Linux windows virtual machine –
As Linux Windows Virtual Machine takes center stage, this opening passage beckons readers into a world crafted with good knowledge, ensuring a reading experience that is both absorbing and distinctly original.
A Virtual Machine (VM) allows you to run an operating system on top of another operating system. This concept is crucial for developers and system administrators who need to test or run multiple operating systems on a single machine.
What is a Virtual Machine (VM) in the Context of Linux and Windows?

A virtual machine (VM) is a software emulation of a physical computer, which creates a separate environment for the operating system (OS) to run within. This allows multiple operating systems to run on the same physical hardware, increasing flexibility and reducing the need for dedicated hardware for each OS. The concept of virtualization, where multiple virtual machines can run on a single physical host, has become increasingly popular in recent years, particularly with the rise of cloud computing and virtualization technologies like VMware, VirtualBox, and Hyper-V.
Concept of Virtual Machines
VMs use a combination of hardware and software components to create a virtual environment that mimics a physical machine. The hypervisor, also known as the virtual machine monitor (VMM), is the software layer that sits between the physical hardware and the guest operating system. The hypervisor manages the resources of the physical host and provides a virtualized platform for the guest OS to run on. The guest OS, in turn, is installed on a virtual machine, which is a self-contained environment that includes a virtual hardware platform, such as a virtual CPU, memory, and storage.
Purpose of Virtual Machines
VMs serve several key purposes:
- Hardware virtualization: VMs allow multiple OSes to run on a single physical host, reducing hardware costs and increasing flexibility.
- Portability: VMs enable OS migration and deployment across different physical hosts, making it easier to manage and maintain OS environments.
- Resource optimization: VMs allow for efficient resource allocation and utilization, as multiple OSes can share the same physical resources.
- Test and development: VMs provide a cost-effective and controlled environment for testing and developing software, reducing the risk of affecting the host system.
When using VMs, you can quickly spin up a new environment for testing or development, and easily clone it for reuse or backup purposes, thereby simplifying the management of OS environments, especially for projects that demand a high level of flexibility and portability.
Advantages of Virtual Machines, Linux windows virtual machine
VMs have numerous advantages, including:
- Improved resource utilization: VMs allow multiple OSes to share physical resources, maximizing utilization and reducing waste.
- Enhanced portability: VMs enable OS migration and deployment across different physical hosts, making it easier to manage and maintain OS environments.
- Increased flexibility: VMs allow for rapid deployment and resizing of OS environments, making it easier to respond to changing business needs.
- Reduced costs: VMs reduce hardware costs by allowing multiple OSes to run on a single physical host.
- Improved security: VMs provide a high level of isolation between guest OSes, reducing the risk of OS-level security breaches.
VMs can significantly improve the efficiency and scalability of your IT infrastructure, enabling you to quickly adapt to changing business requirements and minimize the time and cost associated with IT management and maintenance.
Software Requirements for Running Virtual Machines on Linux and Windows: Linux Windows Virtual Machine
To run virtual machines on Linux and Windows, you need to have certain software tools installed on your computer. These tools enable your system to create and manage virtual machines, which are essentially software-emulated hardware platforms that run their own operating systems.
One of the most critical software tools for running virtual machines is a hypervisor. A hypervisor, also known as a virtual machine monitor (VMM), is a piece of software that creates and manages virtual machines. It sits between the host operating system and the guest operating system, allowing multiple virtual machines to run on a single physical machine. Some popular hypervisors include VMware, VirtualBox, and Hyper-V.
Popular Hypervisors for Virtual Machines
The following table lists some of the most popular hypervisors for running virtual machines on Linux and Windows.
| Hypervisor | Description | Compatibility |
| — | — | — |
| VMware | A commercial hypervisor developed by VMware. | Windows, Linux, macOS |
| VirtualBox | A free and open-source hypervisor developed by Oracle. | Windows, Linux, macOS, Solaris |
| Hyper-V | A virtualization platform developed by Microsoft. | Windows, Linux (with modifications) |
Each hypervisor has its own set of features, advantages, and disadvantages. For example, VMware is a highly scalable and secure hypervisor, but it requires a significant amount of system resources. VirtualBox, on the other hand, is a lightweight and free hypervisor that is suitable for developers and testing environments.
Software Compatibility for Virtual Machines
When choosing a hypervisor, it’s essential to consider the software compatibility of the guest operating system with the host operating system. Some guest operating systems may require specific drivers or software packages to function correctly on a particular host operating system.
For example, Linux guests may require a different set of drivers and software packages to function on a Windows host operating system. Similarly, Windows guests may require specific software packages to function on a Linux host operating system.
In some cases, you may need to install additional software packages or drivers to enable virtualization on your host operating system. For example, some Linux distributions may require you to enable Intel VT-x or AMD-V virtualization technology to run virtual machines.
System Requirements for Running Virtual Machines
Running virtual machines requires a significant amount of system resources, including CPU, memory, and disk space. The system requirements for running virtual machines vary depending on the number of virtual machines, the size of the guest operating system images, and the complexity of the virtualized applications.
As a general rule of thumb, you should have at least 4 GB of RAM and a 64-bit processor to run virtual machines. However, the actual system requirements may be higher depending on your specific use case.
Creating and Configuring Virtual Machines for Linux and Windows
Creating a virtual machine and configuring its settings is a straightforward process. VirtualBox and VMware Workstation are popular options for running virtual machines on Linux and Windows. First, you need to create a new virtual machine by specifying the guest operating system, RAM, CPU, and storage. This sets the foundation for a functional and efficient virtual machine.
Creating a New Virtual Machine
To create a new virtual machine, follow these steps:
- Launch the virtualization software (VirtualBox or VMware Workstation) on your host machine.
- Click on the “New” button to create a new virtual machine.
- Choose the guest operating system from the available options.
- Specify the amount of RAM and CPU cores for the virtual machine.
- Select the storage option, such as a virtual hard disk or a physical disk, and allocate the necessary space.
When creating a new virtual machine, it’s essential to consider the resources required by the guest operating system. Allocating sufficient RAM and CPU cores ensures smooth performance of the virtual machine.
Configuring Virtual Machine Settings
Configuring virtual machine settings involves optimizing performance, networking, and storage. Networking settings control how the virtual machine communicates with the host machine and the outside world.
- Networking settings include options for bridged, NAT, and host-only networking.
- Bridged networking allows the virtual machine to access the host machine’s network.
- NAT networking provides the virtual machine with access to the host machine’s network, but with a private IP address.
- Host-only networking isolates the virtual machine from the host machine’s network.
When configuring virtual machine settings, it’s crucial to consider the specific needs of the guest operating system and the virtual machine’s intended use.
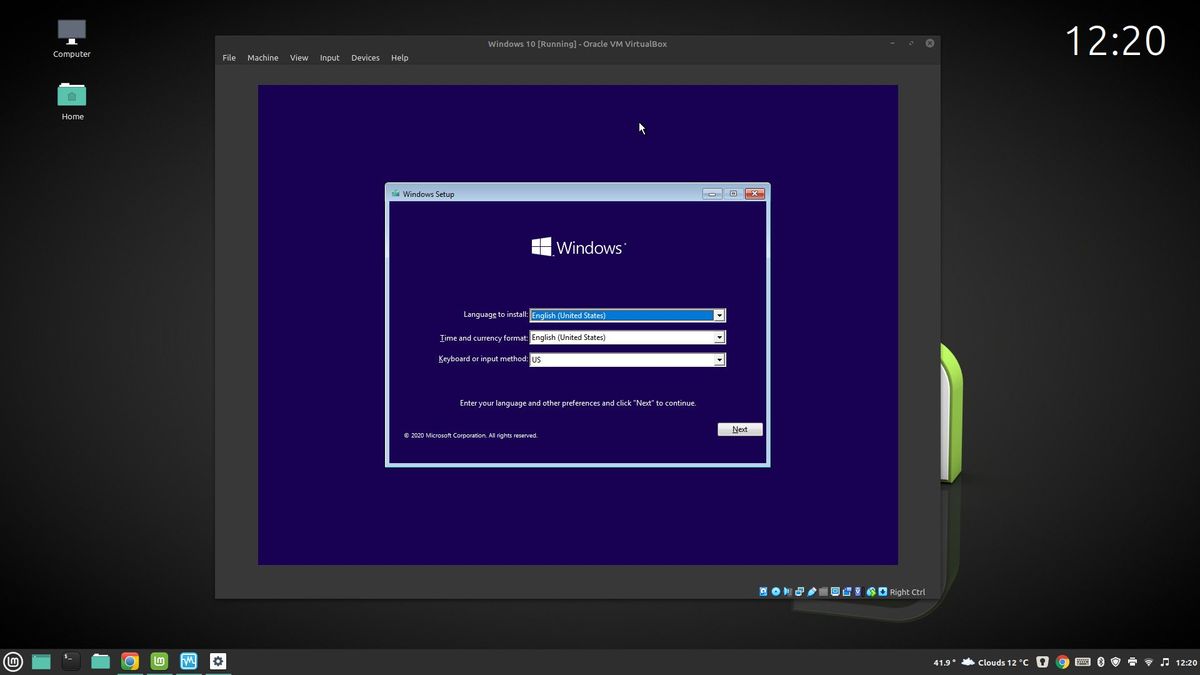
Installing a Guest Operating System
Installing a guest operating system on a virtual machine is similar to installing an operating system on a physical machine. The installation process typically involves creating a bootable installation media, such as a USB stick or a CD/DVD, and then running the installation wizard.
- Download the guest operating system ISO file.
- Launch the virtual machine and insert the bootable installation media.
- Follow the installation wizard to complete the installation process.
When installing a guest operating system, it’s essential to follow the installation wizard’s instructions carefully to ensure a successful installation.
Optimizing Virtual Machine Performance
Optimizing virtual machine performance involves adjusting settings to maximize performance, reduce lag, and prevent crashes.
- Adjust the virtual machine’s RAM and CPU settings to ensure adequate resources.
- Enable hardware virtualization to take advantage of the host machine’s hardware features.
- Disable unnecessary devices and services to reduce resource utilization.
When optimizing virtual machine performance, it’s crucial to identify and address any bottlenecks or resource constraints to ensure smooth operation.
Key Benefits and Challenges of Using Virtual Machines for Linux and Windows
Using virtual machines for Linux and Windows has numerous benefits for individuals and organizations. Virtual machines provide flexibility, isolation, and portability, which are essential for modern computing. They also enable seamless testing, development, and deployment of operating systems and applications.
Main Advantages of Virtual Machines
Virtual machines offer several advantages, including:
-
Isolation and Security
Virtual machines provide a high level of isolation between the host and guest operating systems, ensuring that any malware or viruses in the guest OS do not affect the host OS. This ensures a secure environment for testing and development.
- Portability and Compatibility: Virtual machines can run on any hardware platform, regardless of the underlying architecture, making them highly portable and compatible with different environments.
- Flexibility and Scalability: Virtual machines can be easily created, cloned, and deleted, allowing for rapid deployment and testing of different operating systems and applications. They can also be scaled up or down as needed, making them ideal for resource-intensive applications.
- Ease of Use: Virtual machines are relatively easy to set up and manage, even for those without extensive technical knowledge. Many virtualization software packages come with intuitive controls and GUIs that simplify the process.
Common Challenges of Using Virtual Machines
While virtual machines offer numerous benefits, they also have some challenges. Some of the most common challenges include:
-
Performance Overhead
Virtual machines can introduce a performance overhead due to the additional layer of abstraction required to run the guest OS. This can result in slower performance compared to running the OS natively.
- Resource Requirements: Virtual machines require significant system resources, including RAM, CPU, and storage, which can impact the host system’s performance if not properly managed.
- Networking and File System Challenges: Virtual machines can have difficulty accessing the host system’s network adapters and file systems, which can make it challenging to transfer data between the host and guest OS.
- Compatibility Issues: Virtual machines can have compatibility issues with certain operating systems or applications, which can make it difficult to run certain software or games.
Strategies for Overcoming Common Challenges
To overcome the challenges associated with virtual machines, it’s essential to employ effective strategies. Some of these strategies include:
- Choosing the right virtualization software package that meets your specific needs and requirements.
- Optimizing the host system’s resources to ensure that virtual machines can run smoothly and efficiently.
- Implementing proper networking and file system configurations to enable seamless data transfer between the host and guest OS.
- Testing and validating virtual machines to ensure compatibility with specific operating systems and applications.
By understanding the benefits and challenges of using virtual machines and employing effective strategies to overcome common challenges, users can get the most out of their virtual machine infrastructure, improve efficiency, and ensure a successful experience.
Security Considerations for Virtual Machines Running on Linux and Windows
Virtual machines, whether running on Linux or Windows, can provide a high degree of security due to their isolated environment. However, this isolation is only as good as the security measures implemented to protect the virtual machine from unauthorized access and potential security risks. In this section, we will discuss the potential security risks and threats faced by virtual machines and provide guidance on how to secure and protect them.
Potential Security Risks and Threats
Virtual machines are not immune to security risks and threats, including, but not limited to:
- Unauthorized access: Virtual machines can be vulnerable to unauthorized access, especially if the hypervisor or virtualization software is not properly configured or if the virtual machine is not properly secured.
- Privilege escalation: In a virtual machine, an attacker could potentially gain elevated privileges, allowing them to access sensitive data or disrupt system operations.
- Data leakage: Virtual machines can leak sensitive data, such as encryption keys or authentication credentials, if not properly secured or if the virtual machine is not properly isolated from the host system.
- Malware: Virtual machines can be infected with malware, which can spread to other virtual machines or the host system, causing significant damage to the system or data.
To mitigate these risks, it is essential to implement proper security measures, including:
- Secure configuration: Properly configure the hypervisor or virtualization software to ensure secure isolation of the virtual machine.
- Access controls: Implement access controls, such as authentication and authorization policies, to prevent unauthorized access to the virtual machine.
- Data encryption: Encrypt sensitive data stored within the virtual machine to prevent data leakage.
- Regular updates: Regularly update the virtual machine and guest operating system to ensure the latest security patches and updates are applied.
Best Practices for Configuring Virtual Machine Security
To configure virtual machine security effectively, consider the following best practices:
- Use a secure hypervisor: Choose a reputable and secure hypervisor that provides robust security features, such as encryption and access controls.
- Implement network segregation: Segregate the virtual machine network from the host system network to prevent unauthorized access or data leakage.
- Use a secure virtual switch: Use a secure virtual switch to isolate the virtual machine network from the physical network.
- Maintain a backup: Regularly back up the virtual machine to prevent data loss in the event of a security breach or system failure.
- Regularly monitor: Regularly monitor the virtual machine and host system for suspicious activity or security threats.
Additional Security Measures
To further enhance virtual machine security, consider implementing additional measures, such as:
- Firewalls: Implement firewalls to prevent unauthorized access to the virtual machine.
- Intrusion detection and prevention systems: Implement intrusion detection and prevention systems to detect and prevent potential security threats.
- Security software: Install and regularly update security software, such as antivirus and anti-spyware, to prevent malware infections.
- Biometric authentication: Use biometric authentication, such as fingerprints or facial recognition, to enhance access controls and prevent unauthorized access.
Ultimate Conclusion
In conclusion, Linux Windows Virtual Machine is a powerful tool that offers flexibility and convenience. By understanding the advantages and disadvantages of using virtual machines, you can make informed decisions about your development and system administration needs.
FAQ Compilation
Q: Can I run multiple operating systems on a single virtual machine?
A: Yes, you can run multiple operating systems on a single virtual machine using a feature called “nested virtualization.” However, this may reduce the performance of the virtual machine.
Q: How do I choose the right hypervisor for my needs?
A: The choice of hypervisor depends on your specific requirements, such as the operating system you’re running, the level of performance you need, and the security features you require.
Q: Can I transfer a virtual machine from one host to another?
A: Yes, you can transfer a virtual machine from one host to another using a feature called “export” and “import.” This allows you to easily move your virtual machine to a different physical location.
Q: How do I secure my virtual machine from unauthorized access?
A: To secure your virtual machine, you should use a strong password, enable encryption, and set up a firewall to restrict access to the virtual machine.