking efforts showed that encryption systems were not foolproof, leading to a shift towards more secure and flexible coding methods.
- The development of the Bombe machine, a mechanical computer designed to assist in codebreaking, laid the foundation for the creation of modern computers.
- The work of Alan Turing and his team at Bletchley Park provided valuable insights into the importance of human computing and statistical methods in codebreaking, highlighting the need for a multidisciplinary approach to cryptography.
Lessons Learned from the Enigma Codebreaking Project
The Enigma codebreaking project taught several valuable lessons that remain relevant to modern cryptography:
- The importance of collaboration and multidisciplinary approaches in codebreaking and cryptography.
- The need for a deep understanding of the underlying mathematics and statistical principles underlying encryption systems.
- The value of human computing and statistical methods in codebreaking, particularly in situations where computational resources are limited.
- The importance of a flexible and adaptive approach to cryptography, as encryption systems and techniques continue to evolve.
The Relevance to Modern Cryptography
The legacy of Enigma codebreaking continues to shape modern cryptography, influencing the development of secure communication systems and coding theory. The Enigma codebreaking efforts demonstrated the importance of breaking complex encryption systems, highlighting the need for a multidisciplinary approach to cryptography. This knowledge has been applied in various areas, including:
“The machine has no mind, but it can be used to create a model of the human mind,” – Alan Turing
- Computer security: understanding the importance of human computing and statistical methods in codebreaking has led to the development of more secure encryption methods and protocols.
- Coding theory: the Enigma codebreaking efforts led to a deeper understanding of the underlying mathematics and statistical principles underlying encryption systems, informing the development of modern coding theory.
- Artificial intelligence: the work of Alan Turing and his team at Bletchley Park laid the foundation for the development of artificial intelligence and machine learning techniques, which are now used in various areas, including cryptography and computer security.
- Cybersecurity: the Enigma codebreaking legacy continues to inform the development of more secure and flexible coding methods, highlighting the need for a multidisciplinary approach to cryptography.
Closing Summary
The Enigma codebreaking efforts, a significant chapter in cryptographic history, demonstrate the power of collaboration, intelligence, and human ingenuity in overcoming seemingly insurmountable obstacles. The story of how the Enigma machine was cracked serves as a testament to the importance of strategic thinking, creative problem-solving, and the unwavering dedication of individuals and teams in pursuit of a vital goal.
Helpful Answers
Who was the first person to crack the Enigma code?
Marian Rejewski, a Polish cryptographer, was the first person to crack the Enigma code, along with his colleagues Jerzy Różycki and Henryk Zygalski.
How did British cryptographers crack the Enigma code?
British cryptographers, led by Alan Turing and his team, made significant advancements in cracking the Enigma code, using a combination of mathematical and computational methods, including the development of the Bombe machine.
What was the significance of the Enigma codebreaking efforts?
The Enigma codebreaking efforts were significant because they demonstrated the importance of cryptography in wartime communication and highlighted the importance of collaboration and innovative problem-solving in overcoming complex challenges.
How did the Enigma machine work?
The Enigma machine used a complex series of rotors, wiring, and substitution tables to encrypt messages, producing a highly secure encryption that was difficult to decipher without the correct key.