As how to decrypt virtual machine VMware takes center stage, this opening passage beckons readers into a world crafted with good knowledge, ensuring a reading experience that is both absorbing and distinctly original. The concept of encryption in VMware virtual machines plays a vital role in securing sensitive data.
This guide provides an in-depth exploration of the encryption process in VMware virtual machines, from understanding the encryption features to designing a secure encryption strategy. The content is carefully crafted to provide a clear and concise understanding of the topic.
Understanding VMware Virtual Machine Encryption
Encryption in virtual machines, including those virtualized by VMware, is a crucial aspect of data security. Virtual machines, which are software-based emulation of physical hardware, often store sensitive data that requires protection from unauthorized access. VMware, as a leading provider of virtualization solutions, has implemented robust encryption features to safeguard virtual machine data.
Encryption Concept in VMware Virtual Machines
Encryption is the process of converting plaintext data into unreadable ciphertext, making it difficult for unauthorized parties to access or decipher the information. In the context of VMware virtual machines, encryption is typically applied to the virtual hard disk (VMDK) files, which store the operating system, applications, and data. This ensures that even if a virtual machine is compromised or stolen, the stored data remains protected.
Encryption Features in VMware
VMware offers several encryption features to secure virtual machine data:
- Virtual Machine Encryption: This feature encrypts the contents of a virtual machine’s virtual hard disk (VMDK) files, making it unreadable without the decryption key.
- Password-protected encryption: Users can set a password to encrypt and decrypt virtual machine files, adding an additional layer of security.
- Certificate-based encryption: VMware supports certificate-based encryption using public-key infrastructure (PKI) certificates, which provides an additional layer of security.
Importance of Encryption in Securing Virtual Machine Data
Encrypting virtual machine data is crucial for protecting sensitive information from unauthorized access. In the event of a data breach or virtual machine compromise, encryption prevents attackers from accessing or exploiting the stored data. Additionally, encryption helps organizations comply with regulatory requirements and industry standards for data security.
Types of Encryption in VMware Virtual Machines
VMware virtual machines employ various encryption methods to secure data, ensuring confidentiality, integrity, and authenticity. Encryption plays a crucial role in safeguarding sensitive information, especially in virtualized environments where data is shared extensively. Understanding the types of encryption used in VMware virtual machines is essential for implementing effective security measures. This section highlights the different encryption methods used in VMware and their key characteristics.
Symmetric Encryption
Symmetric encryption involves using the same secret key for both encryption and decryption, making it efficient for bulk data transfer. VMware virtual machines support symmetric encryption algorithms such as AES (Advanced Encryption Standard) and Blowfish. Symmetric encryption is suitable for securing large datasets.
- AES is a widely used block cipher, providing high security and speed.
- Blowfish is an older symmetric encryption algorithm, still used in some VMware environments due to its efficiency and ease of implementation.
Asymmetric Encryption
Asymmetric encryption, also known as public-key encryption, employs a pair of keys – a public key for encryption and a private key for decryption. This method ensures secure key exchange and authentication. VMware virtual machines use asymmetric encryption algorithms such as RSA (Rivest-Shamir-Adleman) and ECDSA (Elliptic Curve Digital Signature Algorithm). Asymmetric encryption is ideal for key exchange, digital signatures, and secure communication.
- RSA is a widely used public-key encryption algorithm, offering high security and flexibility.
- ECDSA is an elliptic curve-based digital signature algorithm, providing faster key generation and smaller key sizes than RSA.
Public and Private Keys
Asymmetric encryption relies on the concept of public and private keys. Public keys are used for encryption, while private keys are used for decryption. The public key is publicly available, while the private key is securely stored by the recipient. VMware virtual machines use public and private keys to establish secure connections and verify identities.
- Public keys are used to encrypt messages or data intended for the owner of the corresponding private key.
- Private keys are used to decrypt messages or data encrypted with the corresponding public key.
Advantages and Disadvantages
Encryption types have their advantages and disadvantages, which are essential to consider when implementing security measures in VMware virtual machines.
| Type of Encryption | Advantages | Disadvantages |
|---|---|---|
| Symmetric | Efficient for bulk data transfer, fast encryption and decryption | Difficult key management, potential for key sharing |
| Asymmetric | Secure key exchange, authentication, and digital signatures | Slower encryption and decryption, key management complexity |
Blockchain is a decentralized, distributed digital ledger technology that enables secure, transparent, and tamper-proof data management. VMware virtual machines can utilize blockchain to enhance data security, integrity, and authenticity. By leveraging blockchain’s unique features, such as immutability and decentralization, VMware can provide an additional layer of security for virtual machine data.
“Immutable data is essential for maintaining the integrity and authenticity of virtual machine data.”
Encrypting Virtual Machine Disks in VMware
Encrypting virtual machine disks in VMware is a crucial step in safeguarding sensitive data stored within virtual machines. This process involves using advanced encryption techniques to protect data from unauthorized access. VMware provides a robust feature for encrypting virtual machine disks, ensuring that sensitive information remains secure.
To encrypt a virtual machine disk in VMware, administrators can follow these steps:
1. Launch the VMware vCenter Server, and navigate to the virtual machine you wish to encrypt.
2. Right-click on the virtual machine and select ‘Edit Settings’.
3. In the Virtual Machine Properties window, click on the ‘Options’ tab.
4. Select ‘Advanced’ from the drop-down menu.
5. Click on the ‘Security’ tab.
6. Enable the ‘Encrypt Configuration File and Virtual Disks’ option.
7. Choose the encryption algorithm and password to use.
8. Click on ‘Save’ to apply the changes.
Differences Between Disk Encryption and File-Level Encryption
Disk encryption and file-level encryption are two distinct methods used to protect data. While both methods aim to safeguard sensitive information, they differ in their approach and scope.
Disk encryption involves encrypting the entire virtual disk, which can be either a virtual hard disk (VHD) or a virtual machine disk (VMDK). This method encrypts all data stored on the disk, including operating systems, applications, and files.
File-level encryption, on the other hand, encrypts individual files or directories within a virtual machine. This method is more granular and flexible, allowing administrators to selectively encrypt sensitive files while leaving other data unprotected.
Both disk encryption and file-level encryption have their own strengths and weaknesses. Disk encryption provides a higher level of security, as it protects all data stored on the virtual disk. However, this method can be more resource-intensive and may require more administrative effort.
File-level encryption, while more flexible and granular, can be more vulnerable to data breaches, as sensitive files may be exposed if not properly protected.
Types of Disk Encryption in VMware, How to decrypt virtual machine vmware
VMware supports several types of disk encryption, including:
*
Full Disk Encryption:
This method encrypts the entire virtual disk, including the operating system and all applications.
*
Selective Disk Encryption:
This method allows administrators to selectively encrypt specific virtual disks or volumes while leaving others unprotected.
*
File-Level Encryption:
This method encrypts individual files or directories within a virtual machine.
Each type of disk encryption has its own benefits and drawbacks, and administrators must carefully evaluate their needs and requirements when selecting an encryption method.
Using Encryption Keys in VMware Virtual Machines
Encryption keys play a vital role in decrypting virtual machine data, making them a critical component of VMware virtual machine encryption. In this section, we will delve into the role of encryption keys, explore how to manage and secure them, and discuss the importance of key rotation and revocation.
Role of Encryption Keys in VMware Virtual Machines
Encryption keys are used to unlock encrypted data stored within a virtual machine. In VMware, encryption keys are used to decrypt virtual machine disks, allowing users to access and read the data stored within. There are two types of encryption keys used in VMware: primary and secondary keys. The primary key is used to encrypt the virtual machine data, while the secondary key is used to decrypt the data.
Managing and Securing Encryption Keys
Managing and securing encryption keys is crucial to preventing unauthorized access to encrypted data. VMware provides several features to help manage and secure encryption keys, including:
-
Key Management Service (KMS)
allows administrators to centrally manage and store encryption keys, making it easier to rotate and revoke keys as needed.
- Encryption key rotation is the process of replacing old encryption keys with new ones to maintain security and prevent key compromise.
- Encryption key revocation is the process of deleting or invalidating encryption keys that have been compromised or are no longer needed.
- Admins can also implement
Access Control
to limit access to encryption keys based on user roles and permissions.
Importance of Key Rotation and Revocation
Key rotation and revocation are essential components of encryption key management in VMware virtual machines. Regular key rotation helps prevent key compromise and ensures that encrypted data remains secure. Revoking keys that have been compromised or are no longer needed helps prevent unauthorized access to encrypted data.
Key rotation is typically performed
every 30-60 days
to ensure that encryption keys remain secure. Revoking keys that have been compromised or are no longer needed is also crucial to prevent unauthorized access to encrypted data.
Best Practices for Key Management
To ensure the security and integrity of encryption keys, administrators should follow best practices for key management, including:
- Use a centralized key management service to centrally manage and store encryption keys.
- Implement regular key rotation to prevent key compromise.
- Revoked keys that have been compromised or are no longer needed.
- Limit access to encryption keys based on user roles and permissions.
- Use secure protocols for key exchange and storage.
By following these best practices and using VMware’s key management features, administrators can ensure the security and integrity of encryption keys and maintain the confidentiality of encrypted data.
Troubleshooting Encryption Issues in VMware Virtual Machines
Troubleshooting encryption issues in VMware virtual machines can be complex and time-consuming, but following a systematic approach can help resolve these issues efficiently. Encryption-related problems in VMware can occur due to various reasons such as incorrect key management, corrupted encryption keys, or incompatible encryption algorithms.
Common Encryption-Related Problems Encountered in VMware
Some common encryption-related problems encountered in VMware virtual machines include:
- Invalid or corrupted encryption keys: Encryption keys can become corrupted or invalid due to various reasons such as power outages, system crashes, or incorrect key management.
- Encryption algorithms incompatibility: Incompatibility between encryption algorithms used in VMware and the operating system can cause encryption-related issues.
- Encryption key sizes mismatch: Mismatch in encryption key sizes between VMware and the operating system can cause encryption-related issues.
- Certificate issues: Issues with certificates used for encryption, such as expired or revoked certificates, can cause encryption-related issues.
Step-by-Step Guide to Troubleshooting Encryption Issues
To troubleshoot encryption issues in VMware virtual machines, follow these steps:
- Check the encryption key status: Verify the status of the encryption key, including its validity, size, and algorithm used.
- Check the encryption algorithm used: Verify the encryption algorithm used in VMware and ensure it is compatible with the operating system.
- Check the certificate status: Verify the status of the certificate used for encryption, including its expiration date, revocation status, and issuer details.
- Recreate the encryption key: Recreate the encryption key using a compatible algorithm and key size.
- Resync the encryption key: Sync the encryption key with the operating system to ensure it is correctly configured.
Resetting or Recovering Encrypted Virtual Machine Data
In some cases, it may be necessary to reset or recover encrypted virtual machine data. This can be done using the following steps:
- Power off the virtual machine: Power off the virtual machine to prevent any data corruption or loss.
- Unmount the virtual disk: Unmount the virtual disk to ensure it is not accessed by any other system or application.
- Remove the encryption key: Remove the encryption key from the virtual machine to reset the encryption.
- Recreate the encryption key: Recreate the encryption key using a compatible algorithm and key size.
- Sync the encryption key: Sync the encryption key with the operating system to ensure it is correctly configured.
When troubleshooting encryption issues, it’s essential to ensure that the encryption key is correctly configured and synchronized with the operating system.
Designing a Secure Encryption Strategy for VMware Virtual Machines
A secure encryption strategy for VMware virtual machines is essential to protect sensitive data from unauthorized access. This involves designing a robust encryption architecture that balances security, performance, and manageability. In this section, we will discuss the best practices for designing a secure encryption strategy, identify the key components of a secure encryption architecture, and compare and contrast different encryption methods and their suitability for various use cases.
Best Practices for Designing a Secure Encryption Strategy
When designing a secure encryption strategy for VMware virtual machines, consider the following best practices:
- Use end-to-end encryption to protect data in transit and at rest. This involves encrypting data as it is transmitted between the virtual machine and the storage, and encrypting the storage itself.
- Employ a key management system to securely store, rotate, and manage encryption keys.
- Use a secure cryptographic protocol to encrypt data, such as AES or SSL/TLS.
- Maintain a record of encryption keys and decrypting processes to facilitate troubleshooting and auditing.
- Continuously monitor and analyze encryption logs to detect potential security threats.
- Ensure that all virtual machines are running a supported and patched version of the operating system.
- Implement network segmentation to limit the attack surface and prevent lateral movement in the event of a breach.
Key Components of a Secure Encryption Architecture
A secure encryption architecture for VMware virtual machines typically includes the following key components:
- Encryption keys: Securely stored and managed encryption keys are essential for decrypting encrypted data.
- Cryptographic protocols: Secure cryptographic protocols, such as AES or SSL/TLS, provide a secure encryption method for data in transit and at rest.
- Key management system: A key management system securely stores, rotates, and manages encryption keys, as well as logs all key-related activities.
- Network segmentation: Implementing network segmentation limits the attack surface and prevents lateral movement in the event of a breach.
- Log monitoring and analysis: Continuous monitoring and analysis of encryption logs facilitates the detection of potential security threats.
Comparison of Different Encryption Methods
Different encryption methods have varying levels of effectiveness for various use cases. The following comparison highlights the key differences between popular encryption methods:
| Encryption Method | Key Features | Suitability for Various Use Cases |
|---|---|---|
| AES (Advanced Encryption Standard) | High-speed encryption, suitable for large datasets | Cloud storage, data backup, and virtual machine encryption |
| SSL/TLS (Secure Sockets Layer/Transport Layer Security) | End-to-end encryption, secure data transmission | Web-based applications, secure data transfer |
| PGP (Pretty Good Privacy) | End-to-end encryption, secure data transmission |
Remember that a robust encryption strategy is only as strong as its weakest link, and that encryption methods should be chosen based on their suitability for specific use cases.
Organizing and Managing Encryption-Related Data in VMware
Organizing and managing encryption-related data in VMware is crucial to maintaining data security and ensuring compliance with regulatory requirements. Proper data categorization and organization enable efficient data retrieval, facilitate incident response, and simplify compliance auditing.
Data Categorization and Organization
Data categorization and organization are essential for effective encryption management. VMware provides features to categorize and organize encryption-related data, making it easier to manage encrypted virtual machines, VM disks, and encryption keys.
- VMware’s built-in categorization features: VMware offers features such as tags and categories that allow administrators to classify and organize virtual machines, VM disks, and encryption keys based on specific criteria. This ensures that encryption-related data is easily searchable and accessible.
- Custom data categorization: Administrators can also create custom categories and tags to suit their specific organizational needs. This enables more granular control over data organization and improves data searchability.
Data Access Control and Auditing
Data access control and auditing are critical components of encryption management. VMware provides features to control access to encryption-related data and track user activity.
- Role-Based Access Control (RBAC): VMware’s RBAC enables administrators to assign specific roles and access permissions to users, ensuring that only authorized personnel can manage encryption-related data.
- Auditing and Logging: VMware’s auditing and logging features provide a detailed record of user activity, including changes to encryption settings, key management, and access control. This helps administrators track data access and compliance with regulatory requirements.
Guidelines for Organizing Encryption-Related Data
To effectively organize encryption-related data in VMware, follow these guidelines:
- Develop a data categorization strategy based on organizational needs and regulatory requirements.
- Use VMware’s built-in categorization features and custom categories to organize virtual machines, VM disks, and encryption keys.
- Implement Role-Based Access Control (RBAC) to control access to encryption-related data.
- Configure auditing and logging to track user activity and ensure compliance with regulatory requirements.
Proper data organization and categorization simplify data retrieval, facilitate incident response, and enhance data security. Regularly review and update your data organization strategy to ensure it remains effective and compliant.
Creating and Implementing Custom Encryption Policies in VMware
Creating custom encryption policies in VMware allows administrators to tailor their encryption settings to specific business needs or security requirements. This ensures that sensitive data is protected consistently across various virtual machines, without unnecessary restrictions or limitations.
To create effective custom encryption policies in VMware, organizations should identify their key objectives, such as compliance with regulatory requirements or protection of specific types of data. They can then configure encryption settings accordingly, balancing security with operational considerations like performance and usability.
Defining Custom Encryption Policies
When defining custom encryption policies, consider the following steps.
- Identify the encryption requirements for your organization, including regulatory compliance, data protection, and organizational standards. This will help guide the development of your custom policy. You might need to reference guidelines from local or global governing bodies to ensure you meet all necessary legal requirements.
- Determine which virtual machines should be subject to the custom encryption policy and which encryption settings will be applied. This could involve segmenting your virtual machines into different tiers based on sensitivity levels and encrypting the most sensitive virtual machines accordingly.
- Configure the encryption settings for each group of virtual machines based on your custom policy. This will involve specifying encryption algorithms, key sizes, and other security parameters tailored to the sensitivity level of the data being protected.
- Implement and test your custom encryption policy in a controlled environment before deploying it across production virtual machines. This will help ensure that the policy operates as intended without negatively impacting system performance or usability.
Custom Encryption Policy Implementation
Implementing custom encryption policies involves several steps, which can be summarized as follows.
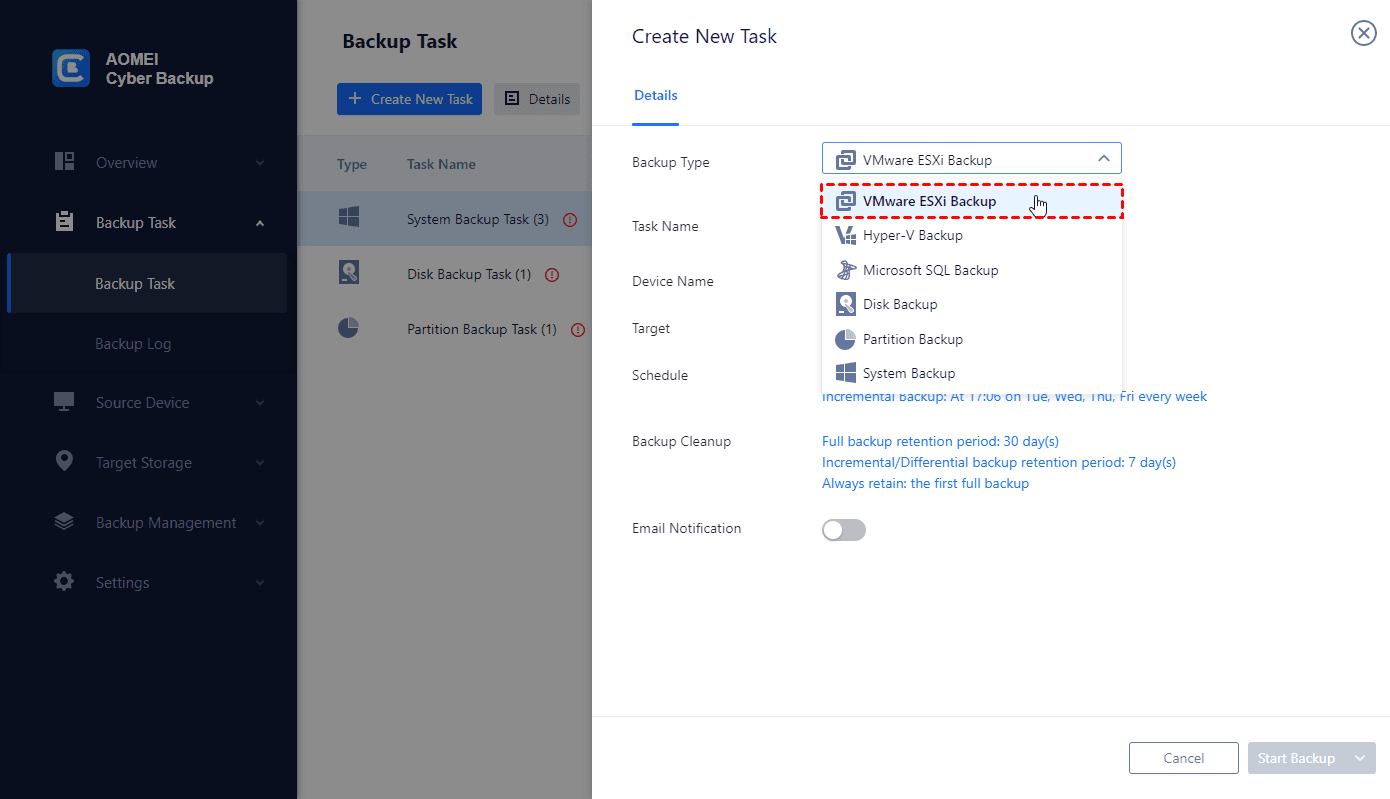
- In your VMware environment, navigate to the appropriate menu to manage virtual machine encryption policies. This is usually found under the advanced settings or VM storage options.
- Create a new custom policy, specifying your chosen encryption settings and selecting the groups of virtual machines that will be subject to this policy.
- Review your policy configuration to ensure it meets all your identified requirements. If necessary, make adjustments to encryption settings or virtual machine assignments to achieve complete compliance.
- Activate and confirm that the custom policy has taken effect across the specified virtual machines, checking their encryption status and ensuring that no issues have arisen from the implementation.
- Continuously monitor and update your custom encryption policies to comply with changing security requirements, such as shifts in regulatory landscapes or new technologies becoming available in the market.
Importance of Policy Management in Encryption
Proper policy management is crucial in creating a reliable and scalable encryption framework, as illustrated in the following details.
- Regularly update your custom policies to reflect changes in organizational security strategies and compliance requirements, thereby ensuring continuous data protection and regulatory adherence.
- Monitor the performance of your virtual machines under different encryption policies to identify potential bottlenecks and areas for process improvement.
- Use automation tools to simplify the management of custom encryption policies and minimize manual errors in configuration and execution. Automated policy updates and reporting can facilitate a centralized view of your entire encryption infrastructure.
Compliance and Regulatory Considerations
Understanding regulatory considerations is crucial when implementing custom encryption policies, involving knowledge of relevant regulations and standards in your region.
- Familiarize yourself with the specific regulatory requirements of your industry and location. For example, in healthcare settings, adherence to HIPAA is crucial.
- Assess the level of encryption required to meet legal demands for data protection and implement this within your custom policies.
- Keep records of your custom encryption policies and associated compliance activities. These records can serve as a safeguard and assist with auditing should a regulatory query arise.
Demonstrating Encryption-Related Features in VMware
VMware provides a robust set of features to help organizations manage and enforce encryption policies within their virtual environments. One of the key features of VMware is its ability to demonstrate encryption-related functionality, allowing administrators to understand how encryption works and how it can be used to protect sensitive data. In this section, we will explore the key features related to encryption in VMware and provide a demonstration of how to use encryption features.
Key Features of VMware Encryption
VMware offers several key features that make encryption easy to manage and implement within virtual environments. Some of the key features include:
- Encryption at Rest: VMware provides encryption at rest, which ensures that data stored on virtual machine disks is encrypted, even when the virtual machine is powered off.
- Encryption in Transit: VMware also provides encryption in transit, which ensures that data transmitted between virtual machines is encrypted, making it more difficult for unauthorized parties to intercept and read the data.
- Key Management: VMware provides a key management system that makes it easy to manage and rotate encryption keys, ensuring that sensitive data is always protected.
- Policy-Based Encryption: VMware allows administrators to create custom policies based on user-defined criteria, making it easy to enforce encryption requirements without disrupting business operations.
The key features of VMware encryption provide organizations with a robust set of tools to manage and enforce encryption policies within their virtual environments. By using these features, organizations can ensure that sensitive data is always protected, even in the event of a security breach.
Demonstrating Encryption-Related Features in VMware
To demonstrate encryption-related features in VMware, administrators can follow a few simple steps:
- Log in to the vCenter Server and navigate to the virtual machine that needs to be encrypted.
- Right-click on the virtual machine and select Convert to Encrypted VM.
- Follow the prompts to select the encryption algorithm and key size, and then provide a password to encrypt the virtual machine disk.
- Verify that the virtual machine is now encrypted by checking the vSphere Client for the encrypted icon.
By following these steps, administrators can demonstrate the encryption-related features of VMware and ensure that sensitive data is always protected.
Role of Documentation and User Guides
Documentation and user guides play a critical role in understanding encryption-related functionality in VMware. VMware provides comprehensive documentation and user guides that detail the steps required to implement encryption in virtual environments.
“Encryption is a critical component of any organization’s security posture. It’s essential to understand how encryption works and how it can be used to protect sensitive data.”
By utilizing VMware documentation and user guides, administrators can quickly and easily implement encryption in virtual environments, ensuring that sensitive data is always protected.
Designing a Data Backup and Recovery Plan for VMware with Encryption: How To Decrypt Virtual Machine Vmware
A data backup and recovery plan is crucial for any VMware environment, especially when encryption is involved. With the ever-increasing importance of data protection and compliance, having a well-designed data backup and recovery plan in place can help organizations avoid data loss, reduce downtime, and ensure business continuity. In the event of a disaster or data breach, a reliable data backup and recovery plan can help organizations quickly recover their encrypted data and minimize the impact on operations.
The Importance of Data Duplication and Redundancy
Data duplication and redundancy are essential components of a robust data backup and recovery plan. By duplicating and storing data in multiple locations, organizations can ensure that their encrypted data is readily available in case of a disaster or data loss. This approach also reduces the risk of single points of failure and provides a higher degree of data availability and integrity.
Data duplication involves creating multiple copies of data and storing them in different locations. This can be done using various methods, such as:
* Synchronous replication: This involves maintaining real-time copies of data across different locations. This method ensures that data is always available and up-to-date, regardless of the location.
* Asynchronous replication: This involves scheduling data replication at regular intervals. This method is often used in environments where data growth is slower and there is a higher tolerance for data latency.
Redundancy, on the other hand, involves storing data in multiple formats or locations to ensure that it can be recovered in the event of a disaster or data loss. This can be achieved through:
* Multisite storage: This involves storing data across multiple sites or locations to ensure that it can be recovered in case of a disaster at one location.
* Storage tiering: This involves storing data in different storage tiers based on its type, frequency of access, and retention requirements. This approach helps to optimize storage resources and improves data recovery times.
*
- Storage redundancy methods include:
- Disk mirroring:
- RAID (Redundant Array of Independent Disks):
- Erasure coding:
- Flash-based storage:
This involves creating near-synchronous copies of data across different disks to ensure high availability and redundancy.
This involves combining multiple disks into a single logical unit to improve data storage and redundancy.
This involves dividing data into smaller chunks and storing parity data to enable efficient data recovery and redundancy.
This involves using flash storage to store frequently accessed data, which can improve performance and reduce latency during data recovery.
Creating a Data Backup and Recovery Plan for VMware with Encryption
A data backup and recovery plan for VMware with encryption should be tailored to meet the specific needs of the organization. Here are some steps to consider:
*
Inventory and Classification:
Identify and classify data based on its sensitivity, business value, and regulatory requirements. This will help determine the level of encryption, backup frequency, and recovery procedures for each data set.
*
Data Deduplication and Compression:
Implement data deduplication and compression techniques to reduce the amount of data that needs to be backed up and stored. This can improve data storage and backup times while reducing storage costs.
*
Encryption and Key Management:
Implement strong encryption and key management practices to protect data in transit and at rest. This includes using industry-recognized encryption protocols and storing encryption keys securely.
*
Backup Scheduling and Frequency:
Determine the backup scheduling and frequency based on the business requirements and regulatory compliance. This may include full, incremental, and differential backups.
*
Backup Location and Storage:
Decide on the backup location and storage options, such as local, remote, or cloud-based storage. Consider using cloud-based storage services that specialize in data backup and recovery.
*
Recovery Procedures:
Establish recovery procedures, including data retrieval, encryption key recovery, and system restore. This should involve testing and validating recovery processes to ensure they work as expected.
*
Training and Maintenance:
Provide training and support for staff involved in data backup and recovery operations. Regularly review and update the data backup and recovery plan to ensure it remains effective and compliant with changing regulatory requirements.
Ultimate Conclusion
In conclusion, decrypting virtual machine VMware requires a thorough understanding of encryption methods, key management, and secure encryption strategies. By following the steps and best practices Artikeld in this guide, you can ensure the secure decryption of your virtual machine data.
Top FAQs
What is the difference between symmetric and asymmetric encryption in VMware?
Symmetric encryption uses a single key for both encryption and decryption, while asymmetric encryption uses a public key for encryption and a private key for decryption.
How do I manage encryption keys in VMware?
You can manage encryption keys in VMware using the vSphere Client or through scripting. It’s essential to regularly rotate and revoke keys to maintain security.
Can I recover encrypted virtual machine data if I lose the encryption key?
No, you cannot recover encrypted virtual machine data if you lose the encryption key. It’s crucial to store and manage keys securely to prevent data loss.
What is the best practice for designing a secure encryption strategy in VMware?
The best practice is to use a combination of encryption methods, regularly rotate and revoke keys, and implement a secure key management system.