SSH into Windows Machine sets the stage for secure remote access, offering readers a glimpse into a story that is rich in detail and original from the outset.
The world of remote computing has made our lives easier, but it also raises concerns about security and reliability. In this article, we will walk you through the process of SSH into a Windows machine, discussing the basics, preparation, and advanced topics.
SSH Basics
SSH, or Secure Shell, is a secure protocol for remote access to devices over the internet. Its purpose is to provide a secure way to access and manage devices remotely, without compromising the security of the device or the network. This is particularly important for devices connected to the internet, as they can be vulnerable to unauthorized access and attacks. The use of SSH has become widespread due to its ease of use, flexibility, and versatility.
Difference between SSH and other remote access protocols
While other remote access protocols, such as Telnet, provide a way to access devices remotely, they do not offer the same level of security as SSH. SSH uses encryption to protect data, including passwords and commands, from eavesdropping and tampering. This ensures that even if an attacker intercepts the connection, they will not be able to access the data or commands being transmitted.
SSH also differs from other protocols in its use of keys for authentication. SSH keys are a pair of digital keys used to authenticate users and devices, without the need for passwords. This is more secure than password-based authentication, as keys are generated and stored securely, and the risk of key guessing or brute-force attacks is significantly reduced.
Importance of SSH keys in secure remote access
SSH keys are an essential part of secure remote access using SSH. Keys are generated using algorithms, such as RSA or DSA, and consist of a private key and a public key. The private key is stored securely on the client-side, while the public key is stored on the server-side. This allows the client to authenticate itself to the server without the need for a password.
SSH keys are more secure than passwords in several ways:
*
- Passwords can be easily guessed or cracked using brute-force attacks, whereas ssh keys are virtually unguessable.
- Passwords can be stolen or intercepted, while secure ssh keys are generated and stored securely.
- Passwords can be compromised due to weak password policies, while ssh keys are resistant to password-related security issues.
SSH key benefits include:
- Fast and reliable connections: SSH keys allow for fast and reliable connections between devices, without the need for password authentication.
- Improved security: SSH keys are more secure than passwords, reducing the risk of unauthorized access and attacks.
- Easy to use: SSH keys are easy to use, with no need to remember complex passwords or usernames.
SSH is widely used and supported:
SSH is widely supported by most operating systems, including Windows, Linux, and macOS, making it easily accessible and usable.
Choosing an SSH Client
When it comes to accessing your Windows machine via SSH, you’ll need to select a suitable SSH client. This decision is crucial as it will impact your overall security, compatibility, and user experience. There are several popular SSH clients available for Windows, each with its own strengths and weaknesses.
Popular SSH Clients for Windows
Some of the most well-known SSH clients for Windows include:
PuTTY is often considered the gold standard for SSH clients on Windows, with a large user base and extensive feature set.
-
PuTTY
PuTTY is a popular open-source SSH client for Windows, offering advanced features such as multiple session support, public key authentication, and support for various network protocols.
- PuTTY is a great option for users who require advanced SSH features and customization options.
- However, due to its complexity and steep learning curve, PuTTY may not be ideal for beginners or users who prefer a more straightforward experience.
-
OpenSSH
OpenSSH is another widely used SSH client for Windows, offering robust security features, a user-friendly interface, and compatibility with various platforms.
- OpenSSH provides secure connections, with features such as key-based authentication, encryption protocols, and secure data transmission.
- OpenSSH also supports various protocols, including SSHv1, SSHv2, and SFTP, making it compatible with a wide range of systems.
-
Windows Subsystem for Linux (WSL)
WSL allows users to run a Linux environment natively within Windows 10, offering a seamless integration of Linux tools and commands with Windows.
- WSL eliminates the need for separate SSH clients, as users can simply use the native Linux tools and commands within the Windows environment.
- This makes WSL an attractive option for developers, power users, and administrators who rely heavily on Linux tools and workflows.
- Complexity: Some SSH clients, like PuTTY, offer a wide range of advanced features, which can be beneficial for power users but overwhelming for beginners.
- Security Features: As with any security-related tool, it’s essential to consider the level of security offered by the SSH client, including features such as encryption protocols and key-based authentication.
- Compatibility: Ensure that the chosen SSH client supports the necessary protocols and is compatible with your target systems.
- User Interface: Consider the user experience and interface of the SSH client, as this can significantly impact your productivity and overall satisfaction.
- Upon initial login, the user copies the public key to their host machine, which then uses this key to verify the user’s private key, ensuring authorized access.
- After the initial setup, when the user attempts to log in, their client application encrypts a session ID with their private key, transmitting the encrypted session ID to the server.
- The server decrypts this ID with the stored public key, if it matches the stored public key, the user’s identity is confirmed.
- CA-signed certificates: These certificates are issued by a trusted CA and contain the client’s public key and identity information.
- Client-certificates: These certificates are used by clients to authenticate with an SSH server.
- Password policies: SSH servers can be configured to enforce complex password policies, such as minimum password length and complexity requirements.
- Password rotation: Regular password rotation can help prevent password compromise, making it harder for attackers to gain access to the system.
- Password authentication protocols: SSH servers can be configured to use stronger password authentication protocols, such as password authentication protocol (PAP) or challenge handshake authentication protocol (CHAP).
- Public key algorithms: SSH servers can be configured to use various public key algorithms, such as RSA or elliptic curve cryptography (ECC).
- Private key management: SSH clients need to manage their private keys securely, using techniques such as encrypted storage and secure password management.
- DH key exchange: This algorithm is widely used in SSH connections and provides a high level of security.
- ECDH key exchange: This algorithm is more secure than DH and provides a higher level of security.
- To use SSH sessions with remote desktop or VPS connections, simply save the connection details as a session in your SSH client.
- Next, when you connect to the remote environment, use the SSH client to log in to the remote server or desktop.
- Once connected, you can use the remote desktop or VPS to access your files, applications, and resources, just as you would on a local machine.
- To use SSH sessions for background processes, first save the connection details as a session in your SSH client.
- Next, create a script or command that you want to run in the background, and upload it to the remote server.
- Using the SSH client, connect to the remote server and use the `ssh-agent` command to run the script or command in the background.
- Incorrect Credentials: Double-check your SSH client configuration, username, and password or private key. Ensure that the SSH server is configured to use the same authentication method (e.g., username/password or public key).
- Incorrect Private Key: Verify that you’re using the correct private key pair, and the private key is properly configured on the client-side.
- SSH Server Configuration: Check the SSH server configuration to ensure it’s set up to allow public key authentication and that the authorized_keys file is correctly configured.
- Permissions Issues: Ensure that the SSH daemon has the correct permissions to access the private key and authorized_keys file.
- Network Congestion: Check the network congestion and ensure that the network connections are stable. You can use tools like `iperf` or `tcpdump` to diagnose network issues.
- Firewall Rules: Verify that the firewalls and access control lists (ACLs) are not blocking SSH traffic. Ensure that the SSH server is configured to allow incoming connections on the correct port.
- DNS Resolution Issues: Check the DNS resolution of the SSH server’s hostname or IP address. You can use tools like `dig` or `nslookup` to diagnose DNS resolution problems.
- SSH Server Port: Ensure that the SSH server is listening on the correct port (standard SSH port is 22).
- SSH Server Availability: Use tools like `ssh` or `ssh -o` to verify the server’s availability and check if it’s responsive.
- Log Files: Check the SSH server’s log files (e.g., `/var/log/auth.log` or `/var/log/secure`) for any error messages or clues that may indicate what’s causing the issue.
- System Resources: Verify that the SSH server has the necessary system resources, such as CPU, memory, and disk space.
- ssh -v: Use the `-v` option with `ssh` to enable verbose mode and get detailed information about the SSH connection process.
- ssh -vv: Use the `-vv` option to get even more detailed information about the SSH connection process.
- ssh -vvv: Use the `-vvv` option to get the most detailed information about the SSH connection process.
- SFTP is based on the FTP (File Transfer Protocol) protocol but uses SSH for authentication and encryption. It provides a high-level API for interacting with remote file systems.
- SCP, on the other hand, is a simple protocol that allows you to transfer files securely using SSH.
- The `sftp` command is used to access an SFTP server, while `scp` is used to transfer files between two local or remote hosts.
- For example, to transfer a file from your local machine to a remote machine using SCP, you would use the command: `scp local_file.txt user@remote_host:remote_directory/`
- SSH tunneling works by establishing a secure connection between the two hosts and then forwarding traffic from one host to the other.
- The `ssh` command can be used to create a tunnel, which can be used to forward traffic from a remote host to a local host, and vice versa.
- For example, to create an SSH tunnel from your local machine to a remote host, you would use the command: `ssh -L 8080:localhost:80 user@remote_host`
- Port forwarding allows you to forward traffic from a specific port on the local host to a different port on the remote host.
- The `ssh` command can be used to forward traffic from a remote host to a local host, and vice versa.
- For example, to forward traffic from port 80 on the local host to port 8080 on the remote host, you would use the command: `ssh -L 8080:localhost:80 user@remote_host`
Factors Influencing the Choice of SSH Client
Several factors should be considered when selecting an SSH client, including:
Installing and Configuring the Selected SSH Client
Once you’ve selected the suitable SSH client, the installation and configuration process varies depending on the chosen tool. For example:
* To install PuTTY, simply download and run the installer.
* For OpenSSH, you’ll need to install the Windows Subsystem for Linux (WSL), which includes OpenSSH.
* WSL is pre-installed with Windows 10, making it easily accessible.
Please note that this is not an exhaustive guide and it is recommended to consult the official documentation for each SSH client for more detailed installation and configuration instructions.
SSH Connection Methods
SSH connections rely on secure authentication and key exchange processes to ensure data integrity. In this context, we’ll delve into the fundamental connection methods.
In SSH, two primary methods for establishing connections are available:
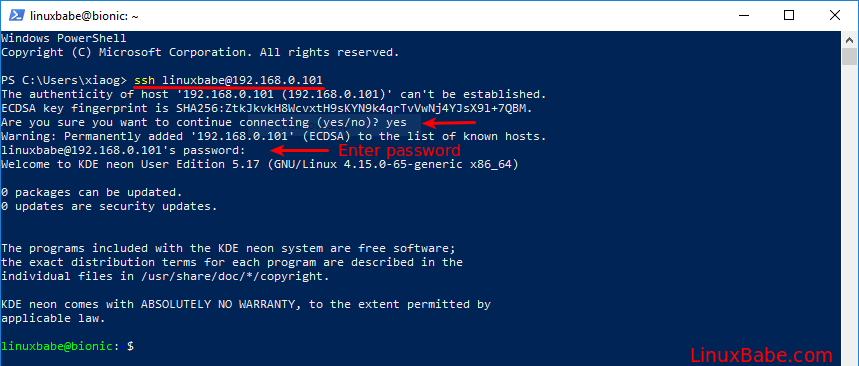
SSH Password Authentication
SSH password authentication is the most straightforward method, where the client sends a username and password to the server for verification. This method involves three main steps:
–
The Handshake
The SSH handshake is the initial connection establishment, where the client initiates communication with the server. The process involves negotiating protocol versions and algorithms for encryption and key exchange.
–
Key Exchange
Key exchange is a fundamental aspect of SSH connections. In this process, both sides negotiate a shared secret key to facilitate secure communication. Key exchange can be achieved using algorithms like Diffie-Hellman or Elliptic Curve Diffie-Hellman.
–
Authentication
Authentication is the final step in the SSH connection process. Upon successful key exchange, the client and server engage in a process of mutual authentication, ensuring both parties agree on the identity and permissions of the user.
Besides SSH password authentication, there are other key exchange and authentication methods, like public key authentication. This method relies on public and private key pairs to establish secure connections. When public key authentication is used, the client provides the server with a public key, which the server verifies against a locally stored private key.
However, for users unfamiliar with public key authentication, password authentication offers an easier, albeit less-secure initial entry into SSH connections.
A different method is also available,
SSH public key authentication
Public key authentication relies on the RSA or DSA (Digital Signature Algorithm) algorithms to create a pair of keys: a public key and a private key.
Another connection method is SFTP (Secure File Transfer Protocol), which, although related to SSH, has some key differences from SSH connections.
SSH and SFTP connections
SSH focuses on secure remote access and command-line execution, whereas SFTP is specifically tailored for file transfers. While SFTP connections can be established using SSH protocols, they serve distinct purposes.
A fundamental aspect distinguishing SSH and SFTP is the protocol’s core functionality:
– SSH establishes a channel for executing remote commands and executing local files or executing remote files.
– SFTP transfers data over a Secure Shell session.
Difference in key exchange and authentication
Although both SSH and SFTP share a similar authentication mechanism, SSH focuses on authenticating users for command execution and file access, whereas SFTP emphasizes secure data transfer.
Summary of the SSH connection process
To recap the key aspects of an SSH connection:
– The client starts with a handshake.
– Next, they establish a shared secret key through key exchange.
– Finally, both parties undergo a process of mutual authentication, verifying the client’s identity.
Difference between SSH and SFTP
Although they coexist, SSH and SFTP connections fulfill different purposes:
– SSH provides secure remote access and command execution.
– SFTP is specifically designed for secure file transfer.
Securing SSH Connections
Secure SSH connections are crucial for protecting sensitive data and preventing unauthorized access to your systems. To achieve this, you need to implement robust security measures, including the use of certificates, passwords, and public key authentication.
Certificate-Based Authentication
Certificate-based authentication is a widely used method for securing SSH connections. In this approach, an SSH client uses a certificate provided by a trusted certification authority (CA) to authenticate with an SSH server. This method provides a high level of security, as the client’s identity is verified before accessing the server.
Certificate-based authentication is particularly useful in environments where a high level of security is required, such as in financial institutions or government agencies.
Password-Based Authentication
Password-based authentication is a simple and widely used method for securing SSH connections. In this approach, the SSH client is prompted to enter a password to access the SSH server. This method is easy to implement but may not be as secure as other methods, as passwords can be compromised through various means.
While password-based authentication provides a basic level of security, it is essential to implement additional security measures, such as public key authentication, to enhance overall security.
Public Key Authentication
Public key authentication is a highly secure method for securing SSH connections. In this approach, the SSH server uses a pair of keys, one public and one private, to authenticate the client. This method provides a high level of security, as the client’s identity is verified using the public key.
Public key authentication is particularly useful in environments where a high level of security is required, such as in financial institutions or government agencies.
SSH Encryption
SSH encryption is crucial for protecting sensitive data transmitted between an SSH client and server. SSH encryption methods, such as AES (Advanced Encryption Standard) and Blowfish, provide a high level of security, making it difficult for attackers to intercept or compromise the data.
The encryption key is derived from the key exchange algorithm and the authentication method used.
Key Exchange Algorithms
Key exchange algorithms are used to negotiate a shared secret key between an SSH client and server. Key exchange algorithms, such as Diffie-Hellman (DH) and elliptic curve Diffie-Hellman (ECDH), provide a high level of security, making it difficult for attackers to compromise the shared secret key.
In conclusion, securing SSH connections requires the implementation of robust security measures, including certificate-based, password-based, and public key authentication, as well as SSH encryption and key exchange algorithms.
Managing SSH Sessions
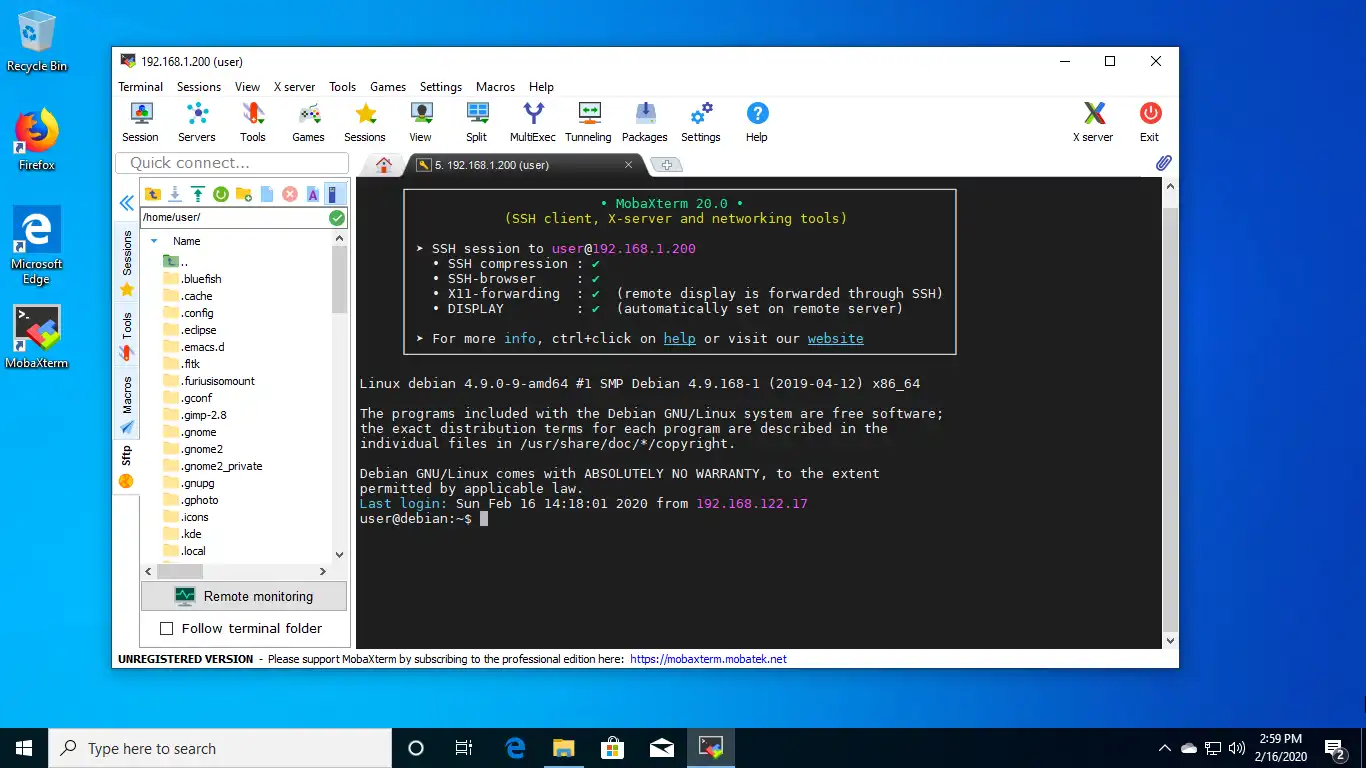
Managing multiple SSH connections can be a daunting task, but fortunately, many SSH clients provide features to simplify the process. With the ability to open tabs, sessions, and background connections, you can efficiently manage multiple connections and reduce the risk of accidental disconnections or lost work.
Managing Multiple SSH Connections
Most SSH clients allow you to open multiple connections in tabs or separate windows. This feature is especially useful if you need to work with multiple servers or projects simultaneously. By opening each connection in a separate tab, you can easily switch between them and avoid cluttering your screen with multiple windows.
SSH clients like PuTTY, SSH Terminal, and iTerm2 offer tab management features, allowing you to easily switch between connections and manage multiple tabs.
To take advantage of this feature, simply right-click (or Ctrl-click on Mac) on a tab and select “New Tab” or use the keyboard shortcut to open a new tab. You can also use the “Sessions” feature to save frequently used connections and easily recall them later.
Using SSH Sessions with Remote Desktop or VPS (Virtual Private Server) Connections
SSH sessions can be used with remote desktop or VPS connections to provide an additional layer of security and flexibility. By using SSH to connect to a remote desktop or VPS, you can ensure that your connection is encrypted and secure, even if you’re accessing the remote environment over a public network.
Benefits of Using SSH Sessions for Background Processes
SSH sessions can also be used to run background processes, such as scheduled tasks or continuous integration workflows. By using SSH to connect to a remote server, you can run scripts or commands in the background, freeing up your local machine’s resources and ensuring that your processes run smoothly and efficiently.
The `ssh-agent` command allows you to run SSH connections in the background, freeing up your local machine’s resources and ensuring that your processes run smoothly and efficiently.
Troubleshooting SSH Issues

Troubleshooting SSH issues can be frustrating, especially when a connection hangs or authentication fails. Don’t worry! We’ve got you covered. In this section, we’ll walk you through common SSH connection issues, methods for resolving them, and best practices for troubleshooting SSH connections.
Authentication Failures
Authentication failures are one of the most common SSH issues. They occur when the client and server cannot verify each other’s identities. This can lead to failed login attempts and frustration. To resolve authentication failures, we need to look at the following:
Network Connectivity Problems, Ssh into windows machine
Network connectivity problems are another common issue when troubleshooting SSH connections. These issues can arise due to various reasons, such as network congestion, firewall rules, or DNS resolution problems.
Checking Server Status
Before diving into troubleshooting SSH issues, it’s essential to check the server status. This includes verifying the SSH server’s availability, checking its log files, and ensuring that the server has the necessary system resources.
Using SSH Debugging Tools
SSH debugging tools can help you identify and resolve SSH connection issues. These tools provide detailed information about the SSH connection process and can help you pinpoint the root cause of the problem.
Advanced SSH Topics on Windows Machine: Ssh Into Windows Machine
SSH is a powerful protocol for secure remote access and communication. In addition to simple SSH connections, there are several advanced topics that can help you utilize SSH to its full potential on a Windows machine.
SSH File Transfer and Synchronization
SSH file transfer and synchronization are essential for many use cases, such as data transfer, backup, and automation. There are two primary ways to transfer files using SSH: SFTP (Secure File Transfer Protocol) and SCP (Secure Copy).
SSH Tunneling for Secure Communication
SSH tunneling allows you to create a secure connection between two hosts by forwarding network traffic through an SSH connection. This is useful for accessing resources that are only available on the local network, such as websites or services.
SSH Port Forwarding and Redirection
SSH port forwarding and redirection are related to SSH tunneling but are more focused on forwarding specific ports and redirecting traffic.
Closing Summary
In conclusion, SSH into a Windows machine is a powerful tool for secure remote access. By following the steps Artikeld in this article, you can set up a secure connection and enjoy the benefits of remote computing.
Query Resolution
Q: What is SSH and why do I need it?
A: SSH, or Secure Shell, is a secure protocol that allows you to access a remote machine securely over the internet. You need it for secure remote access and file transfer.
Q: What is the difference between SSH and SFTP?
A: SSH is a secure protocol for remote access, while SFTP (Secure File Transfer Protocol) is a protocol for secure file transfer.
Q: How do I secure my SSH connection?
A: You can secure your SSH connection by using public key authentication, certificates, and strong passwords.