This Build of Vanguard Cannot Run on Untrusted Machines, so you won’t be able to play it on public computers or your mates’ old laptops. Vanguard is a game that requires a super secure environment to run smoothly, and your friends’ computers are probably not trustworthy.
In this article, we’ll explain why Vanguard can’t run on untrusted machines, the risks of playing it on public computers, and how you can keep your account safe.
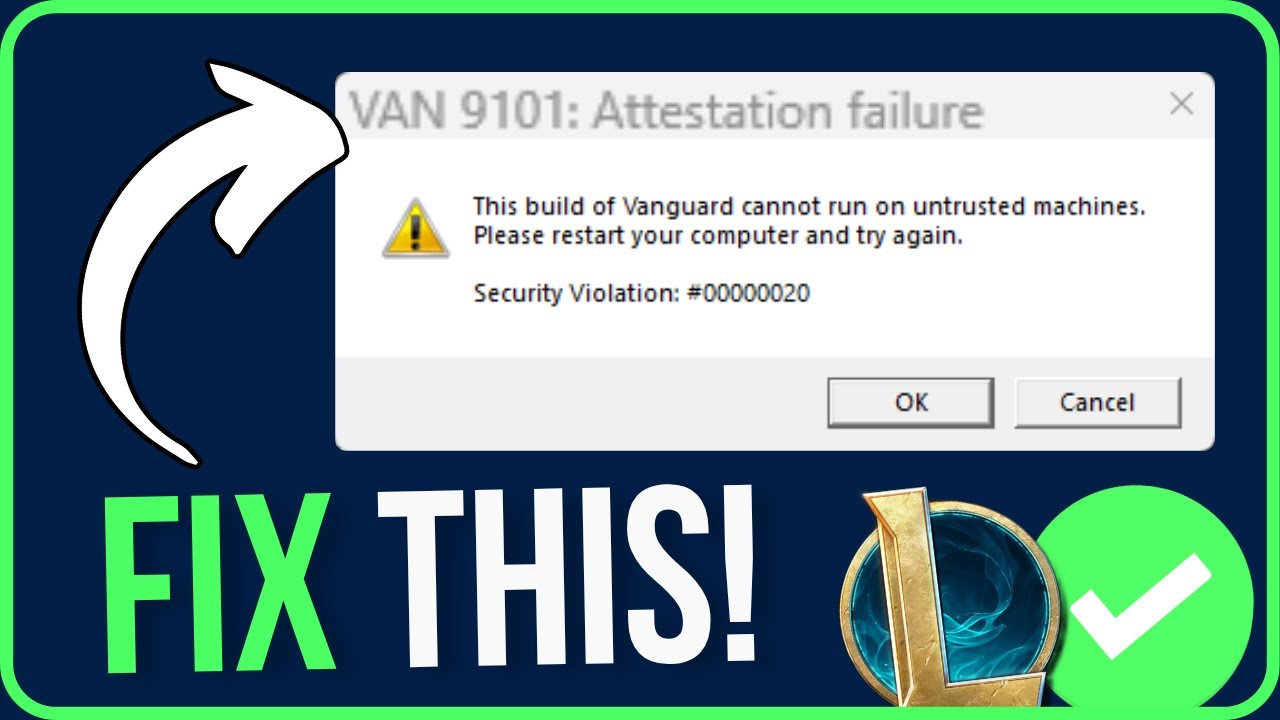
Understanding the Error Message
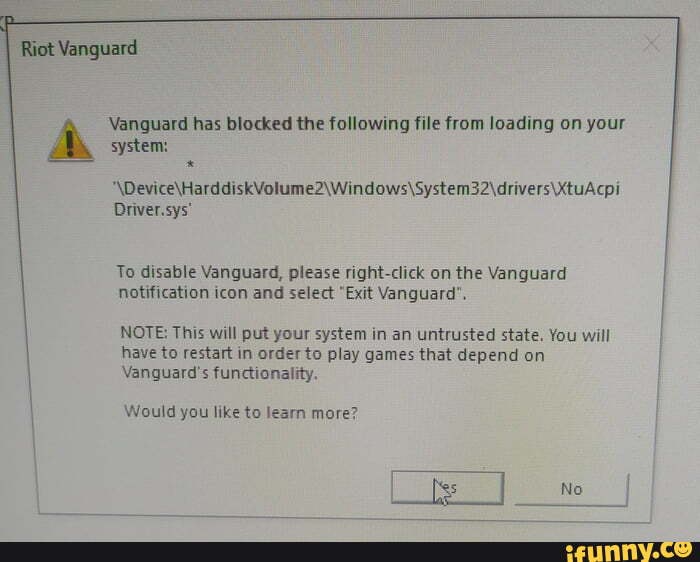
This error message indicates that the current build of Vanguard cannot be executed on a machine whose security level is considered untrusted. Vanguard is a digital title that relies heavily on online authentication and validation to function properly, making it highly susceptible to security threats. When Vanguard detects that it’s running on an untrusted machine, it refuses to launch as a precautionary measure to protect the game and its users from potential security risks.
Reasons for this Error
When Vanguard detects that it’s running on an untrusted machine, it typically results from one of several reasons:
The machine is running on an operating system that is not officially supported by the game.
The machine’s security settings are configured to block the game from running.
The game’s authenticity could not be verified due to a missing or corrupted configuration file.
Operating systems not officially supported by the game may pose security risks to Vanguard and its users. Always ensure your operating system is up-to-date and running a supported version.
Risks of Running Vanguard on Untrusted Machines
Running Vanguard on an untrusted machine exposes the game and its users to the following risks:
Malware infections: Untrusted machines may have malware that can inject malicious code into the game, compromising its security and potentially stealing user data.
Data tampering: Malicious actors may attempt to modify game data or files on an untrusted machine, disrupting the user’s experience and potentially leading to account bans.
- Malicious actors may inject malware into the game that can steal user credentials or sensitive information.
- Users may inadvertently download malware by running Vanguard on an untrusted machine, which can compromise their entire computer system.
Examples of Situations Where this Error May Occur, This build of vanguard cannot run on untrusted machines
The following scenarios may result in Vanguard being unable to run on an untrusted machine:
A user’s computer is connected to a public Wi-Fi network and Vanguard is attempting to authenticate online.
A user is running Vanguard on a virtual machine or a cloud-based operating system that is not officially supported by the game.
A user has a compromised or outdated operating system that Vanguard’s security measures detect as a potential threat.
A user’s security software or firewall settings block Vanguard’s ability to connect to the online servers due to a false positive or misconfigured rule.
Security Requirements of Vanguard
Securely implementing Vanguard on trusted machines is crucial for a seamless and protected experience. The requirements for security differ significantly between trusted and untrusted machines, as Vanguard employs stringent security protocols to safeguard sensitive information and functionality.
One essential aspect of Vanguard’s security is its reliance on trusted machines. These machines must meet specific security requirements, which include:
Vanguard’s Security Requirements for Trusted Machines
To establish a secure connection with Vanguard, trusted machines must meet the following criteria:
- The machine should be running on a version of the operating system that is compatible with Vanguard.
- The machine should have up-to-date security patches and updates installed to prevent any potential vulnerabilities from being exploited.
- The machine should be configured with a secure browser, capable of handling sensitive information and secure connections.
- The machine should have a reliable and secure network connection, free from malware and other security threats.
Vanguard’s security measures are designed to protect sensitive information from unauthorized access. However, if a trusted machine fails to meet these security requirements, the consequences can be severe, including data breaches, system compromise, and unauthorized access. These consequences highlight the importance of adhering to security requirements for trusted machines.
The difference between Vanguard’s security measures for trusted and untrusted machines lies in the level of verification and validation. Trusted machines undergo rigorous verification and validation to ensure their security, whereas untrusted machines rely on more basic security protocols. This distinction is critical in maintaining the integrity of Vanguard’s functionality and information security.
To understand the impact of not meeting security requirements for Vanguard, consider the potential consequences of data breaches or system compromise on the organization or individual using Vanguard. These consequences include financial losses, reputational damage, and even legal liabilities.
Vanguard’s security requirements and protocols are designed to prevent these consequences by ensuring the integrity of sensitive information and functionality. By adhering to these requirements, trusted machines can securely interact with Vanguard, safeguarding the confidentiality, integrity, and availability of sensitive information.
In Vanguard, encryption is used to protect data in transit and at rest. The system employs end-to-end encryption to ensure that data is only accessible to authorized parties, adding an additional layer of security.
Confidentiality, Integrity, and Availability (CIA) are the three primary security principles in Vanguard.
The system’s security architecture ensures that access to sensitive information and functionality is restricted to authorized users and machines, thereby preventing unauthorized access, malicious activities, and other security threats.
For trusted machines to securely interact with Vanguard, they must meet the security requirements mentioned earlier, including up-to-date security patches, a secure browser, and a reliable network connection.
In summary, Vanguard’s security requirements and protocols are designed to protect sensitive information and functionality from unauthorized access, malicious activities, and other security threats. By adhering to these requirements, trusted machines can securely interact with Vanguard, safeguarding confidentiality, integrity, and availability.
Trusted Machine Requirements
To ensure a secure environment for Vanguard software, a machine must meet specific system requirements. A trusted machine is one that has been properly configured to avoid potential security risks and maintain the integrity of the software.
Minimum System Requirements
A machine must meet the following minimum system requirements to be considered trusted:
- The operating system should be up-to-date, with the latest service pack installed.
- The hardware should be capable of performing well with the software, with a minimum of 8 GB of RAM and a 2.4 GHz processor.
- A stable internet connection of at least 1 Mbps, and a reliable power source are also essential.
A stable and well-configured machine ensures that the Vanguard software runs smoothly and efficiently, while also maintaining optimal performance.
Up-to-Date Operating System and Software Installations
An up-to-date operating system and software installations are crucial for maintaining a trusted environment. A well-configured operating system helps prevent security vulnerabilities, while also ensuring optimal performance.
Patches and updates should be installed regularly to avoid potential security risks.
A well-maintained machine also helps prevent software incompatibilities and performance issues.
Antivirus Software and Firewalls
A reputable antivirus software and a strong firewall are essential components of a trusted machine. Antivirus software helps protect against malware, ransomware, and other types of cyber threats, while a firewall prevents unauthorized access to the machine and its data.
A reputable antivirus software should be installed on the machine at all times.
A strong firewall helps prevent unauthorized access to the machine and its data, thereby ensuring the security and integrity of the Vanguard software.
The importance of antivirus software and firewalls cannot be overstated, as they provide a critical layer of protection against various types of cyber threats.
Best Practices for Maintaining Trusted Machines: This Build Of Vanguard Cannot Run On Untrusted Machines

Maintaining a trusted machine environment is crucial for ensuring the security and integrity of sensitive data, particularly in environments where data protection and compliance are critical, such as in finance, healthcare, and government sectors. A trusted machine environment ensures that machines are free from malware, viruses, and other malicious software that could compromise the confidentiality, integrity, and availability of sensitive data.
Implementing Strong Access Controls
Access controls are critical in preventing unauthorized access to machines, networks, and data. Implementing strong access controls, such as multi-factor authentication, role-based access control, and least privilege access, helps to ensure that only authorized personnel have access to machines and sensitive data.
- Multifactor authentication adds an additional layer of security, making it more difficult for attackers to gain unauthorized access to machines and data.
- Role-based access control ensures that users are granted access to resources based on their job functions and responsibilities.
- Least privilege access restricts users to only the privileges they need to perform their job functions, reducing the risk of data breaches and unauthorized access.
Many organizations, such as the US Department of Defense and the National Security Agency (NSA), implement strong access controls as a best practice for maintaining a trusted machine environment.
Keeping Software Up-to-Date
Keeping software up-to-date is critical in maintaining a trusted machine environment. Outdated software may contain known vulnerabilities that can be exploited by attackers to gain unauthorized access to machines and data. Implementing regular software updates and patches helps to ensure that machines are protected from known vulnerabilities.
- Regular software updates and patches help to address known vulnerabilities and prevent attacks.
- Outdated software may contain known vulnerabilities that can be exploited by attackers to gain unauthorized access to machines and data.
- Maintaining a patch management system helps to ensure that all software is up-to-date and patched, reducing the risk of data breaches and unauthorized access.
Examples of companies that have implemented regular software updates and patches include Google, Microsoft, and Amazon Web Services (AWS). These companies regularly update their software to address known vulnerabilities and ensure the security and integrity of their machines and data.
Regularly Monitoring Machines and Networks
Regularly monitoring machines and networks helps to detect and respond to potential security threats in real-time. Implementing a threat detection system, such as intrusion detection and prevention systems (IDPS) and security information and event management (SIEM) systems, helps to identify potential security threats and prevent attacks.
- Regularly monitoring machines and networks helps to detect and respond to potential security threats in real-time.
- IDPS and SIEM systems help to identify potential security threats and prevent attacks.
- A threat detection system helps to identify and respond to security threats, reducing the risk of data breaches and unauthorized access.
Examples of companies that have implemented regular monitoring and threat detection systems include JPMorgan Chase, Bank of America, and Citigroup. These companies regularly monitor their machines and networks to detect and respond to potential security threats.
Last Recap
In conclusion, playing Vanguard on untrusted machines is a big no-no. To stay safe, make sure to play it on a computer you control, and always keep your software up to date.
Questions Often Asked
Q: What are untrusted machines?
A: Untrusted machines are computers that are not secure, either because they’re old, have malware, or have been hacked.