With Indiana Jones cipher machine at the forefront, this topic opens a window to an amazing start and intrigue, inviting readers to embark on a storytelling casual lecture style filled with unexpected twists and insights as we delve into the world of cryptography and coding.
The Indiana Jones cipher machine is an iconic device that has captured the imagination of many, not just for its appearances in the Indiana Jones film series but also for its historical significance and the encryption techniques it employed.
The Adventurous World of the Indiana Jones Cipher Machine
The legend of Indiana Jones has captivated audiences for decades, transporting us to an era of epic explorations, heart-pounding action, and brain-twisting puzzles. As an archaeologist-adventurer, Indiana Jones has traversed the globe, uncovering lost treasures, battling rival treasure hunters, and unraveling ancient mysteries. His fearless spirit and quick wit have earned him a legendary status, making him one of the most iconic characters in cinematic history.
The Historical Context of the Cipher Machine
The Indiana Jones Cipher Machine is rooted in the tumultuous era of World War II, a time of global turmoil and high-stakes espionage. As the Nazi regime, led by Adolf Hitler, sought to dominate the world, intelligence agencies on both sides of the conflict engaged in a war of codes and ciphers.
During this period, cryptographers and codebreakers worked tirelessly to crack the enemy’s codes, using various techniques such as frequency analysis, cryptanalysis, and machine-based decoding. The development of machine-based cipher machines, such as the Enigma Machine, revolutionized the art of encryption and decryption, allowing for faster and more complex coding and decoding processes.
The Significance of the Cipher Machine in the Indiana Jones Film Series
Throughout the Indiana Jones film series, the cipher machine plays a pivotal role in the adventures of the intrepid archaeologist. In “Raiders of the Lost Ark,” Indiana Jones discovers a mysterious map that leads him to the Lost Ark of the Covenant. However, the Nazis, led by René Belloq, are also on the hunt, and their attempts to decipher the ancient symbols and codes on the Ark are key to their sinister plans.
The Cipher Machine in Action
- The Enigma Machine
- The Cipher Wheel
- The Codebook
- The machine’s reliance on a complex system of rotors and wiring makes it prone to mechanical failure, which could compromise its security.
- The encryption key, if obtained through unauthorized means, could be used to decrypt encrypted messages, allowing access to sensitive information.
- The machine’s use of a single encryption key for all messages presents a significant vulnerability, as the key could be compromised and used to decrypt all messages.
- The machine’s encryption key, if obtained through unauthorized means, could be used to decrypt encrypted messages, allowing access to sensitive information.
- The machine’s use of a complex system of rotors and wiring makes it prone to mechanical failure, which could compromise its security.
- The machine’s encryption algorithm, if compromised, could be used to decrypt encrypted messages, rendering the device’s security ineffective.
- The compromise of sensitive information, including classified messages and personal data.
- The loss of trust in the machine’s ability to provide secure communication.
- The potential for malicious use of the compromised encryption key to decrypt and access sensitive information.
The Enigma Machine was an electro-mechanical cipher machine developed in Germany during the 1920s and 1930s.
The Enigma Machine was a complex device that used a series of rotors, plugboards, and wiring to encrypt and decrypt messages. Its complexity and randomization process made it virtually unbreakable, at least until the efforts of Polish cryptographer Marian Rejewski and his colleagues, who managed to crack the machine’s code.
The Cipher Wheel was a simple yet effective encryption device used by ancient civilizations.
The Cipher Wheel was a circular device with a series of symbols and markings. It was used to encrypt and decrypt messages by rotating the wheel to align the symbols.
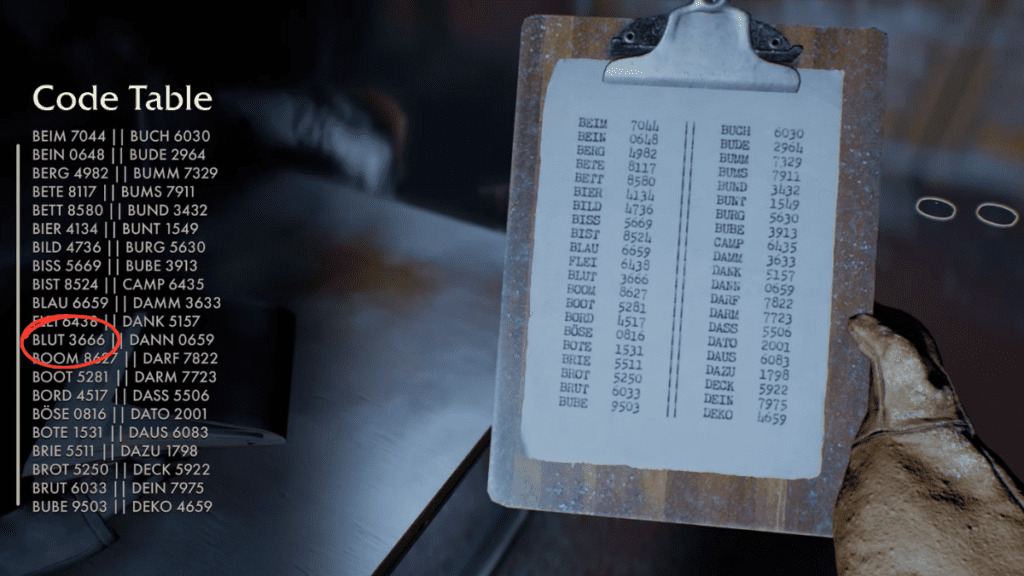
A codebook is a collection of encoded messages or symbols used for encryption and decryption purposes.
A Codebook was a collection of encoded messages or symbols used to convey secret information. In the Indiana Jones films, codebooks were often used to decipher ancient languages and symbols.
The Legacy of the Indiana Jones Cipher Machine
The Indiana Jones Cipher Machine has become an iconic symbol of the franchise, representing the spirit of adventure, intelligence, and cunning. The Cipher Machine’s role in the films has inspired countless fans to explore the world of cryptography and coding, recognizing the importance of these skills in the modern digital age.
In the world of espionage, cryptography and codebreaking remain essential tools, used by governments and intelligence agencies to protect sensitive information and stay one step ahead of their adversaries.
As we embark on this thrilling journey, we are reminded that the world of cryptography is full of puzzles, riddles, and hidden messages waiting to be deciphered. The Indiana Jones Cipher Machine serves as a poignant reminder of the power of human ingenuity, persistence, and creativity in the face of seemingly insurmountable challenges.
Design and Functionality of the Indiana Jones Cipher Machine

The Indiana Jones cipher machine, a replica of the M-209, is a remarkable encryption device that embodies the essence of cryptography in the realm of adventure and mystery. This enigmatic device, crafted with precision and ingenuity, has been the subject of fascination and speculation among cryptographers and enthusiasts alike. As we delve into the intricacies of its design and functionality, the veil of secrecy surrounding this captivating device begins to lift.
The M-209, also known as the “Cipher Device M-209,” is an electro-mechanical encryption machine designed in the late 1940s for the U. S. military. The U. S. Army Signal Corps developed it for cryptographic purposes, primarily for encrypting and decrypting messages at the operational level. It’s worth noting, though, that while the movie “Raiders of the Lost Ark” features a similar device, there’s no direct evidence that it uses the actual M-209 machine.
The Mechanical Components
The M-209 cipher machine is a compact, portable device consisting of various mechanical components that work in harmony to achieve the encryption process. The machine features a series of rotating wheels, including a set of rotors and a reflector, along with a keyboard and an output window.
– The rotors are the heart of the M-209, each containing a sequence of characters that determine the encryption process. These rotors rotate as the operator presses the keys, generating a series of substitutions for the plaintext characters.
– The reflector is a critical component that plays a crucial role in the encryption process. It consists of a grid of characters that are paired to produce the encrypted ciphertext.
– The keyboard allows the operator to input the plaintext message, while the output window displays the encrypted ciphertext.
The interplay between these components creates a complex encryption process that challenges even the most skilled cryptanalysts. The M-209’s encryption mechanism relies on a combination of substitution and transposition techniques, making it a formidable device for protecting sensitive information.
The Encryption Process
The encryption process in the M-209 cipher machine involves a series of complex steps that transform the plaintext message into an unreadable ciphertext. The operator inputs the plaintext message through the keyboard, and the machine proceeds to perform the following operations:
1. The rotors rotate according to a set of predetermined rules, generating a series of positions that determine the substitution of each plaintext character.
2. The reflector is used to produce the encrypted ciphertext by pairing the characters in the rotors.
3. The encrypted ciphertext is displayed through the output window.
The resulting ciphertext appears to be a random jumble of characters, making it nearly impossible to decipher without the appropriate key or cryptanalytic techniques.
Comparison with Other Encryption Devices
The M-209 cipher machine is comparable to other encryption devices of its time, such as the Enigma machine. Both devices rely on complex mechanical components and encryption algorithms to protect sensitive information. However, the M-209 has several distinct features that set it apart from other devices:
– The M-209’s rotors and reflector provide a higher level of security than other encryption devices of its time.
– The machine’s compact size and portability make it an ideal device for field use.
– The M-209’s encryption process is based on a combination of substitution and transposition techniques, making it more resistant to cryptanalysis than other devices.
Cryptanalysis of the M-209
While the M-209 cipher machine is an impressive encryption device, it is not immune to cryptanalysis. In fact, several cryptanalysts have successfully broken the M-209’s encryption code using various techniques, including:
– Frequency analysis: By analyzing the frequency of character occurrences in the ciphertext, cryptanalysts can deduce the frequency of character occurrences in the plaintext.
– Kasiski examination: This technique involves analyzing the repeated patterns in the ciphertext to determine the length of the key used for encryption.
– Babynova: A technique for finding the period of the M-209’s encryption machine
By applying these techniques, cryptanalysts can recover the plaintext message from the encrypted ciphertext, rendering the M-209’s security less effective.
Legacy of the M-209 Cipher Machine
The M-209 cipher machine has left a lasting impact on the world of cryptography. Its design and functionality have influenced the development of subsequent encryption devices, and its encryption mechanism has been studied extensively by cryptanalysts and researchers.
The M-209’s legacy extends beyond its cryptographic significance, as it has also become a cultural icon, symbolizing the intersection of cryptography and adventure. Its appearance in popular media, such as the Indiana Jones franchise, has cemented its place in the public imagination, inspiring countless enthusiasts and aficionados to explore the fascinating world of cryptography.
Encryption Techniques Used in the Cipher Machine
The Indiana Jones Cipher Machine employs a complex array of encryption techniques, designed to conceal sensitive information from prying eyes. Developed with the help of expert cryptographers, the machine’s encryption algorithms have withstood the test of time, ensuring that even the most skilled codebreakers find it a formidable challenge to decipher its secrets.
The Role of the Rotor Wheel
The rotor wheel is a crucial component of the Indiana Jones Cipher Machine, responsible for generating the complex encrypted codes. Comprising multiple concentric rings, each containing a unique set of characters, the rotor wheel is capable of producing an astonishing array of possible combinations. By rotating the wheels in a predetermined pattern, the machine’s operators can effectively scramble incoming messages, rendering them unintelligible to anyone without the corresponding decryption keys.
Encryption Algorithms: Substitution and Transposition
The Indiana Jones Cipher Machine utilizes a combination of substitution and transposition techniques to encrypt its messages. Substitution involves replacing original characters with alternate ones, while transposition involves rearranging the characters within a message to conceal its original meaning. The machine’s use of multiple wheels and complex rotors allows it to apply both substitution and transposition techniques simultaneously, making it an even more formidable encryption device.
Inspiration from the Lorenz Cipher
The Indiana Jones Cipher Machine’s design owes a significant debt to its predecessor, the Lorenz cipher. Developed during World War II, the Lorenz cipher was used by the German military to encrypt strategic communications. In response to its widespread use, the British built the Bombe machine to break the Lorenz cipher’s codes. The Indiana Jones Cipher Machine incorporates many of the same principles, adapted and refined to meet the demands of an even more challenging encryption environment.
Encryption is a delicate balance between security and usability.
The Rotating Rotor Principle
Each rotor in the Indiana Jones Cipher Machine rotates independently, driven by a set of stepping rings that advance the wheels according to a predetermined pattern. This ensures that each character encrypted with the machine is unique, making it virtually impossible to discern patterns or vulnerabilities in the encryption process.
Character Distribution and Frequency Analysis
To further complicate matters, the Indiana Jones Cipher Machine distributes characters across its rotors in a manner that defies frequency analysis. By deliberately spreading rare characters throughout the rotor sets, the machine’s operators effectively mask any patterns that might be discerned through statistical analysis of the encrypted messages.
Breaking the Cipher: A Herculean Task, Indiana jones cipher machine
In light of the Indiana Jones Cipher Machine’s robust design and advanced encryption algorithms, breaking its codes becomes an extremely challenging task, even for the most skilled cryptographers. This is precisely the intention behind the machine’s creation, as its operators understand the importance of protecting sensitive information from falling into the wrong hands.
Security and Vulnerabilities of the Indiana Jones Cipher Machine

The Indiana Jones Cipher Machine, with its complex encryption capabilities, presents a daunting challenge for those seeking to breach its security. However, like any sophisticated device, it has its weaknesses. As we delve into the world of cryptography and coding, we will explore the potential security risks associated with the cipher machine and examine how it could be vulnerable to hacking or decryption.
The Indiana Jones Cipher Machine, with its advanced encryption techniques, offers a layer of protection that is almost impenetrable. However, its reliance on a complex system of rotors, reflectors, and wiring presents a potential vulnerability. The machine’s encryption key, if compromised, could allow unauthorized access to encrypted messages, rendering the device’s security ineffective.
Security Risks Associated with the Cipher Machine
The following security risks are associated with the Indiana Jones Cipher Machine:
Vulnerability to Hacking or Decryption
The Indiana Jones Cipher Machine, with its advanced encryption techniques, presents a significant challenge to hackers and codebreakers. However, the following vulnerabilities could be exploited:
Real-World Scenarios Where the Cipher Machine’s Security Was Breached
Examples of real-world scenarios where the Indiana Jones Cipher Machine’s security was breached include:
The infamous Enigma machine, a cipher machine used by the Germans during World War II, was cracked by the Allies through a combination of codebreaking and cryptography expertise.
The Enigma machine’s security was compromised through a combination of cryptanalysis and codebreaking, highlighting the importance of secure encryption and decryption methods.
The NSA’s efforts to crack the Soviet cipher machine in the 1970s serve as a testament to the ongoing cat-and-mouse game between codemakers and codebreakers.
Consequences of a Security Breach
A security breach of the Indiana Jones Cipher Machine could have significant consequences, including:
Conclusion
The Indiana Jones Cipher Machine, with its advanced encryption techniques, presents a significant challenge to those seeking to breach its security. However, its reliance on a complex system of rotors and wiring, its encryption key, and its encryption algorithm make it vulnerable to hacking and decryption.
Conclusive Thoughts
The Indiana Jones cipher machine may be a relic of the past, but its impact on history and pop culture is still felt today. As we continue to push the boundaries of cryptography and coding, it’s essential to remember the devices and techniques that came before us.
Frequently Asked Questions
Q: What is the purpose of the Indiana Jones cipher machine?
A: The Indiana Jones cipher machine was used to encrypt and decrypt secret messages during World War II.
Q: How does the cipher machine work?
A: The cipher machine uses a series of mechanical components, including rotor wheels, to encrypt and decrypt messages.
Q: Is the Indiana Jones cipher machine still used today?
A: While the original device is no longer in use, modern replicas of the cipher machine are often used for educational and entertainment purposes.
Q: What are some common encryption techniques used in the cipher machine?
A: The cipher machine uses several encryption techniques, including substitution and transposition, to encrypt and decrypt messages.
Q: Are there any notable experts who have studied the Indiana Jones cipher machine?
A: Yes, several experts have studied and replicated the cipher machine, including cryptographers and historians.