Java Virtual Machine What is the backbone of the Java ecosystem, enabling platform independence and a wide range of security features. A Java Virtual Machine, or JVM, is a run-time environment that executes Java bytecode on a variety of devices, from desktop computers to mobile phones. This remarkable technology has made Java one of the most popular programming languages in the world.
The JVM is a crucial part of what makes Java so versatile and widely used. It provides a layer of abstraction between the Java code and the underlying hardware, allowing the same code to run on different platforms without modification. This means that Java developers can write once and run anywhere, without worrying about compatibility issues.
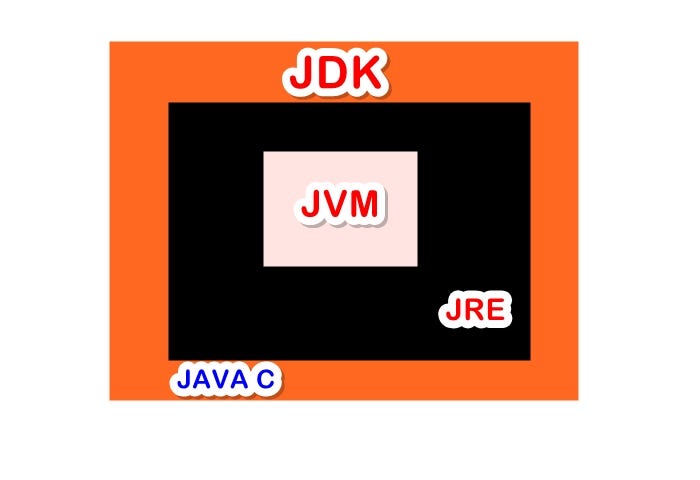
The Java Virtual Machine (JVM)
The Java Virtual Machine (JVM) is a crucial component of the Java ecosystem, serving as the runtime environment for Java programs. It plays a vital role in enabling platform independence, allowing Java developers to write, compile, and run code on any device that has a JVM installed, without worrying about the underlying hardware or operating system.
The JVM is responsible for loading, linking, and executing Java bytecode, as well as managing memory and providing a set of services to Java programs, such as exception handling, synchronization, and thread management. By doing so, the JVM allows Java developers to focus on writing code without worrying about the details of platform-specific implementation.
The JVM’s role in enabling platform independence is a key benefit for Java developers. By compiling Java code into platform-independent bytecode, developers can write code that can run on any device with a JVM, without modifications. This allows Java programs to be portable across different operating systems, hardware architectures, and devices, making Java a popular choice for developing cross-platform applications.
Benefits of Using the JVM
The JVM provides several benefits to Java developers, including:
The JVM’s ability to detect and prevent memory-related issues, such as memory leaks and buffer overflows, helps ensure the stability and reliability of Java programs.
The JVM’s automatic memory management features, such as garbage collection, reduces the risk of memory-related bugs and makes it easier to write and maintain Java code.
The JVM’s ability to optimize and improve the performance of Java programs, through techniques such as just-in-time (JIT) compilation and dynamic recompilation, helps improve the overall user experience.
The JVM’s platform independence allows Java developers to write code that can run on any device with a JVM, without worrying about the underlying hardware or operating system, making it a popular choice for developing cross-platform applications.
- Memory management
- Performance optimization
- Platform independence
- Security
- Robustness
- The Class Loader is responsible for resolving symbolic references to types in the loaded classes.
- The Class Loader uses caching to improve performance and prevent duplicate loading of classes.
- The Class Loader is capable of resolving class conflicts by using a class hierarchy or by ignoring the class.
- The Interpreter interprets the Java bytecodes directly, executing them one at a time.
- The JIT Compiler compiles the Java bytecodes into native machine code, improving execution time and performance.
- The Garbage Collector manages memory by identifying and reclaiming objects that are no longer in use.
- The Method Area stores the class metadata and constants.
- The Heap stores the instances of Java objects.
- The Stack stores the method call stack and local variables.
- The Native Method Stack stores the native method call stack.
- The Class Loader uses the API to load classes and resolve symbol references.
- The Execution Engine uses the API to execute Java bytecodes and manage the garbage collection process.
- The Runtime Data Areas use the API to store and retrieve data used by the Java application.
- -Xms size – sets the initial heap size
- -Xmx size – sets the maximum heap size
- -XX:NewRatio ratio – sets the new ratio, which determines the heap size of the young generation.
- -XX:SurvivorRatio ratio – sets the survivor ratio, which determines the size of the survivor space in the young generation.
- -Xmx size – sets the maximum number of threads
- -Xss size – sets the maximum stack size for each thread
- -XX:+UseParallelGC – enables parallel garbage collection
- -XX:+UseParallelGC – enables parallel garbage collection
- -XX:+UseConcMarkSweepGC – enables concurrent mark-and-sweep garbage collection
- -XX:+UseG1GC – enables low-pause-time garbage collection
- -X property name=property value – sets a JVM property
- -XX option – sets a JVM option
- -jar file -jar – sets the main class to be executed
- Command-line arguments – JVM options can be specified as command-line arguments when running the Java application
- Properties file – JVM options can be specified in a properties file, which can be loaded using the -D option
- Document the JVM configuration
- Test the JVM configuration
- Monitor the JVM performance
- Adjusting GC algorithms: Developers can adjust the GC algorithms to suit their application’s needs. For example, the Parallel GC is suitable for applications with multiple CPU cores, while the CMS GC is better suited for applications with high pause times.
- Heap sizing: Developers can adjust the heap size to ensure that the JVM has enough memory to handle the application’s memory footprint. A larger heap size can lead to longer GC pause times, while a smaller heap size can lead to more frequent GC cycles.
- Pause times: Developers can adjust the GC pause times to find the right balance between garbage collection frequency and pause times. Higher pause times can improve GC efficiency but may cause application stalls.
- Heap usage analysis: Developers can use heap usage analysis tools to monitor the JVM’s heap usage and identify memory leaks or inefficient memory usage patterns.
- Heap profiling: Developers can use heap profiling tools to analyze the JVM’s heap usage and identify memory-intensive objects, methods, or classes.
- Garbage collection metrics: Developers can use garbage collection metrics, such as GC count, GC time, and GC pause time, to monitor JVM performance.
- Heap size: Developers can use heap size metrics, such as initial heap size, maximum heap size, and heap usage, to monitor JVM performance.
- Memory usage: Developers can use memory usage metrics, such as memory usage, memory allocation, and memory deallocation, to monitor JVM performance.
- CPU usage: Developers can use CPU usage metrics, such as CPU usage, CPU load, and CPU idle time, to monitor JVM performance.
- System resources: Developers can use system resources metrics, such as disk usage, network usage, and system load, to monitor JVM performance.
- Serial GC: This is the default garbage collection algorithm in the JVM, which runs in serial mode and uses a single thread to collect garbage. It is suitable for small Java applications with low memory requirements.
- CMS (Concurrency Mark-and-Sweep) GC: This algorithm is designed for low-pause-time collection and uses a concurrent mark-and-sweep approach to collect garbage. It is suitable for applications that require low pause times and can tolerate increased garbage collection frequencies.
- G1 (Garbage-First) GC: This is a low-pause-time garbage collector that uses a generational approach to collect garbage. It is suitable for large Java applications with high memory requirements and is designed to reduce pause times.
- Parallel GC: This algorithm uses multiple threads to collect garbage in parallel, which improves overall system performance. It is suitable for large Java applications with high memory requirements and is designed to reduce pause times.
- Set the minimum and maximum heap sizes to ensure that the JVM has enough memory to perform garbage collection.
- Choose the correct garbage collection algorithm based on the application’s memory requirements and performance needs.
- Tune garbage collection parameters such as the garbage collection frequency, pause time, and heap sizes based on performance monitoring data.
- Use garbage collection logging to identify and resolve performance issues.
- jdb (Java Debugger): A command-line tool for debugging Java programs. It allows developers to set breakpoints, step through code, and examine variables and expressions.
- jconsole (Java Console): A graphical user interface (GUI) for monitoring and debugging Java applications. It provides real-time information about memory usage, CPU activity, and threads.
- VisualVM (Visual Virtual Machine): A GUI-based tool for profiling and monitoring Java applications. It offers detailed information about performance, memory usage, and CPU activity.
- Java Mission Control (JMC): A commercial tool for monitoring and debugging Java applications. It provides advanced features such as real-time monitoring, thread dumps, and heap analysis.
- VisualVM (Visual Virtual Machine): In addition to its debugging features, VisualVM also offers profiling capabilities such as CPU profiling, memory profiling, and thread profiling.
- Java Mission Control (JMC): JMC provides advanced profiling features such as real-time monitoring, thread dumps, and heap analysis.
- JProfiler: A commercial profiling tool for Java applications. It offers detailed information about performance, memory usage, and CPU activity.
- Use the correct tool for the job: Choose the tool that best addresses the specific debugging or profiling need.
- Familiarize yourself with the tool: Spend time learning the tool’s features and functionality to ensure effective use.
- Analyze results carefully: Interpret data accurately and make informed decisions based on findings.
- Test and verify changes: Before implementing fixes, test and verify the changes to ensure they resolve the issue.
- Specify the Java version: Always specify the Java version to use when running the application. This ensures that the JVM uses the correct version of the Java Runtime Environment (JRE) and prevents potential compatibility issues.
- Set memory limits: Establishing memory limits helps prevent applications from consuming excessive resources, reducing the risk of memory leaks and improving overall system stability.
- Configure garbage collection: Garbage collection plays a vital role in maintaining memory efficiency. Optimizing garbage collection settings (e.g., garbage collector type, concurrent mode, and maximum pause time) can significantly impact application performance.
- Set classpath and library paths: Correctly setting the classpath and library paths ensures that the JVM has access to all required classes and libraries, avoiding potential errors and exceptions.
- Cheap and expensive operations: Identify and minimize expensive operations (e.g., database queries, complex calculations) and replace them with cheaper alternatives where possible.
- Memory allocation: Optimize memory allocation through techniques like caching, lazy loading, and reducing object creation to prevent memory leaks and improve performance.
- Garbage collection optimization: Fine-tune garbage collection settings to minimize pause times, reduce memory allocation, and optimize performance.
- Code caching: Employ code caching to reduce the overhead of repeated method calls and improve response times.
- Validate user input: Always validate user input to prevent SQL injection, cross-site scripting (XSS), and other attacks that exploit unchecked user input.
- Use secure communication protocols: Employ secure communication protocols (e.g., HTTPS, TLS) to protect data exchanged between the application and users.
- Implement access control: Establish proper access controls to prevent unauthorized access to sensitive data, resources, and functionalities.
- Monitor and detect threats: Regularly monitor and analyze system logs to detect potential security threats and take prompt action to resolve any issues that arise.
- Memory usage: Keep track of memory usage, including heap size, allocated objects, and garbage collection activity.
- CPU usage: Monitor CPU usage, including average load, number of threads, and CPU time.
- Garbage collection metrics: Track garbage collection metrics, such as pause times, garbage collection counts, and promotion failures.
- Thread counts and locks: Monitor thread counts, lock contention, and synchronization activity to identify potential bottlenecks.
- Sign and verify JAR files: Sign JAR files to ensure authenticity and verify their signature before loading them into the application.
- Implement sandboxing: Employ sandboxing techniques to restrict application access to sensitive resources and prevent security breaches.
- Regularly update and patch the JVM: Regularly update and patch the JVM to ensure the latest security patches and fixes are applied.
The JVM’s automatic memory management features, such as garbage collection, reduce the risk of memory-related bugs and make it easier to write and maintain Java code. Garbage collection is a critical aspect of the JVM, as it helps ensure that memory is properly released when it is no longer being used, preventing memory leaks and memory-related errors.
Garbage collection is a process by which the JVM identifies and reclaims memory occupied by objects that are no longer referenced by any active program threads.
The JVM’s ability to optimize and improve the performance of Java programs, through techniques such as JIT compilation and dynamic recompilation, helps improve the overall user experience. JIT compilation, for example, is a technique used by the JVM to compile frequently executed methods into machine code, improving their performance.
JIT compilation is a technique used by the JVM to compile frequently executed methods into machine code, reducing the overhead of interpretation and improving their performance.
The JVM’s platform independence allows Java developers to write code that can run on any device with a JVM, without worrying about the underlying hardware or operating system. This makes it a popular choice for developing cross-platform applications.
Platform independence allows Java developers to write code that can run on any device with a JVM, without worrying about the underlying hardware or operating system, making it a popular choice for developing cross-platform applications.
The JVM’s built-in security features, such as data execution prevention (DEP) and address space layout randomization (ASLR), help protect against common security threats, such as buffer overflows and stack-based attacks.
Data execution prevention (DEP) is a security feature that prevents code execution in data areas, such as the stack and heap, to prevent stack-based and heap-based attacks.
The JVM’s robustness features, such as error handling and exception management, help ensure that Java programs remain stable and responsive in the face of errors and exceptions.
Error handling and exception management are critical aspects of the JVM, as they help ensure that Java programs remain stable and responsive in the face of errors and exceptions.
Architecture and Components of the JVM
The Java Virtual Machine (JVM) is the runtime environment in which Java bytecodes are executed. The JVM’s architecture consists of multiple components that work together to achieve this task. Understanding the architecture and components of the JVM is essential for developers who want to optimize their Java applications and troubleshoot issues that may arise.
CLASS LOADER COMPONENT
The Class Loader is responsible for loading Java classes into the memory of the JVM. It is divided into three sub-components: Bootstrap Class Loader, Extension Class Loader, and System Class Loader. The Bootstrap Class Loader loads the core Java libraries, while the Extension Class Loader loads Java libraries from the extension directories. The System Class Loader loads classes from the application’s classpath.
EXECUTION ENGINE COMPONENT
The Execution Engine is responsible for executing the Java bytecodes loaded into the memory of the JVM. It consists of the following sub-components: Interpreter, Just-In-Time (JIT) Compiler, and Garbage Collector.
RUNTIME DATA AREAS
The Runtime Data Areas are the memory regions where the JVM stores data used by the Java application. The Runtime Data Areas include the following: Method Area, Heap, Stack, and Native Method Stack.
COMMUNICATION MECHANISM BETWEEN COMPONENTS
The components of the JVM communicate with each other through a mechanism called the Application Programming Interface (API). The API provides a set of standardized functions that allow the components to interact with each other and achieve their tasks.
JVM Options and Configuration
The Java Virtual Machine (JVM) provides a wide range of options that can be used to configure and customize the behavior of the JVM when running a Java application. These options can be used to optimize performance, troubleshoot issues, or customize the behavior of the JVM to suit the specific needs of an application.
JVM Options, Java virtual machine what is
There are several different types of JVM options, including options that control the memory allocation, threading, garbage collection, and security of the JVM.
Memory Allocation
The following JVM options can be used to control the memory allocation of the JVM:
These options allow the JVM to be configured to suit the specific needs of an application, for example, to allocate more or less memory to the heap.
Threading
The following JVM options can be used to control the threading of the JVM:
These options allow the JVM to be configured to suit the specific needs of an application, for example, to allocate more or less resources to each thread.
Garbage Collection
The following JVM options can be used to control the garbage collection of the JVM:
These options allow the JVM to be configured to suit the specific needs of an application, for example, to optimize garbage collection for low latency or high throughput.
Configuring JVM Options
JVM options can be configured in several ways, including:
These options allow the JVM to be configured to suit the specific needs of an application, for example, to optimize performance or troubleshoot issues.
Specifying JVM Options
JVM options can be specified in several ways, including:
li>Environment variables – JVM options can be specified using environment variables.
These options allow the JVM to be configured to suit the specific needs of an application, for example, to optimize performance or troubleshoot issues.
Best Practices
When configuring the JVM, it is generally a good idea to:
This allows the JVM to be configured to suit the specific needs of an application, for example, to optimize performance or troubleshoot issues.
JVM Performance Optimization

JVM performance optimization is a critical aspect of ensuring that Java applications run efficiently and effectively. As Java applications become increasingly complex, it’s essential to optimize the JVM to meet the growing demands of memory, CPU, and system resources. By optimizing the JVM, developers can improve the overall performance, scalability, and reliability of their applications, ultimately leading to better user experiences and business outcomes.
Garbage Collection Tuning
Garbage collection tuning is a crucial aspect of JVM performance optimization. Garbage collection (GC) is a process that frees up memory occupied by unused objects, allowing the JVM to reclaim resources and prevent memory leaks. However, GC can be a performance bottleneck if not properly tuned. To optimize GC, developers can adjust the JVM’s GC algorithms, heap sizes, and pause times to find the right balance between garbage collection frequency and pause times.
Heap Sizing
Heap sizing is another critical aspect of JVM performance optimization. A properly sized heap can ensure that the JVM has enough memory to handle the application’s memory footprint, reducing the need for GC and improving performance. To determine the optimal heap size, developers can use various tools and techniques, such as heap profiling and memory usage analysis.
-1M: Maximum heap size in bytes.
Metrics and Tools for Measuring JVM Performance
Measuring JVM performance is critical to ensuring that the JVM is running efficiently and effectively. Developers can use various metrics and tools to monitor JVM performance, such as garbage collection metrics, heap size, memory usage, CPU usage, and system resources.
JVM Security Features
The Java Virtual Machine (JVM) includes a range of security features designed to protect against common attacks and ensure the secure execution of Java code. Security is a critical aspect of any virtual machine, and the JVM has evolved over time to address various security vulnerabilities.
The JVM’s primary goals in terms of security are to prevent data tampering, restrict access to resources, prevent stack-based buffer overflows, and validate Java source code. In this section, we will delve into the details of the JVM’s security features and explore how they are used to protect against common attacks.
Sandboxing
Sandboxing is a security technique that involves isolating an application or process within a controlled environment, preventing it from interacting with sensitive resources or other applications. The JVM uses a form of sandboxing to ensure that Java code executes safely and without compromising the system or other applications.
When a Java application is run, the JVM creates a sandboxed environment for it, which is a set of permissions and restrictions that define what the application is allowed to do. The sandboxed environment includes a set of built-in security managers that govern the application’s access to system resources and prevent it from performing actions that could compromise the system.
Class Loading and Verification
Class loading and verification are critical components of the JVM’s security features. The JVM’s class loader is responsible for loading Java classes and other resources into the JVM, while the verifier checks the classes to ensure they conform to the Java language specification.
When a Java class is loaded into the JVM, the class loader checks its dependencies, permissions, and other attributes to ensure they conform to the system’s security policy. The verifier, on the other hand, checks the class’s bytecode to ensure it does not contain malicious code or attempts to access sensitive resources.
Bytecode Verification
Bytecode verification is an essential security feature of the JVM that checks the integrity of Java code. The verifier checks the bytecode to ensure it conforms to the Java language specification and does not contain malicious code.
The verifier checks for a range of security issues, including:
– Data type mismatches
– Out of bounds array accesses
– Uninitialized local variables
– Stack overflow and underflow conditions
– Method calls with incorrect parameters
Memory and Resource Management
Memory and resource management are critical aspects of the JVM’s security features, as they help prevent data tampering and restrict access to sensitive resources.
The JVM includes a range of memory and resource management mechanisms, including:
– Garbage collection: This mechanism automatically reclaims memory occupied by discarded objects, preventing memory leaks.
– Memory protection: The JVM includes memory protection mechanisms to prevent Java code from accessing sensitive resources or other applications.
– Resource restrictions: The JVM restricts access to system resources, such as file systems, network sockets, and graphics devices.
Secure Class Loading
Secure class loading is a critical security feature of the JVM that ensures loaded classes conform to the system’s security policy. The JVM includes a range of secure class loading mechanisms, including:
– Code signing: This involves digitally signing Java classes with a trusted certificate, ensuring the classes conform to the system’s security policy.
– Manifest-based security: This involves associating security attributes with Java classes and their dependencies in the manifest file.
– Permissions-based security: This involves defining a set of permissions that govern an application’s access to system resources and other applications.
Security Manager
The Security Manager is a critical component of the JVM’s security features, responsible for controlling an application’s access to system resources and other applications. The Security Manager includes a range of mechanisms for restricting access to sensitive resources, including:
– File system access control: This involves restricting access to file systems, directories, and files based on an application’s security attributes.
– Network socket access control: This involves restricting access to network sockets based on an application’s security attributes.
– Graphics device access control: This involves restricting access to graphics devices, such as monitors and printers.
Debugging and Monitoring
Debugging and monitoring are critical aspects of the JVM’s security features, as they help detect and prevent security issues.
The JVM includes a range of debugging and monitoring mechanisms, including:
– Heap dumps: This involves creating a snapshot of the JVM’s heap to detect memory leaks.
– Stack tracing: This involves tracing the execution of Java code to detect stack-based buffer overflows.
– JVM profiling: This involves tracking performance metrics, such as execution time and memory usage, to detect performance issues.
Best Practices for Securing the JVM
Securing the JVM requires a comprehensive approach, including:
– Implementing secure class loading mechanisms, such as code signing and manifest-based security.
– Defining a secure class loading policy, including a set of permissions that govern an application’s access to system resources and other applications.
– Enabling the Security Manager to control an application’s access to system resources and other applications.
– Monitoring JVM performance and detecting performance issues using heap dumps, stack tracing, and JVM profiling.
JVM Garbage Collection
The Java Virtual Machine (JVM) uses a garbage collector to automatically free the memory allocated to objects that are no longer needed or referenced. This process is known as garbage collection, which allows developers to focus on writing code without worrying about memory management. The JVM’s garbage collector plays a crucial role in maintaining system performance and preventing memory leaks.
Different Garbage Collection Algorithms Used by the JVM
The JVM supports several garbage collection algorithms, each with its own strengths and weaknesses. Some of the most common algorithms include:
Trade-Offs Between Concurrent and Non-Concurrent Garbage Collection
Concurrent garbage collection occurs while the application is still running, whereas non-concurrent garbage collection occurs when the application is paused. The main trade-off between these two approaches is the impact on system performance.
Concurrent garbage collection can lead to increased garbage collection frequencies, but it reduces pause times. Non-concurrent garbage collection can lead to longer pause times, but it reduces garbage collection frequencies.
Tuning Garbage Collection for Better Performance
To achieve optimal performance, you need to tune garbage collection parameters based on the application’s needs. Here are some general guidelines:
By following these guidelines, you can optimize garbage collection performance and ensure that your Java application runs smoothly without memory leaks or performance issues.
JVM Debugging and Profiling Tools
Debugging and profiling tools are essential components of any software development process, helping programmers identify and fix issues, optimize performance, and improve overall code quality. The Java Virtual Machine (JVM) offers a range of debugging and profiling tools that cater to different needs and levels of expertise. This section explores the available tools, their purpose, and functionality, as well as best practices for using them effectively.
Available Debugging Tools
The JVM provides several debugging tools, each designed to address specific debugging needs. The most commonly used tools include:
Each of these tools has its unique features and advantages, and choosing the right tool depends on the specific debugging needs and the developer’s level of expertise.
Available Profiling Tools
Profiling tools help identify performance bottlenecks and optimize code execution. The JVM provides several profiling tools, including:
Profiling tools help identify performance issues and provide recommendations for optimization. Choosing the right profiling tool depends on the specific needs and the level of expertise.
Best Practices for Debugging and Profiling
To get the most out of debugging and profiling tools, follow these best practices:
By following these best practices and using the available debugging and profiling tools, developers can optimize their code, identify and fix issues, and improve overall code quality.
JVM Best Practices: Java Virtual Machine What Is
The Java Virtual Machine (JVM) is a crucial component of the Java ecosystem, and its optimal use is essential for developing efficient, scalable, and secure applications. JVM best practices encompass a range of strategies for configuring, optimizing, and securing the JVM to ensure it runs smoothly and effectively.
The importance of adhering to JVM best practices cannot be overstated, as it directly impacts the performance, reliability, and security of the applications built on top of it. By following these guidelines, developers can avoid common pitfalls, optimize resource utilization, and enhance the overall user experience.
Configuration Best Practices
Configuring the JVM is a critical aspect of ensuring optimal performance and security. Here are some key configuration best practices to keep in mind:
Proper JVM configuration is essential for ensuring optimal performance, security, and reliability. Understanding these best practices can help developers avoid common pitfalls and optimize resource utilization to improve the overall user experience.
Performance Optimization Best Practices
JVM performance optimization is critical to ensuring that applications run efficiently and scalably. Here are some key optimization techniques to consider:
By applying these optimization techniques, developers can significantly improve JVM performance, scalability, and reliability. It’s essential to continuously monitor and analyze system performance to identify areas for improvement.
Security Best Practices
Ensuring JVM security is vital to protecting applications from potential threats and vulnerabilities. Here are some key security best practices:
By following these security best practices, developers can significantly reduce the risk of security breaches and ensure the integrity and confidentiality of user data.
Monitoring JVM Metrics
Monitoring JVM metrics is crucial to understanding system performance, identifying potential issues, and optimizing resource utilization. Here are some essential metrics to monitor:
By regularly monitoring JVM metrics, developers can diagnose performance issues, optimize resource utilization, and enhance overall user experience.
Ensuring JVM Security
Ensuring JVM security is critical to protecting applications from potential threats and vulnerabilities. Here are some essential security measures to implement:
li>Use signed JARs: Use signed JARs to prevent unauthorized modification or tampering of application code.
By implementing these security measures, developers can significantly reduce the risk of security breaches and ensure the integrity and confidentiality of user data.
JVM Future Developments
The Java Virtual Machine (JVM) has been a cornerstone of the Java ecosystem for decades, and its future developments hold significant implications for the performance and security of Java applications. As the JVM continues to evolve, we can expect to see advancements in areas such as performance optimization, security enhancements, and improvements to garbage collection.
Advancements in Garbage Collection
Recent developments in garbage collection technology have led to significant improvements in JVM performance. One such advancement is the introduction of Shenandoah, a low-pause-time garbage collector designed to minimize pause times and improve throughput. Shenandoah achieves this by using a concurrent garbage collection algorithm and leveraging multi-core processors to accelerate garbage collection.
Another area of focus is the ongoing development of ZGC, a high-performance garbage collector aimed at Java 11 and later. ZGC targets the goal of garbage collection pause times below 1 ms, even for large heaps. To achieve this, ZGC employs a variety of innovative techniques, including concurrent mark-and-sweep, concurrent reference processing, and a new card table architecture.
Improved Performance Optimization
In addition to advancements in garbage collection, the JVM is also focusing on performance optimization techniques. One such initiative is the ongoing development of GraalVM, a high-performance runtime designed to accelerate Java and other languages. GraalVM achieves this by leveraging just-in-time compilation, caching, and other performance optimization techniques.
Another area of focus is the development of C2, a performance-focused compiler for the JVM. C2 aims to provide significant performance improvements over previous compilers by employing advanced techniques such as loop fusion, register allocation, and dead code elimination.
Enhanced Security Features
As the JVM continues to evolve, security is becoming an increasingly important area of focus. One such development is the introduction of Ahead-of-Time (AOT) compilation, a feature designed to prevent malicious code from being executed within the JVM. AOT compilation achieves this by converting Java bytecode into native machine code, which is then executed directly without the need for interpretation by the JVM.
Another area of focus is the development of the Proguard native-image tool, designed to create custom images that can be executed without the need for the JVM. This provides an added layer of security, as the native image cannot be reversed engineered or manipulated by malicious actors.
Future Release Expectations
Looking ahead to future JVM releases, we can expect to see significant advancements in performance, security, and other areas. One such area of focus is the ongoing development of Project Panama, a series of features aimed at improving the performance and functionality of the JVM.
Project Panama includes several key features, including the development of a new JVM-based library interface, improved support for direct memory access, and enhanced performance characteristics. These features are expected to provide significant benefits for Java developers, including improved performance, increased security, and easier integration with other languages.
Real-Life Impact and Examples
The advancements and developments discussed above are expected to have a significant impact on real-world applications and use cases. For example, the introduction of Shenandoah and ZGC is expected to revolutionize the way Java applications handle garbage collection, providing significant benefits for performance-critical applications.
Similarly, the development of GraalVM and C2 is expected to provide significant performance improvements for Java applications, particularly those that require high-performance execution. The introduction of Ahead-of-Time compilation and the Proguard native-image tool are expected to provide added security and stability for Java applications.
Overall, the future developments and advancements in the JVM ecosystem hold significant implications for Java developers and users around the world. As the JVM continues to evolve and improve, we can expect to see significant benefits in terms of performance, security, and functionality.
End of Discussion

In conclusion, the Java Virtual Machine is a powerful tool that enables platform independence and a wide range of security features. By understanding how the JVM works, developers can write more efficient and effective code, and take full advantage of the benefits that Java has to offer. Whether you’re a seasoned developer or just starting out, the JVM is an essential part of your toolkit.
FAQs
Q: What is the purpose of the Java Virtual Machine?
The primary purpose of the JVM is to execute Java bytecode on a variety of devices, providing platform independence and a wide range of security features.
Q: How does the JVM achieve platform independence?
The JVM provides a layer of abstraction between the Java code and the underlying hardware, allowing the same code to run on different platforms without modification.
Q: What are some of the benefits of using the JVM?
Some of the benefits of using the JVM include platform independence, security features, and a wide range of tools and libraries for development.