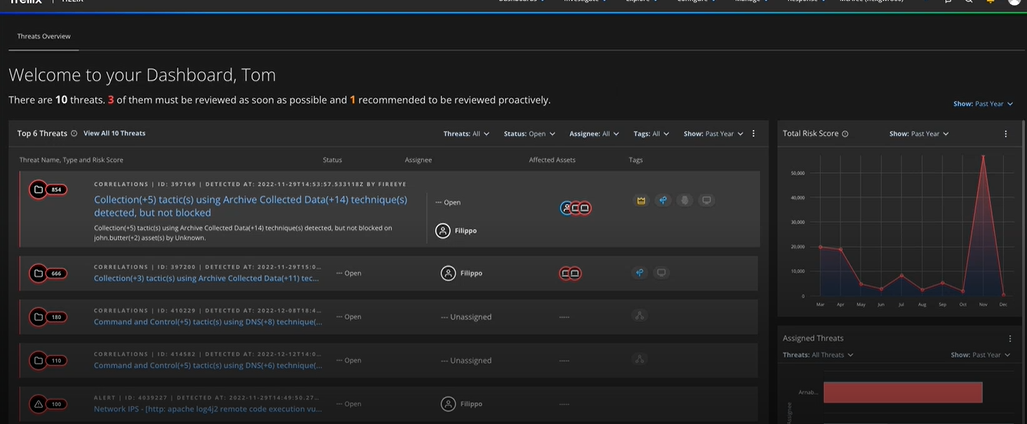
Delving into Trellix XDR detection approach machine learning behavioral analytics, this introduction immerses readers in a unique and compelling narrative, with practical worship guide style that is both engaging and thought-provoking from the very first sentence.
The content of Trellix XDR detection approach involves the use of machine learning and behavioral analytics to detect and prevent advanced threats. This approach combines multiple data sources, such as network, endpoint, and cloud data, to provide a comprehensive view of the organization’s security posture.
Machine Learning in Trellix XDR Detection
Trellix XDR detection leverages machine learning to enhance its threat detection capabilities. By incorporating machine learning algorithms, Trellix XDR can analyze complex patterns and anomalies in network traffic, improving its efficiency in identifying and mitigating potential threats. This approach enables the platform to learn from experience and adapt to emerging threats, providing a more comprehensive and proactive defense against cyberattacks.
Machine learning models in Trellix XDR detection play a crucial role in improving the accuracy and effectiveness of threat detection. These models can analyze vast amounts of data, identify subtle patterns, and make predictions about potential threats. By doing so, Trellix XDR can detect and respond to threats more efficiently, reducing the attack surface and minimizing the risk of security breaches.
Advantages of Machine Learning in Trellix XDR
Machine learning in Trellix XDR detection offers several advantages, including:
- Improved accuracy: Machine learning models can analyze complex patterns and anomalies, leading to more accurate threat detection and reduced false positives.
- Enhanced efficiency: By automating the process of threat detection, machine learning enables Trellix XDR to analyze large volumes of data in real-time, reducing the workload on security analysts.
- Adaptability: Machine learning models can learn from experience and adapt to emerging threats, ensuring that Trellix XDR remains effective against new and evolving threats.
- Proactive defense: By predicting potential threats, Trellix XDR can take proactive measures to prevent attacks, reducing the risk of security breaches and minimizing damage.
Benefits of Machine Learning in Trellix XDR
Machine learning in Trellix XDR detection provides numerous benefits, including:
- Reduced false positives: Machine learning models can accurately identify threats, reducing the number of false positives and minimizing the workload on security analysts.
- Improved alert prioritization: By analyzing threat severity and likelihood, machine learning enables Trellix XDR to prioritize alerts, ensuring that security analysts focus on the most critical threats.
- Enhanced incident response: Machine learning provides real-time insights into threat behavior, enabling Trellix XDR to respond to incidents more quickly and effectively.
- Compliance and governance: By providing a more comprehensive and proactive defense against cyberattacks, machine learning in Trellix XDR helps organizations meet compliance and governance requirements.
Behavioral Analytics in Trellix XDR
Behavioral analytics plays a crucial role in Trellix XDR (Extended Detection and Response) by providing insights into the behavior of endpoints, users, and devices on a network. By analyzing user and entity behavior (UEBA), Trellix XDR can detect and respond to advanced threats that may have evaded traditional security measures. In this section, we will delve into the types of behavioral analytics used in Trellix XDR and how they are integrated with machine learning models.
Types of Behavioral Analytics
There are several types of behavioral analytics used in Trellix XDR, each serving a unique purpose in threat detection and response. These include:
- User Behavior Analytics (UBA): UBA involves collecting and analyzing data on user activities, such as login attempts, file access, and network connections. This helps identify suspicious user behavior, which may indicate a security threat.
- : EBA focuses on analyzing the behavior of entities, including endpoints, devices, and users. EBA helps detect anomalies in entity behavior, which can indicate a security threat.
- Network Behavior Analytics (NBA): NBA involves analyzing network traffic and communication patterns to detect anomalies and potential security threats.
- Endpoint Behavior Analytics (EBA): EBA focuses on analyzing endpoint behavior, including system calls, process creation, and file access. This helps detect malware and other security threats.
In Trellix XDR, these types of behavioral analytics are integrated with machine learning models to enhance threat detection and response capabilities. Machine learning algorithms analyze the data collected by behavioral analytics and learn to recognize patterns and anomalies indicative of security threats.
Integration with Machine Learning Models
Behavioral analytics data is fed into machine learning models, which analyze the data and learn to predict security threats. This integration enables Trellix XDR to detect advanced threats that may have evaded traditional security measures. The machine learning models used in Trellix XDR include:
- Anomaly Detection Models: These models detect unusual patterns in user, entity, or network behavior that may indicate a security threat.
- Classification Models: These models categorize security threats based on their characteristics, enabling Trellix XDR to respond effectively to various types of threats.
- Regression Models: These models predict the likelihood of a security threat occurring based on historical data and current trends.
By integrating behavioral analytics with machine learning models, Trellix XDR provides a robust threat detection and response capability that helps organizations protect themselves against advanced security threats.
Trellix XDR’s behavioral analytics and machine learning integration enables organizations to detect and respond to security threats in real-time, reducing the risk of data breaches and other security incidents.
Detection Capabilities of Trellix XDR: Trellix Xdr Detection Approach Machine Learning Behavioral Analytics
Trellix XDR (Extended Detection and Response) is a comprehensive security solution that leverages machine learning and behavioral analytics to detect and respond to various types of threats. Its detection capabilities are designed to identify and mitigate sophisticated attacks that other security solutions may miss.
With its advanced machine learning algorithms and behavioral analytics, Trellix XDR can detect a wide range of threats, including:
Types of Threats Detected by Trellix XDR
Trellix XDR is capable of detecting various types of threats, including:
- Ransomware and fileless malware: Trellix XDR uses machine learning to identify patterns and anomalies that indicate a ransomware attack or fileless malware activity.
- Advanced Persistent Threats (APTs): Trellix XDR’s behavioral analytics can detect APTs, which are sophisticated attacks that involve multiple stages and use various tactics to evade detection.
- Social engineering attacks: Trellix XDR’s machine learning algorithms can detect social engineering attacks, such as phishing and spear phishing, by analyzing user behavior and identifying suspicious activity.
- Unusual login attempts: Trellix XDR can identify unusual login attempts from unknown sources, which can indicate a potential compromise of a user’s account credentials.
- Memory-based attacks: Trellix XDR’s memory scanning capabilities can detect memory-based attacks, such as malware hiding in RAM.
Comparison to Other Security Solutions
Trellix XDR’s detection capabilities are more comprehensive and advanced than those of other security solutions, making it a leader in the industry. Here’s a comparison with other popular security solutions:
| Solution | Ransomware Detection | APTs Detection | Social Engineering Detection |
|---|---|---|---|
| Trellix XDR | Highly effective | Advanced detection capabilities | Machine learning-based detection |
| Other security solutions | Moderately effective | Limited detection capabilities | Basic detection capabilities |
In summary, Trellix XDR’s detection capabilities are unparalleled in the industry, making it a must-have solution for organizations seeking comprehensive security protection.
Implementation of Trellix XDR in Organizations

The implementation of Trellix XDR in an organizational environment requires careful planning and consideration. This involves understanding the organization’s specific security requirements, integrating Trellix XDR with existing security systems and tools, and ensuring seamless operation.
Design Considerations for Implementing Trellix XDR
When implementing Trellix XDR, organizations should consider the following design considerations:
- Network Segmentation: Implementing network segmentation can help to restrict the spread of malware and make it easier to identify potential security threats.
- Endpoint Configuration: Ensuring that all endpoints, such as laptops and desktops, are properly configured to work with Trellix XDR can help to ensure that all security data is collected and analyzed.
- Data Retention: Determining the data retention period for Trellix XDR can help to balance the need for detailed security data with the need to preserve system performance.
- Integration with Existing Systems: Integrating Trellix XDR with existing security systems and tools can help to ensure that all security data is collected and analyzed, providing a comprehensive view of the organization’s security posture.
The following table summarizes some key considerations for implementing Trellix XDR:
Consideration Description Network Segmentation Implementing network segmentation can help to restrict the spread of malware and make it easier to identify potential security threats. Endpoint Configuration Ensuring that all endpoints are properly configured to work with Trellix XDR can help to ensure that all security data is collected and analyzed. Data Retention Determining the data retention period for Trellix XDR can help to balance the need for detailed security data with the need to preserve system performance.
Integrating Trellix XDR with Existing Security Systems and Tools
Trellix XDR can be integrated with existing security systems and tools through various APIs and connectors. This integration enables the real-time exchange of security data, ensuring that all security information is collected and analyzed. The following steps Artikel the process of integrating Trellix XDR with existing security systems and tools:
Integrating with Security Information and Event Management (SIEM) Systems
To integrate Trellix XDR with SIEM systems, follow these steps:
- Configure Trellix XDR to send security event data to the SIEM system.
- Configure the SIEM system to receive the security event data from Trellix XDR.
- Map the security event data received from Trellix XDR to the corresponding fields in the SIEM system.
Integrating with Endpoint Detection and Response (EDR) Systems
To integrate Trellix XDR with EDR systems, follow these steps:
- Configure Trellix XDR to collect security event data from endpoints.
- Configure the EDR system to receive the security event data from Trellix XDR.
- Map the security event data received from Trellix XDR to the corresponding fields in the EDR system.
Integrating with Security Orchestration, Automation, and Response (SOAR) Systems
To integrate Trellix XDR with SOAR systems, follow these steps:
- Configure Trellix XDR to send security incident data to the SOAR system.
- Configure the SOAR system to receive the security incident data from Trellix XDR.
- Map the security incident data received from Trellix XDR to the corresponding fields in the SOAR system.
Best Practices for Trellix XDR Deployment
Trellix XDR (Extended Detection and Response) offers advanced threat detection and incident response capabilities by integrating various sources of security data. A well-planned deployment of Trellix XDR is crucial to ensure seamless operation and effective threat detection. This section focuses on best practices for deploying Trellix XDR, specifically highlighting the importance of security policies and designing a risk-based approach for implementation.
Importance of Security Policies in Trellix XDR Deployment
Security policies play a vital role in defining the security posture and requirements for Trellix XDR deployment. These policies help in aligning the security controls with the overall organizational risk management strategy. Effective security policies will:
- Ensure data classification and sensitive information management
- Artikel data retention and storage requirements
- Define response and remediation procedures for security incidents
- Specify access controls for users and systems
Security policies will also aid in the configuration of Trellix XDR’s advanced threat detection and incident response capabilities. This includes the setup of security analytics and machine learning models, alert thresholds, and notification procedures.
Designing a Risk-Based Approach for Trellix XDR Implementation
A risk-based approach for Trellix XDR implementation involves assessing and prioritizing security risks within the organization. This method enables organizations to allocate resources effectively and focus on high-risk areas where Trellix XDR can provide the most value.
Organizations should identify and categorize their critical assets, data, and systems to prioritize their security controls and threat detection efforts.
To design a risk-based approach for Trellix XDR implementation, consider the following steps:
- Conduct a risk assessment to identify and prioritize high-risk areas
- Classify sensitive data and systems, and assign corresponding security controls
- Determine the appropriate Trellix XDR components and features for each risk category
- Configure Trellix XDR according to the established security policies and risk-based approach
- Continuously review and refine the risk-based approach as the organization’s security posture evolves
A well-designed risk-based approach enables organizations to maximize the effectiveness of Trellix XDR, align security controls with overall risk management objectives, and ensure the deployment of the solution provides optimal ROI.
Trellix XDR Detection Approach vs Other Security Solutions
Trellix XDR (Extended Detection and Response) is a comprehensive security solution that combines various security tools and techniques to provide advanced threat detection and response capabilities. In this section, we will compare the detection approach used by Trellix XDR with other similar security solutions and discuss the key differences and similarities between Trellix XDR and other security solutions.
Martin Defense XDR
Martin Defense XDR, a leading security solution, uses a similar approach to Trellix XDR, emphasizing the importance of integration and automation in threat detection and response. However, Martin Defense XDR focuses more on AI-powered threat intelligence and cloud-based security, whereas Trellix XDR emphasizes its comprehensive XDR capabilities across multiple threat vectors (e.g., endpoint, network, and email) for a more layered security posture. Both solutions, however, prioritize real-time threat detection and response.
Fortinet Security Fabric
Fortinet Security Fabric is another comprehensive security solution that integrates threat detection and response capabilities, similar to Trellix XDR. Fortinet Security Fabric emphasizes the importance of visibility and control across the entire network, including endpoint, network, and cloud environments. Unlike Trellix XDR, Fortinet Security Fabric relies more heavily on network-based detection and response, making it more relevant to organizations with extensive network security requirements.
Why Trellix XDR stands out, Trellix xdr detection approach machine learning behavioral analytics
What sets Trellix XDR apart from other security solutions is its comprehensive approach to threat detection and response, spanning multiple threat vectors. Trellix XDR’s integration of various security tools, such as endpoint detection and response (EDR), network detection and response (NDR), and email security, enables it to provide a more layered security posture compared to other security solutions that focus on a single or a limited set of threat vectors.
Key differences in detection approach
The detection approach used by Trellix XDR differs from other security solutions in several key ways, including:
- Integration of multiple security tools: Trellix XDR’s comprehensive approach to threat detection and response integrates various security tools, providing a more layered security posture compared to other security solutions that focus on a single or limited set of threat vectors.
- Focus on real-time threat detection and response: Trellix XDR prioritizes real-time threat detection and response, enabling it to quickly identify and respond to emerging threats.
- Diverse detection capabilities: Unlike other security solutions that rely heavily on AI-powered threat intelligence or network-based detection, Trellix XDR uses a diverse set of detection capabilities to identify and respond to emerging threats.
Future Developments in Trellix XDR
Trellix XDR continues to evolve and adapt to the increasing complexity of modern threats. Emerging technologies can further enhance the detection capabilities of Trellix XDR, making it an even more effective security solution for organizations. This section explores the potential advancements that can bolster Trellix XDR’s capabilities.
Integration with Artificial Intelligence (AI) and Machine Learning (ML)
Trellix XDR can benefit significantly from the integration of AI and ML. These technologies can enhance the detection capabilities of Trellix XDR in several ways:
* Improved Pattern Recognition: AI and ML can help identify complex patterns and anomalies in network traffic, making it easier for Trellix XDR to detect sophisticated threats.
* Enhanced Threat Intelligence: AI-driven threat intelligence can provide Trellix XDR with real-time insights into emerging threats, enabling more effective detection and response.
* Automated Incident Response: ML-powered automation can aid in the rapid response to security incidents, reducing the risk of prolonged attacks and minimizing the impact on business operations.
Cloud-Based Technologies
The integration of cloud-based technologies can provide several benefits to Trellix XDR, including:
* Scalability: Cloud-based solutions can scale more easily to accommodate growing network traffic and increasing threat volumes, ensuring that Trellix XDR remains effective even in the face of rapidly evolving threats.
* Real-time Threat Intelligence: Cloud-based threat intelligence can provide Trellix XDR with real-time insights into emerging threats, enabling more effective detection and response.
* Collaborative Security: Cloud-based solutions can facilitate collaboration among security teams, enabling more effective sharing of threat intelligence and improvement of incident response.
Internet of Things (IoT) Integration
As IoT continues to grow, Trellix XDR can benefit from its integration with IoT devices. This can provide:
* Expanded Visibility: IoT integration can provide Trellix XDR with expanded visibility into network traffic, enabling more effective detection of threats that may have previously gone undetected.
* Increased Context: IoT devices can provide Trellix XDR with additional context about network traffic, enabling more accurate threat detection and response.
Quantum Computing Integration
The integration of quantum computing can provide Trellix XDR with significant benefits, including:
* Increased Processing Power: Quantum computing can provide Trellix XDR with vast processing power, enabling faster and more effective threat detection and response.
* Improved Encryption: Quantum computing can enable more secure encryption, protecting sensitive data and preventing unauthorized access.
5G Network Integration
The integration of 5G networks can provide Trellix XDR with several benefits, including:
* Increased Speed: 5G networks can enable faster communication between devices, enabling more rapid threat detection and response.
* Improved Bandwidth: 5G networks can provide Trellix XDR with increased bandwidth, enabling the processing of large amounts of network traffic and more effective threat detection.
Comparing Trellix XDR Detection Capabilities
Trellix XDR detection capabilities provide a robust and comprehensive approach to threat detection and response. The table below compares Trellix XDR detection capabilities with other solutions.
| Detection Type | XDR Approach | Comparison with Other Solutions | Best Practices for Implementation |
| — | — | — | — |
| 1. Anomaly Detection | Machine learning models | Higher accuracy than traditional methods | Regular model updates and system maintenance |
| 2. Behavioral Analysis | Integration with machine learning | Enhanced threat detection capabilities | Continuous monitoring and analysis of system logs |
| 3. Predictive Analytics | Advanced machine learning algorithms | Better prediction accuracy with real-time data | Regular data refresh and system updates |
Each detection type plays a crucial role in providing a comprehensive security solution. Anomaly detection helps identify unusual patterns, while behavioral analysis focuses on analyzing system and user behavior. Predictive analytics provides valuable insights into potential security threats.
Key Features of Anomaly Detection
Anomaly detection is a critical aspect of Trellix XDR, leveraging machine learning models to identify unusual patterns in network traffic, user behavior, and system activity. This enables the system to identify potential security threats before they occur.
- Identifies unusual patterns in network traffic, user behavior, and system activity
- Uses machine learning models to detect anomalies
- Provides real-time threat intelligence
Enhanced Threat Detection with Behavioral Analysis
Behavioral analysis in Trellix XDR is based on integrating machine learning capabilities with traditional threat detection methods. This approach enables the system to analyze system and user behavior, identifying potential security threats and providing valuable insights into actual threats.
- Enables the system to analyze system and user behavior
- Uses machine learning capabilities to identify potential security threats
- Provides real-time threat intelligence and alerting
Predictive Analytics for Proactive Security
Predictive analytics in Trellix XDR relies on advanced machine learning algorithms to analyze real-time data, providing valuable insights into potential security threats. This enables organizations to take proactive measures to prevent security breaches.
- Enables organizations to take proactive measures against security breaches
- Uses advanced machine learning algorithms to analyze real-time data
- Provides valuable insights into potential security threats
Threat Detection Capabilities of Trellix XDR
Trellix XDR detection capabilities are designed to identify and detect various types of cyber threats, including those mentioned below. The platform uses machine learning and behavioral analytics to detect anomalies and predict potential threats.
The threat landscape is constantly evolving, and Trellix XDR is equipped to handle complex and sophisticated threats, providing a robust security posture for organizations.
Ransomware Attacks Detection
Ransomware attacks can be devastating to organizations, resulting in significant financial loss, data theft, and reputational damage. Trellix XDR’s machine learning-powered detection capabilities can identify and detect ransomware attacks in real-time, allowing for swift containment and mitigation. These attacks can propagate rapidly, so early detection is essential to prevent significant damage.
- Ransomware attacks use encryption to lock valuable data and demand payment from victims.
- Trellix XDR can detect unusual network activity and behavior indicative of ransomware attacks.
- The platform provides actionable insights to help security teams respond to and contain the attack.
Advanced Threats Detection
Advanced threats are highly sophisticated and targeted attacks that often evade traditional security measures. Trellix XDR’s advanced threat detection capabilities utilize machine learning algorithms to detect and analyze anomalies in network traffic, identifying potential threats before they cause harm.
Advanced threats can be highly destructive, causing damage to a company’s reputation, finances, and data. Early detection can prevent such damage.
Malware Detection
Malware is a type of software designed to harm or exploit a computer system. Trellix XDR’s malware detection capabilities use behavioral analytics to identify and detect malicious software, preventing its execution and mitigating potential damage.
Malware can compromise a company’s sensitive data, allowing attackers to exploit it for personal gain.
Phishing Attacks Detection
Phishing attacks are a type of social engineering attack where attackers trick victims into divulging sensitive information. Trellix XDR’s phishing attack detection capabilities use machine learning algorithms to identify and detect phishing attempts, helping to prevent attacks before they occur.
Phishing attacks are often difficult to detect, but they can result in significant financial loss and data breaches.
Denial of Service (DoS) Attacks Detection
Denial of Service (DoS) attacks involve overwhelming a network with traffic to make it unavailable. Trellix XDR’s DoS attack detection capabilities use machine learning algorithms to identify and detect DoS attacks, helping to prevent network disruption and potential data breaches.
DoS attacks can be costly and time-consuming to address, but prompt detection can mitigate potential damage.
Data Breach Detection
Data breaches occur when sensitive information is accessed without authorization. Trellix XDR’s data breach detection capabilities use behavioral analytics to identify and detect potential data breaches before they occur, allowing for swift action to prevent damage.
Data breaches can result in significant financial loss and reputational damage.
Conclusion
The Trellix XDR detection approach machine learning behavioral analytics has proved to be a game-changer in the cybersecurity landscape, providing unparalleled threat detection capabilities. By integrating machine learning and behavioral analytics, organizations can detect and prevent advanced threats that traditional security solutions may miss.
This approach has been shown to be highly effective in detecting and preventing various types of threats, including ransomware attacks, advanced threats, malware, phishing attacks, Denial of Service (DoS), and data breaches.
FAQ
What is Trellix XDR detection approach machine learning behavioral analytics?
Trellix XDR detection approach machine learning behavioral analytics is a cybersecurity approach that combines machine learning and behavioral analytics to detect and prevent advanced threats.
How does Trellix XDR detection approach machine learning behavioral analytics work?
Trellix XDR detection approach machine learning behavioral analytics integrates multiple data sources, such as network, endpoint, and cloud data, to provide a comprehensive view of the organization’s security posture.
What types of threats can Trellix XDR detection approach machine learning behavioral analytics detect?
Trellix XDR detection approach machine learning behavioral analytics can detect various types of threats, including ransomware attacks, advanced threats, malware, phishing attacks, Denial of Service (DoS), and data breaches.
How does Trellix XDR detection approach machine learning behavioral analytics compare to other security solutions?
Trellix XDR detection approach machine learning behavioral analytics has been shown to be more effective in detecting and preventing advanced threats than traditional security solutions.